Unit 42 researchers have uncovered Gremlin Stealer, a new C# malware that exfiltrates sensitive information such as credit card details, cookies, and credentials from victims’ machines. The malware is actively marketed in a Telegram group and is engineered to bypass security measures. Palo Alto Networks provides protective solutions against this threat. Affected: malware victims, online users, cybersecurity sectors.
Keypoints :
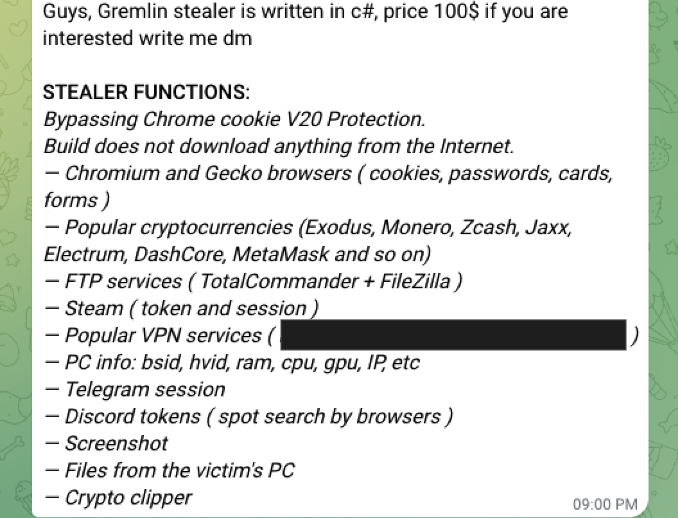
- Gremlin Stealer is an information-stealing malware written in C#.
- It has been marketed on a Telegram channel called CoderSharp since mid-March 2025.
- The malware can exfiltrate data from browsers, clipboard, and local disk.
- Stolen data includes credit card details, browser cookies, and VPN credentials.
- Palo Alto Networks offers protection through various cybersecurity solutions.
- A portal for uploading stolen data exists at 207.244.199[.]46.
- Gremlin Stealer can bypass Chrome’s cookie V20 protection.
- The malware is capable of stealing data from multiple applications including Telegram and Discord.
- Data is packaged and sent to attackers’ servers in ZIP format.
- Unit 42 advises users who suspect compromise to contact their Incident Response team.
MITRE Techniques :
- T1071.001 – Application Layer Protocol: Gremlin Stealer uses HTTP to communicate with its server at hxxp[:]//207.244.199[.]46/index.php.
- T1083 – File and Directory Discovery: It gathers information regarding directories and files related to cryptocurrency wallets.
- T1003.001 – Credential Dumping: Gremlin Stealer extracts usernames and passwords from FTP and VPN clients.
- T1203 – Exploitation for Client Execution: The malware exploits vulnerabilities to access sensitive data from browsers and other applications.
- T1526 – Indicator Removal on Host: Gremlin Stealer evades detection by storing stolen information in LOCAL_APP_DATA.
Indicator of Compromise :
- [URL] hxxp[:]//207.244.199[.]46/index.php
- [SHA256] d1ea7576611623c6a4ad1990ffed562e8981a3aa209717065eddc5be37a76132
- [IP Address] 207.244.199.46
- [Domain] 207.244.199[.]46
- [Email Address] N/A
Full Story: https://unit42.paloaltonetworks.com/new-malware-gremlin-stealer-for-sale-on-telegram/