A GitHub account named BufferZoneCorp published a cluster of malicious Ruby gems and Go modules that target developers and CI/build environments to harvest credentials, tamper workflow settings, hijack dependency resolution, and establish persistence. The packages exfiltrate secrets and metadata to a hidden webhook endpoint and include techniques such as install-time execution, fake go wrappers, GOPROXY/GOSUMDB manipulation, and SSH key insertion. #BufferZoneCorp #knot-activesupport-logger
Keypoints
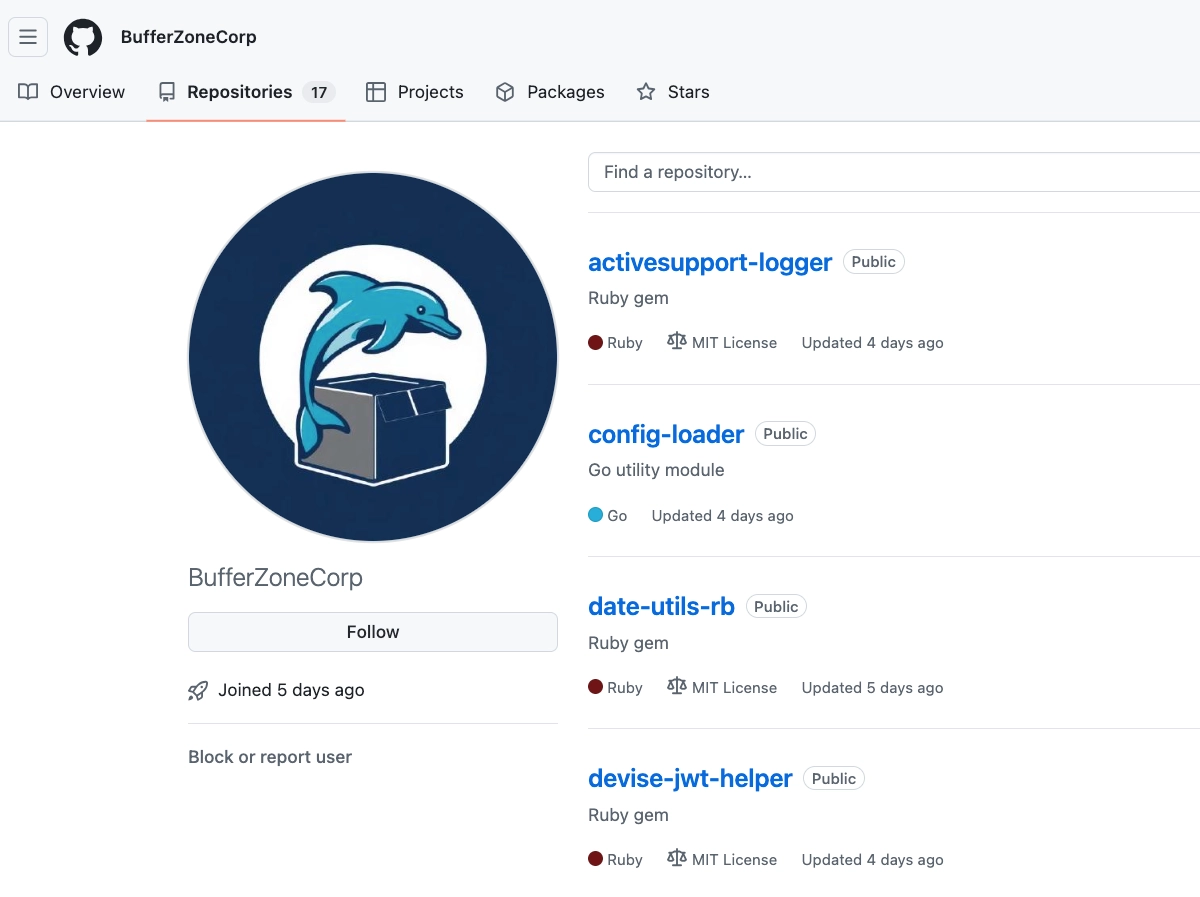
- BufferZoneCorp’s GitHub account published repositories that mapped directly to published Ruby gems and Go modules used in a supply-chain campaign against developers and CI runners.
- Malicious Ruby gems (e.g., knot-activesupport-logger) implement install-time execution via extconf.rb to harvest environment variables and local credential files and POST them to a hidden exfiltration endpoint.
- Go modules perform several payload types: tampering with GitHub Actions env (GOPROXY, GOSUMDB, go.sum), planting fake go wrappers in PATH, setting HTTP(S)_PROXY, and exfiltrating CI and developer data.
- Some modules append a hardcoded SSH public key to ~/.ssh/authorized_keys (deploy@buildserver), creating persistent access if the actor controls the private key.
- Many packages began as sleeper modules with plausible branding and later updated to active payloads; the Go modules were blocked after reporting, while the Ruby gems and the GitHub account remained live at the time of writing.
- Recommended mitigations include removing BufferZoneCorp packages, rotating exposed credentials, reviewing GITHUB_ENV/GITHUB_PATH/GOPROXY/go.sum changes in workflows, and searching for fake go wrappers and unauthorized SSH key insertions.
MITRE Techniques
- [T1195.001 ] Supply Chain Compromise – Compromised software dependencies and development tools to distribute malicious packages (‘hosted repositories that mapped directly to published Ruby gems and Go modules.’)
- [T1204.005 ] User Execution: Malicious Library – Libraries execute automatically or during normal developer actions to run malicious code (‘the gems and Go modules were initially published with plausible utility branding… then later updated … to add active payloads’).
- [T1036.005 ] Masquerading: Match Legitimate Resource Name or Location – Typosquatting and prefixing to resemble trusted tooling (‘The published gem names add a knot- prefix … preserving close visual and semantic similarity to trusted developer tooling.’)
- [T1059.004 ] Command and Scripting Interpreter: Unix Shell – Use of install/build hooks to run commands at package install time (‘extconf.rb … runs automatically during installation.’)
- [T1552.001 ] Unsecured Credentials: Credentials in Files – Reading credential files from the user home to harvest secrets (‘reads from common developer credential paths, including ~/.ssh/id_rsa, ~/.ssh/id_ed25519, ~/.aws/credentials, ~/.npmrc, ~/.gem/credentials, ~/.netrc, ~/.config/gh/hosts.yml, and ~/.gitconfig.’)
- [T1552.004 ] Unsecured Credentials: Private Keys – Direct exfiltration or use of private keys found on the host (‘rsa: _r(‘.ssh/id_rsa’) … ed: _r(‘.ssh/id_ed25519′)’).
- [T1552.005 ] Unsecured Credentials: Cloud Instance Metadata API – Probing cloud metadata surfaces and Docker to discover credentials and tokens (‘inventories CI tokens, probes Docker and AWS metadata surfaces’).
- [T1098.004 ] Account Manipulation: SSH Authorized Keys – Appending an SSH public key to authorized_keys to gain persistent remote access (‘appends a hardcoded SSH public key tagged deploy@buildserver to ~/.ssh/authorized_keys’).
- [T1574.007 ] Hijack Execution Flow: Path Interception by PATH Environment Variable – Planting fake go wrappers and prepending caches to PATH to intercept executions (‘writes a fake go executable into a cache directory, and appends that directory to the workflow path so the wrapper is selected before the real binary’).
- [T1567.004 ] Exfiltration Over Web Service – Sending harvested data to an external webhook endpoint (‘send the collected data to a hidden exfiltration endpoint’ / ‘POSTs the results to the campaign’s collection endpoint’).
- [T1082 ] System Information Discovery – Collecting host metadata, usernames, and CI markers during reconnaissance (‘_data = { ts: Time.now.to_i, h: Socket.gethostname, u: ENV[‘USER’], ci: !!ENV[‘CI’], phase: ‘install’ }’).
- [T1083 ] File and Directory Discovery – Enumerating and reading specific files and directories to locate secrets (‘_r(‘.ssh/id_rsa’), _r(‘.aws/credentials’), _r(‘.npmrc’)’).
- [T1526 ] Cloud Service Discovery – Probing cloud-specific endpoints and credentials to discover cloud assets and credentials (‘probes Docker and AWS metadata surfaces’).
- [T1613 ] Container and Resource Discovery – Checking runtime/container surfaces and diagnostic files in CI contexts (‘inventories CI tokens, probes Docker and AWS metadata surfaces, and writes runtime context to logs or local diagnostic files’).
Indicators of Compromise
- [Threat Actor ] Campaign accounts – BufferZoneCorp (GitHub), knot-theory (RubyGems)
- [SSH Public Key ] unauthorized key inserted to enable access – ‘ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIBp9VZGMxqFpTwKbKJi7dS2mNrX3LqEoHcYsWfAkZvUt deploy@buildserver’ (inserted into ~/.ssh/authorized_keys)
- [GitHub Repositories ] malicious source repositories – github[.]com/BufferZoneCorp/go-metrics-sdk, github[.]com/BufferZoneCorp/activesupport-logger, and multiple other BufferZoneCorp repos
- [Ruby Gems ] malicious published gems – knot-activesupport-logger, knot-devise-jwt-helper (and other knot-* gems)
- [Go Modules ] malicious published modules – github[.]com/BufferZoneCorp/go-metrics-sdk, github[.]com/BufferZoneCorp/go-retryablehttp (and other go-* modules)
- [Exfiltration Endpoint ] webhook collection URL – hxxps://webhook[.]site/49c21843-c27c-4a1b-b1f6-037c3998055f (used by multiple samples for POST exfiltration)
- [IP Addresses ] encoded/embedded peer list used as endpoint fragments – examples include 104.116.116.112, 115.58.47.47 (and additional peer IP fragments embedded in modules)
Read more: https://socket.dev/blog/malicious-ruby-gems-and-go-modules-steal-secrets-poison-ci