ResolverRAT is a newly discovered remote access trojan (RAT) that utilizes advanced evasion techniques and runtime resource resolution to avoid detection. This malware primarily targets employees in the healthcare and pharmaceutical sectors via localized phishing campaigns, employing significant social engineering tactics. Affected: healthcare sector, pharmaceutical sector
Keypoints :
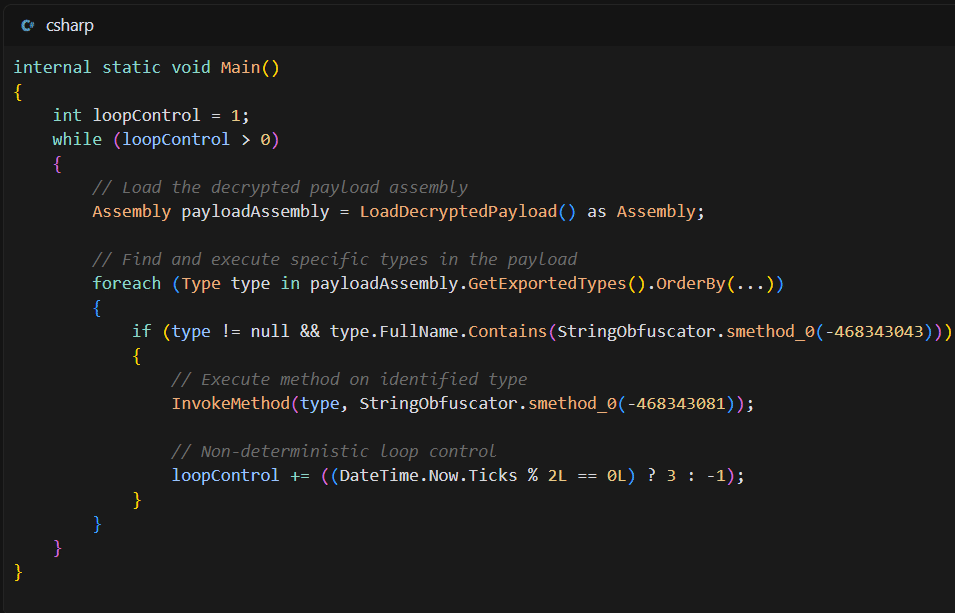
- ResolverRAT employs advanced in-memory execution and dynamic resource handling to evade detection.
- Localized phishing campaigns are tailored to specific countries and languages, increasing credibility and user interaction.
- A classic DLL side-loading technique is used to execute the malware through legitimate software.
- The malware features multiple layers of anti-analysis techniques, making it difficult to reverse-engineer.
- The ResolverRAT utilizes AES-256 encryption for its payload, enhancing security.
- Persistence methods include registry modifications and installing files across various system directories.
- The command-and-control (C2) architecture incorporates resilient IP rotation and certificate pinning to evade detection.
- Morphisec’s Anti-Ransomware Assurance Suite provides protection against ResolverRAT and similar threats.
MITRE Techniques :
- TA0001 – Initial Access: Achieved through social engineering via localized phishing emails.
- TA0002 – Execution: Leveraging DLL side-loading to execute malicious payloads through legitimate applications.
- TA0003 – Persistence: Utilizes registry modifications and file installations across various system directories for persistence.
- TA0005 – Defense Evasion: Implements AES-256 encryption and anti-analysis techniques to prevent detection.
- TA0011 – Command and Control: Employs resilient C2 infrastructure with IP rotation and custom protocols for stealthy communication.
Indicator of Compromise :
- [SHA256] ec189b7ce68cb308139f6a5cf93fd2dc91ccf4432dc09ccaecb9de403a000c73
- [SHA256] 6c054f9013c71ccb7522c1350995066ef5729371641a639a7e38d09d66320bf4
- [SHA256] c3028a3c0c9b037b252c046b1b170116e0edecf8554931445c27f0ddb98785c1
- [C2 IP] 38.54.6.120
- [C2 IP] 192.30.241.106
Full Story: https://www.morphisec.com/blog/new-malware-variant-identified-resolverrat-enters-the-maze/