Gremlin stealer has evolved new obfuscation and anti-analysis methods, including hiding payloads in .NET resources, XOR encoding, and instruction virtualization through a commercial packing utility. It steals browser data, session tokens, crypto wallet information, and other credentials, then exfiltrates them to attacker-controlled infrastructure such as hxxp[:]194.87.92[.]109 for publication or sale. #Gremlin #Unit42 #CortexXDR #AdvancedWildFire
Keypoints
- Gremlin stealer now uses advanced obfuscation to hide its payload inside embedded .NET resources.
- A commercial packing utility with instruction virtualization converts the original code into custom bytecode executed by a private virtual machine.
- The malware targets browser cookies, session tokens, clipboard data, cryptocurrency wallets, FTP credentials, VPN credentials, and payment card details.
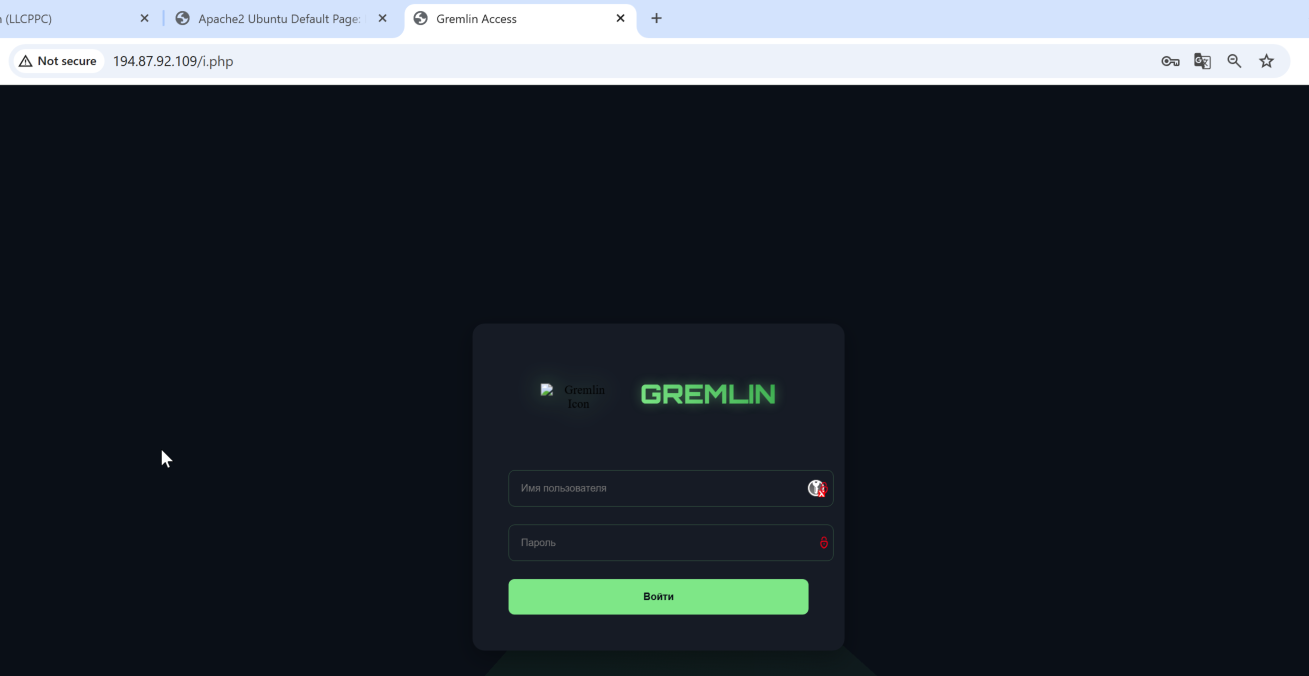
- A new Gremlin site at hxxp[:]194.87.92[.]109 was identified for publishing stolen data, and it had zero detections at the time of discovery.
- The latest variant adds a Discord token extraction module, a crypto clipper, and WebSocket-based session hijacking for live browser sessions.
- The malware names exfiltrated ZIP archives using the victim’s public IP address before uploading them to attacker-controlled servers.
- Compared with older samples, the newer builds add staged loading, XOR decryption, string encryption, and control-flow obfuscation to hinder analysis.
MITRE Techniques
- [T1027 ] Obfuscated Files or Information – The malware hides its payload in the .NET Resource section and uses XOR encoding to evade static analysis (‘the malicious payload into the .NET Resource section, masking it with XOR encoding to bypass signature-based detection and heuristic scanning’).
- [T1027.016 ] Stripped Payload – The sample is packed and transformed into custom bytecode executed by a private virtual machine, hindering inspection (’employs instruction virtualization, transforming the original code into a custom, non-standard bytecode executed by a private virtual machine’).
- [T1027.013 ] Encrypted/Encoded File – Strings and configuration data are encrypted and recovered only through a decoder routine (‘All important strings are hidden’ and ‘uses these numbers to calculate an offset and a length’).
- [T1055 ] Process Injection – The malware requests data directly from the running browser process to hijack live sessions (‘requesting the data directly from the running browser process’).
- [T1115 ] Clipboard Data – The clipper continuously monitors the clipboard for cryptocurrency wallet strings and replaces them in real time (‘continuously monitors the system clipboard’ and ‘replaces the victim’s address with the attacker’s wallet’).
- [T1005 ] Data from Local System – It collects local browser and system data such as cookies, tokens, clipboard contents, and stored credentials (‘Browser cookies’, ‘Session tokens’, ‘Clipboard contents’, ‘FTP and VPN credentials’).
- [T1566 ] Phishing – The article notes theft of digital identity and social engineering-related artifacts such as Discord tokens (‘signifies a pivot toward targeting digital identity and social engineering’).
- [T1041 ] Exfiltration Over C2 Channel – Stolen data is uploaded to attacker-controlled servers for publication or sale (‘exfiltrates it to attacker-controlled servers’).
Indicators of Compromise
- [SHA256] Gremlin stealer samples analyzed in the article – 2172dae9a5a695e00e0e4609e7db0207d8566d225f7e815fada246ae995c0f9b, 9aab30a3190301016c79f8a7f8edf45ec088ceecad39926cfcf3418145f3d614, and other 9 hashes
- [URL] New Gremlin exfiltration/publishing site – hxxp[:]194.87.92[.]109, hxxp[:]194.87.92[.]109/i.php
- [IP Address] Attacker-controlled site backend / published data host – 194.87.92.109
- [File Name / Archive] Stolen data is bundled into ZIP archives and named using the victim’s public IP address – ZIP archive containing browser cookies, session tokens, clipboard contents, and credentials
- [Embedded Resource Name] String decoder reads from the embedded resource file used by the .NET sample – resource
Read more: https://unit42.paloaltonetworks.com/gremlin-stealer-evolution/