The Zscaler ThreatLabz team recently uncovered the latest activities of the Mustang Panda espionage group, notably in Myanmar, detailing new variants of their malware, ToneShell, and an additional tool called StarProxy. This research highlights significant updates in command-and-control operations and lateral movement strategies employed by the group. The article emphasizes the targeted sectors, including government and NGOs, while mentioning the advanced techniques they utilize to evade detection. Affected: Myanmar, Government entities, NGOs, Military entities
Keypoints :
- Mustang Panda is a China-sponsored espionage group targeting East Asian entities.
- Discovery of new ToneShell variants and a lateral movement tool named StarProxy.
- ToneShell updates include modifications to its C2 communication protocol and client identifier creation.
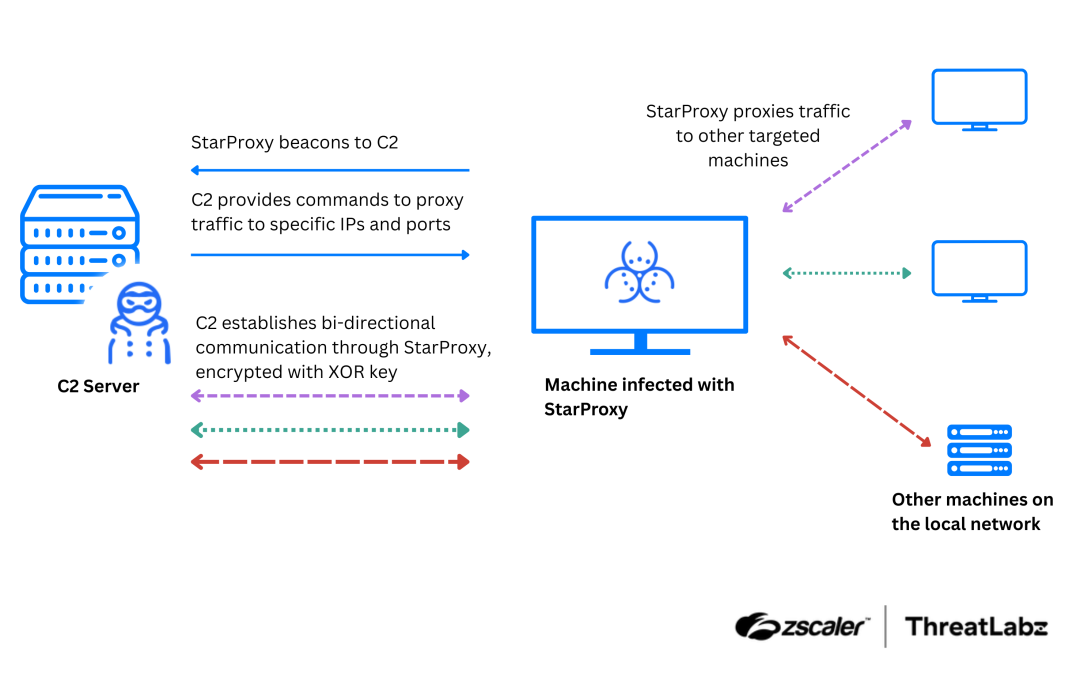
- StarProxy allows proxy traffic between infected devices and C2 servers, using FakeTLS protocol.
- DLL sideloading techniques were employed to execute malicious payloads, often packaged with legitimate binaries.
- Mustang Panda remains actively targeting organizations and individuals in Myanmar.
MITRE Techniques :
- T1574.002 Hijack Execution Flow: DLL Side-Loading – All the DLLs in this toolset are sideloaded by legitimate and signed Windows binaries.
- TA0011 Command and Control – StarProxy and ToneShell variants have command-and-control capabilities.
- T1573 Encrypted Channel – StarProxy uses two 256-byte XOR keys to encrypt and decrypt network packets using a custom algorithm.
- ToneShell variants use a rolling XOR key to encrypt and decrypt network packets.
- T1090.001 Proxy: Internal Proxy – StarProxy routes traffic between systems within a compromised network.
- T1573.001 Symmetric Cryptography – Tools use symmetric encryption algorithms for data protection.
- TA0005 Defense evasion – Encrypted network packets help evade network security products.
- T1001.003 Data Obfuscation: Protocol Impersonation – Tools use FakeTLS headers to blend in with legitimate network traffic.
- T1027.007 Obfuscated Files or Information: Dynamic API Resolution – ToneShell resolves APIs dynamically to evade detection.
- T1055.001 Process Injection: Dynamic-link Library Injection – DLL injection is used to execute payloads from C2 server.
- T1070.004 Indicator Removal: File Deletion – Functionality to delete payload files received from C2 server is present.
- T1134.002 Access Token Manipulation: Create Process with Token – ToneShell can create sub-processes with specific user tokens.
- T1087 Account Discovery – Functionality exists to retrieve a list of user accounts.
Indicator of Compromise :
- [MD5] 233214d22659aa85f32bb705812a0b22
- [MD5] b695a31ea90e61cc08da1837d836655a
- [MD5] 4fefc66a0f7e1b2ed8affc9c3ba66ec7
- [MD5] 6164f397ff13c56310e94af235a9aa02
- [MD5] 1b388ef6594415421ef1b3cd9502fc7a
Full Story: https://www.zscaler.com/blogs/security-research/latest-mustang-panda-arsenal-toneshell-and-starproxy-p1