This article explains how DNS history and host response data can be leveraged to discover unreported domains potentially linked to the APT36 group, also known as Transparent Tribe. It details the investigative process using Validin to enrich and pivot on known indicators, revealing additional associated infrastructure. #APT36 #TransparentTribe #Validin
Keypoints
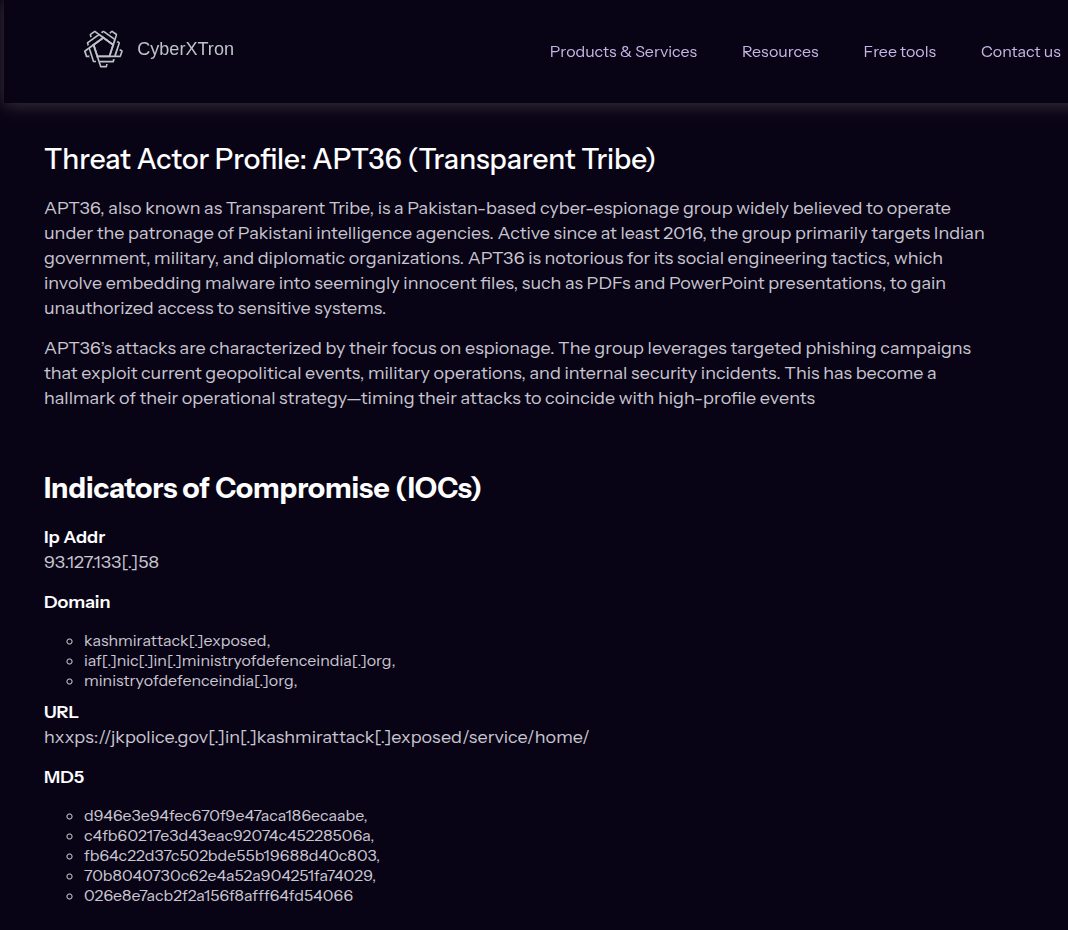
- Initial indicators related to a Transparent Tribe phishing attack targeting Indian government entities were collected from CyberXTron’s reports and tweets.
- A project named “Transparent Tribe Enrichment” was created in Validin to bulk import and track domain and IP indicators, including defanged ones.
- Wildcard searches on apex domains (kashmirattack[.]exposed and ministryofdefenceindia[.]org) revealed multiple associated subdomains and enriched the dataset.
- DNS history showed domain resolutions transitioning through obscure name servers to Cloudflare, with identification of several low-popularity IPs excluding Cloudflare ASNs for focused analysis.
- Pivoting on these IPs and host response attributes like HTTP title tags and ETag values uncovered additional domains and IPs associable with Transparent Tribe infrastructure.
- The study warned of “dangling Cloudflare proxies” causing potential misattribution of domains due to hijacked origin IPs while emphasizing careful correlation for threat hunting.
- The combined approach enabled the identification of previously unreported domains and IPs that may serve as early indicators of Transparent Tribe activity.
MITRE Techniques
- [T1598] Phishing – Initial targeted phishing attack against Indian Government and Defense attributed to Transparent Tribe as described (“…a targeted phishing attack attributed to Transparent Tribe…”).
- [T1584.001] Compromise Infrastructure: Domain Registrar – Use of altered DNS and domain infrastructure (wildcard domain and subdomain searches, DNS history analysis) to uncover malicious domains and pivot to related infrastructure.
- [T1566.001] Phishing: Spearphishing Attachment – Host response title tag pivoting revealed domains serving unusual PDF updates likely connected to phishing campaigns (“…title tags with the text ‘Pahalgam Terror Attack Updates.pdf’…”).
Indicators of Compromise
- [Domain] Known and newly discovered domains linked to Transparent Tribe – kashmirattack[.]exposed, ministryofdefenceindia[.]org, departmentofdefence[.]de, defenceindia[.]ltd, briefcases[.]email, departmentofspace[.]info, accounts[.]mgovcloud[.]in[.]storagecloud[.]download, accounts[.]mgovcloud[.]in[.]virtualeoffice[.]cloud, accounts[.]mgovcloud[.]in[.]cloudshare[.]digital, 37-221-64-252[.]cprapid[.]com
- [IP Address] Low-popularity IPs associated through DNS history – 93.127.133[.]58, 37.221.64[.]134, 45.141.58[.]224, 78.40.143[.]188, 78.40.143[.]189, 176.65.143[.]215, 37.221.64[.]252
- [HTTP Header – ETag] Unique ETag value used for host response pivoting – W/”18-yDYnaqhRYUMt/OyUu05l2wAGXRQ”
Read more: https://www.validin.com/blog/illuminating_transparent_tribe/