Windows includes the Ancillary Function Driver (AFD) kernel component, which underpins networking sockets but has lacked comprehensive public API definitions until recently. New research and published definitions enhance forensic and troubleshooting capabilities for AFD sockets by exposing detailed socket information at the kernel level. #Windows #AncillaryFunctionDriver #AFD #SystemInformer
Keypoints
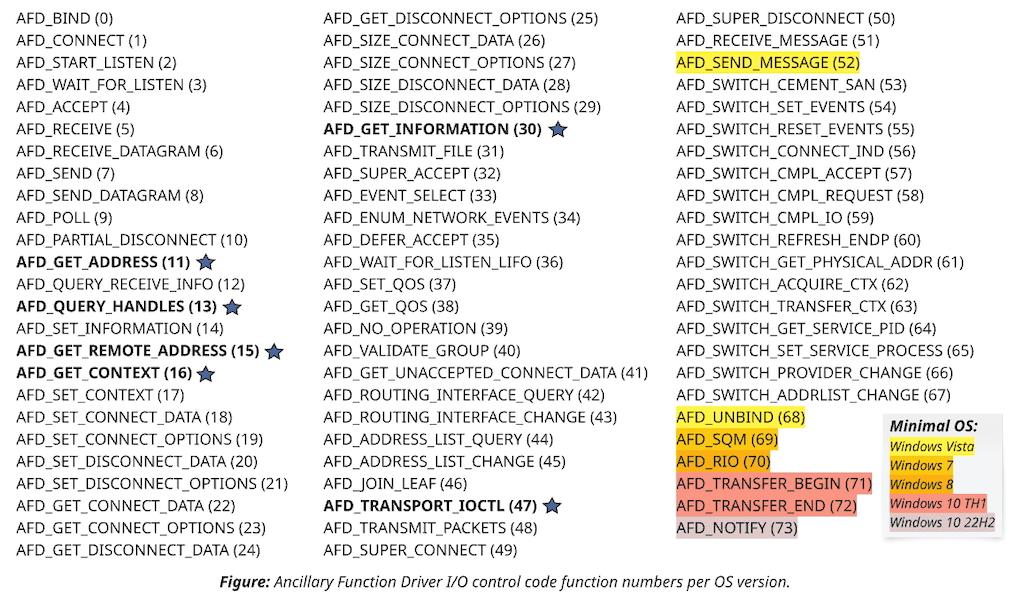
- AFD.sys provides the kernel-level backbone for Winsock networking sockets, exposing socket operations through around 70 IOCTL handlers accessible via DeviceIoControl.
- The transport mode of sockets (TLI, Hybrid, or TDI) significantly affects their behavior and the structures used in interacting with them, with Vista introducing important changes that caused compatibility challenges.
- Newly published PHNT header definitions for AFD enable detailed socket introspection and API usage previously unavailable or poorly documented for modern Windows versions.
- Forensic analysis benefits greatly from IOCTLAFDGETCONTEXT, IOCTLAFDGETINFORMATION, and address-related control codes, although some data like remote addresses can be user-mode spoofed.
- IOCTLAFDTRANSPORT_IOCTL allows querying and setting socket options at various protocol stack levels, revealing comprehensive socket configuration details across TCP, UDP, raw IP, and Hyper-V sockets.
- System Informer now integrates these capabilities to increase socket handle visibility, enabling enumeration and inspection of networking sockets across processes without using Winsock abstraction.
- Despite some driver bugs and undocumented behaviors (e.g., Hyper-V socket ioctl anomalies), the kernel-level AFD APIs offer a trustworthy source of socket state information for security and debugging.
MITRE Techniques
- [T1055] Process Injection – The possibility to duplicate socket handles and interact with underlying AFD sockets directly without Winsock could facilitate stealthy communication by bypassing user-mode APIs (‘…allows maintaining C2 communication without ever loading Winsock DLLs…’).
- [T1040] Network Sniffing – The detailed socket state inspection via AFD IOCTLs provides deeper insight into active connections, potentially aiding network monitoring and forensic data gathering (‘…provides detailed introspection of the state on a per-socket basis…’).
Indicators of Compromise
- [File Handles] Identification of DeviceAfd handles related to socket operations allows correlation with network activity and suspicious process handles.
- [IOCTL Codes] Usage of specific IOCTL codes such as IOCTLAFDGETCONTEXT, IOCTLAFDGETINFORMATION, IOCTLAFDTRANSPORT_IOCTL represents kernel-level socket queries potentially linked to forensic or monitoring tools.
- [File Names] Examples include devices like DeviceTcp, DeviceUdp, DeviceRawIp, and other protocol-specific device names relevant for socket transport modes.
Read more: https://www.huntandhackett.com/blog/improving_afd_socket_visibility