The article analyzes the SecurityMail.chm malware created by the North Korean hacking group Kimsuky, which targets virtual asset users through a malicious CHM file containing embedded PowerShell scripts. The malware uses an ActiveX object to execute Base64-encoded payloads received from a C2 server, aiming to steal cryptocurrency investments. #SecurityMail #Kimsuky #CHMMalware #BitJoker
Keypoints
- SecurityMail.chm is a 1MB malicious CHM file attributed to North Korean threat actor Kimsuky targeting virtual asset users.
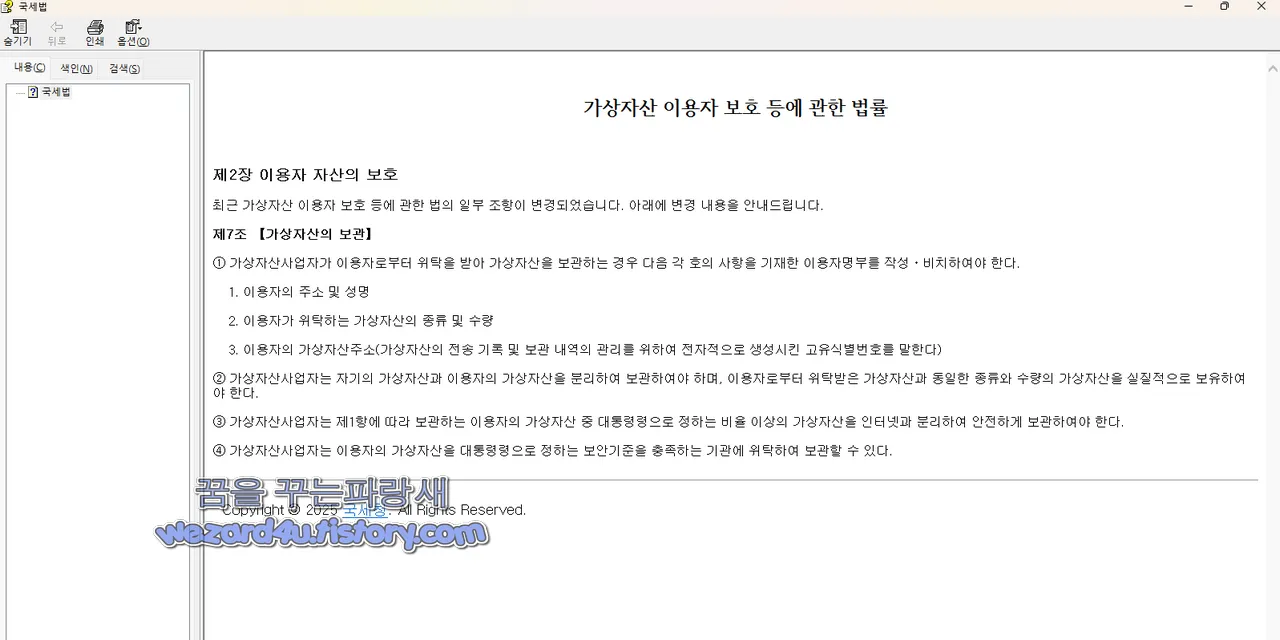
- The CHM file masquerades as information about virtual asset protection laws but contains hidden malicious code starting from line 100 in its HTML content.
- It exploits an ActiveX object (classid:52a2aaae-085d-4187-97ea-8c30db990436) to execute Base64-encoded PowerShell scripts remotely downloaded and decoded using certutil.
- The malware generates shortcut files and executes remote commands via Windows Script Host (wscript), enabling persistent command execution from a C2 server.
- The C2 server URL hxxp://noreplymail.space/BitJoker/bootstrapservice.php has historical connections to the Konni group and has been actively exploited since March 2025.
- The malware creates files such as Link.dat and Link.ini in the user’s Links directory and uses randomized tags in HTTP requests to evade detection.
- This campaign is designed primarily to steal cryptocurrency assets, highlighting the risk to virtual asset investors and limitations of antivirus solutions.
MITRE Techniques
- [T1204] User Execution – The malware is disguised as a legitimate CHM help file containing dummy legal information to lure virtual asset users (“The CHM file masquerades as information about virtual asset protection laws but contains hidden malicious code”).
- [T1129] Execution Through Module Load – Uses an ActiveX object with classid 52a2aaae-085d-4187-97ea-8c30db990436 to execute malicious scripts embedded in the file (“object tag loads an ActiveX object to execute Base64 encoded payloads”).
- [T1059] Command and Scripting Interpreter – Executes Base64 encoded PowerShell scripts decoded by certutil and run through wscript.exe (“PowerShell script executed indirectly via certutil to decode .ini file and wscript to run it”).
- [T1102] Web Service – Malware fetches commands from a remote C2 server URL hxxp://noreplymail.space/BitJoker/bootstrapservice.php to perform Remote Code Execution (“Microsoft.XMLHTTP object requests and executes remote code from C2 server”).
- [T1543] Create or Modify System Process – Generates shortcut files (Link.dat, Link.ini) in user directories to maintain persistence (“Creates shortcut and script files in user’s Links directory to execute commands”).
Indicators of Compromise
- [File Hashes] SecurityMail.chm – MD5: 4599ac1bbe483c73064df1353feafd01, SHA-1: a76af8176da28fdab47f9a77d50eb0e89f2b8557, SHA-256: 7047878f4fbea323148f6554afe616991eb56cc327653972c4213a9017c5e66b
- [Domains] C2 server – noreplymail.space used in URL hxxp://noreplymail.space/BitJoker/bootstrapservice.php, associated with prior Konni activity
- [File Names] Link.dat, Link.ini – Generated in C:UsersuserLinks directory to store decoded payload and execute scripts
- [IP Address] DNS IP 46.202.158.9 linked to the domain noreplymail.space
Read more: http://wezard4u.tistory.com/429504