This article analyzes a pcap file to identify malicious activity related to the KOI Stealer infection, focusing on anomalies in network traffic using Wireshark. Critical indicators of compromise (IOCs) are extracted, including suspicious IP addresses and HTTP request patterns. Affected: C2 server, infected host, outbound external server, Active Directory environment
Keypoints :
- Analysis of pcap file from www.malware-traffic-analysis.net focusing on malicious network behavior.
- Identification of an Active Directory environment, including domain controller and segment details.
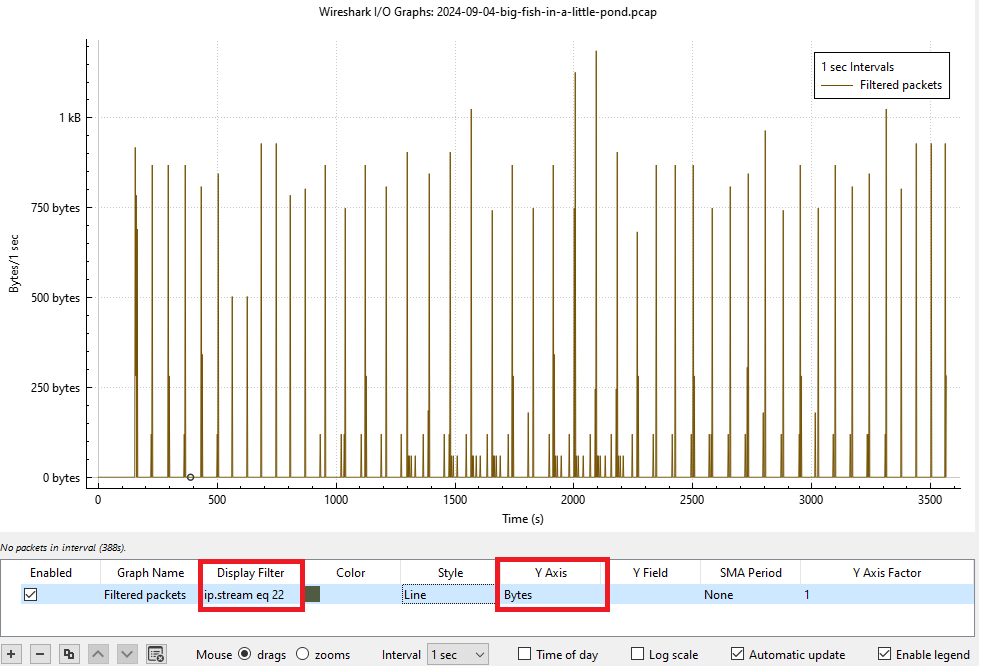
- Observation of unusual traffic patterns revealing potential command-and-control (C2) communications.
- Extraction of IOCs including suspicious IP addresses and HTTP request payloads.
- Detection of dynamic DNS updates as potential indicators of malware preparation for lateral movement.
- Identification of Málaga malware communications through specific IP addresses.
- Analysis of protocols like SMB and HTTP for signs of compromise.
- Use of JA3 fingerprints to identify malicious TLS traffic.
MITRE Techniques :
- Application Layer Protocol: DNS (T1071.004) – dynamic DNS updates indicating possible compromise.
- Command and Control (T1071) – periodic communication with C2 server for instructions, suggestive of beaconing behavior.
- Network Service Discovery (T1046) – identify traffic patterns that reveal internal host activities.
- Data Encrypted (T1041) – use of obfuscated data in HTTP POST requests to hide malicious activities.
Indicator of Compromise :
- [IP Address] 172.17.0.99 (Infected host inside LAN)
- [IP Address] 79.124.78.197 (C2 server)
- [IP Address] 46.254.34.201 (Malicious external server)
- [User-Agent] Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 10.0; WOW64; Trident/7.0; .NET4.0C; .NET4.0E; .NET CLR 2.0.50727; .NET CLR 3.0.30729; .NET CLR 3.5.30729)
- [HTTP URI] /foots.php/index.php?id=&subid=qIOuKk7U/index.php