Netskope Threat Labs uncovered a complex multi-stage attack chain executed by the DOGE Big Balls ransomware, a variant of Fog ransomware, leveraging custom PowerShell scripts, open-source tools, vulnerable drivers, and the Havoc red team framework. The infection involves sophisticated persistence mechanisms, lateral movement, and credential dumping, often hosted and updated through Netlify, posing significant risks to targeted networks. #DOGEBigBalls #FogRansomware #Havoc #Mimikatz #Rubeus
Keypoints
- Netskope Threat Labs identified new scripts and binaries linked to DOGE Big Balls ransomware utilizing custom and open-source tools like Mimikatz, Rubeus, and Havoc.
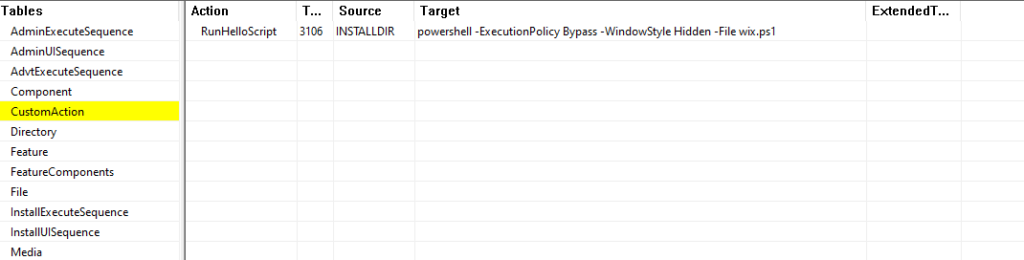
- The initial infection starts via a payload named payload.msi which executes encoded PowerShell scripts embedding persistence and download mechanisms.
- The attack chain disables Windows Defender, establishes persistence through registry Run keys and scheduled tasks, and creates hidden directories for payload storage.
- Credential dumping via Mimikatz and lateral movement using SMBExec and Pass-The-Hash/Pass-The-Ticket techniques enable wide network propagation.
- Exploitation of vulnerable drivers (CVE-2015-2291) through the ktool.exe payload deploys the Havoc Demon payload for further control.
- The attacker uses Netlify-hosted URLs for frequent updates of payloads and scripts to maintain stealth and efficacy of the campaign.
- Additional components include installing ZeroTier for remote access, deploying an XMRIG miner, and adding admin accounts to maintain long-term control.
MITRE Techniques
- [T1543] Create or Modify System Process – Creation of Scheduled Task “EdgeAutoUpdaterTask” and persistence via registry Run keys for script execution (“the final step is to create a Scheduled Task named ‘EdgeAutoUpdaterTask’ to ensure stage1.ps1 script is downloaded and executed”).
- [T1078] Valid Accounts – Addition of new admin user “svcadmin” with password “P@ssword123!” to escalate privileges in domain environments (“if any user in the remote machines is a Domain Admin, it adds a new user named ‘svcadmin’”).
- [T1055] Process Injection – Use of Meterpreter payload loaders disguised as executables (e.g., cwiper.exe, sh.exe series) for stealthy code execution (“most of the files mentioned were loaders to meterpreter payloads”).
- [T1003] Credential Dumping – Usage of Mimikatz to extract credentials and password hashes from memory (“Invoke-Mimikatz.ps1… runs ‘sekurlsa::logonpasswords’ command to list…computer credentials”).
- [T1021] Remote Services – Lateral movement using SMBExec for executing scripts on remote Active Directory machines (“Invoke-SMBExec.ps1… executes the propagation PowerShell line in AD machines”).
- [T1071] Application Layer Protocol – Exfiltration of reconnaissance data via HTTP POST requests (“collected info is sent to the attacker via an HTTP POST request in a form named ‘mimikatz’”).
- [T1112] Modify Registry – Persistence established by adding Run keys such as ‘HKLMSoftwareMicrosoftWindowsCurrentVersionRunUpdaterService’ (“adds an ‘UpdaterService’ entry in the Windows Run registry key”).
- [T1110] Brute Force – Enumeration and abuse of Active Directory to propagate infection and perform DCSync attacks (“performs a DCSync attack to steal credentials from the AD database”).
- [T1036] Masquerading – Use of LNK files named “EdgeAutoUpdater.lnk” deployed in the Startup folder to execute malicious scripts automatically (“LNK file is created in the Startup folder to ensure it is executed once the user logs in”).
- [T1218] Signed Binary Proxy Execution – Use of legitimate Windows tools like msiexec to install ZeroTier and execute other installers (“downloaded an MSI installer… installed it using the Windows msiexec tool”).
- [T1499] Endpoint Denial of Service – Attempt to disable Windows Defender protections to avoid detection (“attempt to disable Windows Defender protections and set persistence”).
- [T1553] Subvert Trust Controls – AMSI bypass by patching the AmsiScanBuffer function to evade malware detection (“bypassing AMSI technology by patching the ‘AmsiScanBuffer’ function exported by amsi.dll”).
Indicators of Compromise
- [File Names] Payload and script names used in the infection chain – payload.msi, wix.ps1, stage1.ps1, cwiper.exe, ktool.exe, sh.exe, rkd.exe, pivot.ps1
- [Domains] Netlify URLs hosting payloads – gentle-chebakia-da1172.netlify.app, other related URLs used for downloading scripts and executables
- [Registry Keys] Persistence and configuration – HKLM:SOFTWARE$r77configprocess_names, HKLMSoftwareMicrosoftWindowsCurrentVersionRunUpdaterService
- [Wallet Address] Crypto-mining wallet used by XMRIG miner – 8BSDR3NXiScgvyBShu8qunNdqURqMocHdJquG8Gw4hEV7yutSAsYkXp66cJptav3nJY1goVbZwoQFXNstRuAX2Ft3FDJBzu
Read more: https://www.netskope.com/blog/new-doge-big-balls-ransomware-tools-in-the-wild