Proofpoint’s findings reveal a significant rise in account takeover (ATO) attempts targeting Microsoft 365 tenants, primarily leveraging various HTTP client tools. Notably, the Axios HTTP client has shown a high success rate in these attacks, while Node Fetch is used for brute force campaigns. The article discusses historical and current trends in ATO attacks, the evolving tactics of threat actors, and the impact on organizations. Affected: Microsoft 365
Keypoints :
- 78% of Microsoft 365 tenants faced at least one account takeover attempt.
- The Axios HTTP client achieved a 43% success rate in compromising targeted accounts.
- Brute force methods remain common but generally yield low success rates.
- Historical campaigns utilized the OkHttp client for user enumeration and targeted high-value users.
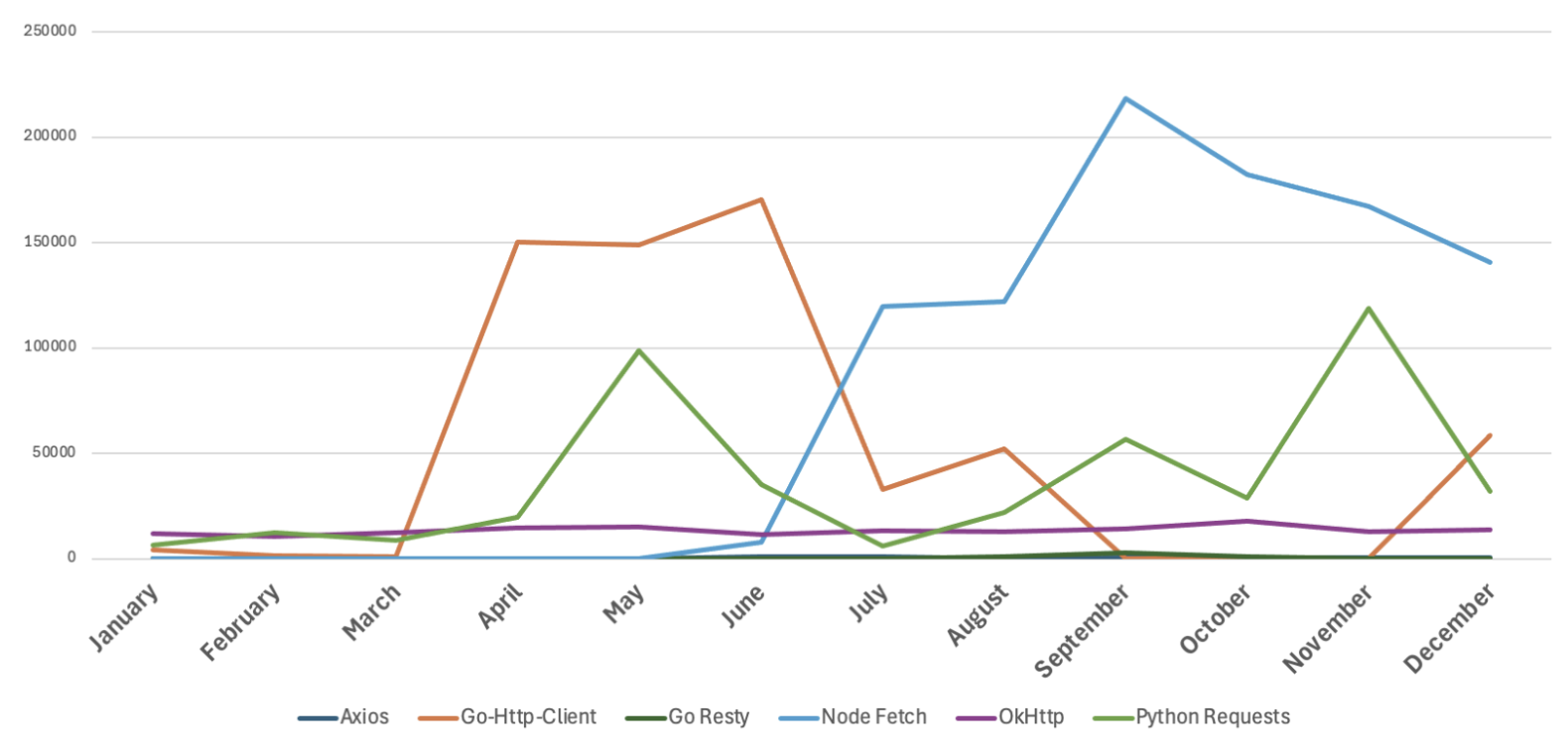
- Current trends show a rise in various HTTP clients, including python-requests and Go Resty, in ATO attacks.
- Attackers are increasingly using legitimate HTTP client tools to launch sophisticated ATO attacks.
- High-value targets include executives and financial officers across multiple industries.
- Node Fetch is primarily used for password spraying attacks with a low success rate.
- Threat actors are expected to continue evolving their tools and strategies.
MITRE Techniques :
- Brute Force (T1110) – Attackers utilize various HTTP clients to perform brute force login attempts against Microsoft 365 accounts.
- Account Manipulation (T1098) – Use of stolen credentials to compromise accounts and create unauthorized OAuth applications.
- Credential Dumping (T1003) – Credential theft through phishing and reverse proxy tools targeting Microsoft 365 users.
- Exploitation of Remote Services (T1210) – Leveraging HTTP clients to exploit vulnerabilities in Microsoft 365 services.
- Data Exfiltration (T1041) – Post-compromise actions include data theft and unauthorized sharing of sensitive information.
Indicator of Compromise :
- [domain] okhttp/3.2.0
- [domain] axios/0.21.1
- [domain] python-requests/2.20.0
- [url] https://nc.667af91ca5068[.]digital/auth
- [url] https://c.65a9b4549d87a[.]digital/auth
- Check the article for all found IoCs.
Full Research: https://www.proofpoint.com/us/blog/threat-insight/http-client-tools-exploitation-account-takeover-attacks