The article analyzes a malicious code attack by the North Korean hacking group Kimsuky, which exploited a stolen digital certificate from CJ OliveNetworks to target a Korean research institute. The malware demonstrates advanced techniques such as self-modifying code, hardware I/O manipulation, and debugger evasion, impacting CJ OliveNetworks and the Korean research organization. #CJOliveNetworks #Kimsuky
Keypoints
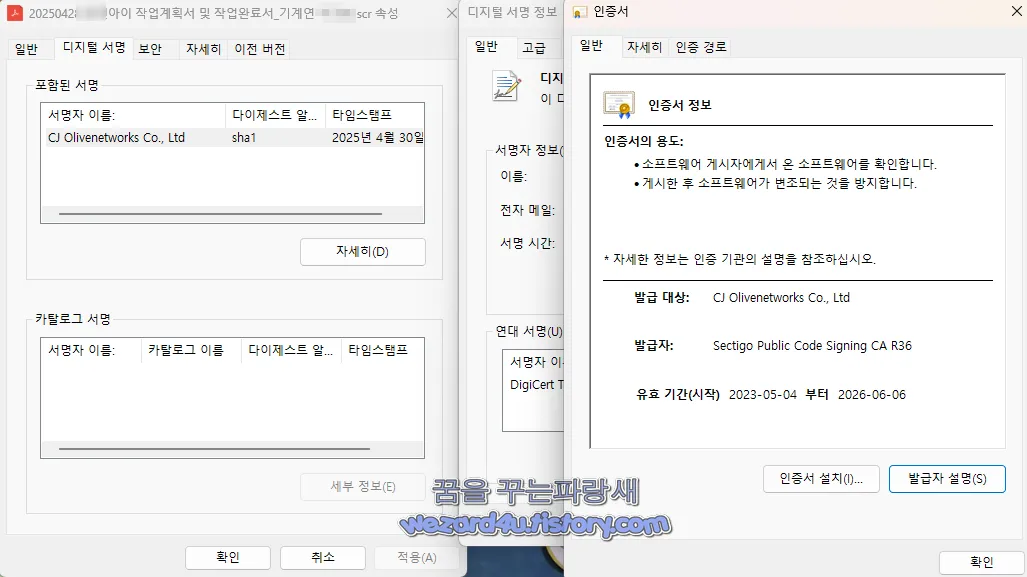
- The malware uses a stolen digital signature issued by Sectigo for CJ OliveNetworks, which was promptly revoked after detection.
- Key malicious file involved: “20250428 플x아이 작업계획서 및 작업완료서_기계연 이x화.scr” sized 6MB with multiple file hashes documented.
- The malware employs self-modifying code that manipulates memory addresses based on carefully calculated input parameters and triggers abnormal termination if debugging conditions are detected.
- Direct hardware communication occurs through dynamically calculated I/O port outputs, likely for debugging detection or hardware-level attacks such as keylogging.
- The code demonstrates advanced obfuscation using bitwise operations, XOR memory encoding, and dynamic function pointer invocation to evade static analysis.
- Multiple subroutines do not return normally, indicating forced process termination or infinite loops to disrupt analysis.
- The analysis identifies potential stack overflow vulnerabilities and exploitation vectors such as shellcode injection and function pointer overwriting.
MITRE Techniques
- [T1071] Application Layer Protocol – The malware communicates via HTTP to a suspicious domain hxxp://gsegse(.)dasfesfgsegsefsede(.)o-r(.)kr/login(.)php, indicating command and control.
- [T1106] Execution through API – Dynamic function pointer calls are made, leveraging virtual function tables for execution flow hijacking (‘param_2[0x1e]에 저장된 함수 포인터를 동적으로 호출’).
- [T1055] Process Injection – The malware manipulates memory and overwrites function pointers on the stack to subvert normal execution flows (‘스택 내부 함수 포인터 덮어쓰기 가능성’).
- [T1204] User Execution – The initial infection vector is a malicious executable file signed with stolen digital certificates that trick users into running the malware.
- [T1562] Impair Defenses – The malware uses debugger evasion techniques, such as conditional abnormal termination on debugger detection (‘조건 충족 시 강제 중단’).
- [T1027] Obfuscated Files or Information – Use of XOR-based runtime decoding and self-modifying code to hide payload content and obstruct static analysis (‘XOR를 이용한 메모리 난독화, self-modifying code’).
- [T1499] Endpoint Denial of Service – Subroutines that do not return normally hint at forced termination or infinite loops to disrupt endpoint operations (‘서브루틴이 반환하지 않음’).
Indicators of Compromise
- [File Hashes] Malicious signed executable with hashes MD5: 7ec88818697623a0130b1de42fa31335, SHA-1: 49fd125c5f516be6883404c256d79afa54dd42d7, SHA-256: 123aefe0734da130b475bfdad6c3ebe49688569ab8310e71ec5252ec46cb67eb
- [File Hashes] Supporting config.dat file with hashes MD5: 580d7a5fdf78dd3e720b2ce772dc77e9, SHA-1: df3e07199e8457341dd06dfa5b04d6a9d45b01c1, SHA-256: 7047efbd15b20086933a3e41f23252d3f8b049b913b2c05af520a3233368f700
- [Domain] Suspicious C2 domain: hxxp://gsegse(.)dasfesfgsegsefsede(.)o-r(.)kr/login(.)php used for control and commands
- [IP Address] Associated IP: 162.220.11.186 linked to suspicious network activity
- [File Name] Malicious executable: “20250428 플x아이 작업계획서 및 작업완료서_기계연 이x화.scr” digitally signed with stolen certificate
Read more: https://wezard4u.tistory.com/429487