This article explains how Kerberoasting is a covert attack technique exploiting Service Principal Names (SPNs) in Active Directory to recover service account passwords. It details methods of exploitation, detection, and mitigation strategies to defend against this threat. #Kerberoasting #ActiveDirectory #SPN #MITRE T1558.003
Keypoints
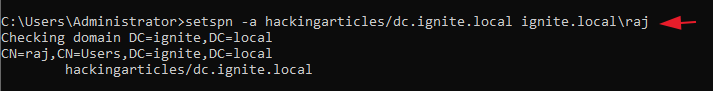
- Kerberoasting targets service accounts with SPNs in Active Directory by requesting service tickets.
- Attackers can crack the encrypted Ticket Granting Service (TGS) tickets offline to reveal passwords.
- Tools like Impacket, Rubeus, and targetedKerberoast facilitate the exploitation process.
- Detection involves monitoring Event ID 4769 for unusual ticket requests, especially RC4 encryption types.
- Mitigation includes using strong, complex passwords, rotating them regularly, and enforcing AES encryption.
Read More: https://www.hackingarticles.in/kerberoasting-attack-in-active-directory/