This article discusses the security risks associated with Google Cloud Platform’s Cloud Build service, particularly the potential for supply chain attacks using a technique called “Bad.Build.” It highlights vulnerabilities in default permissions of the Cloud Build service account and emphasizes the need for enhanced monitoring and control over CI/CD operations to prevent malicious actions. Affected: Google Cloud Platform, Cloud Build Service, GCP users
Keypoints :
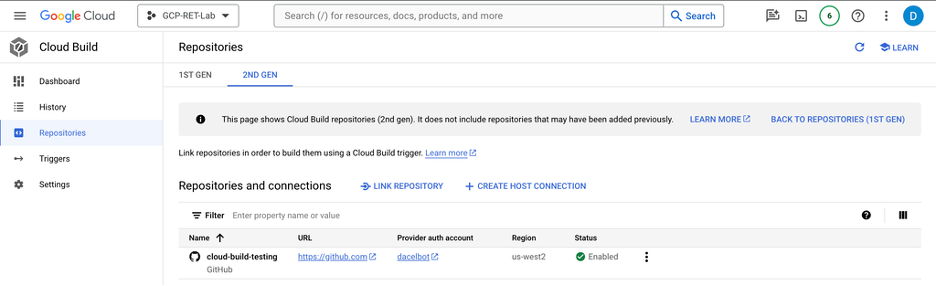
- Google Cloud Build is a CI/CD service used to automate application deployment.
- Orca Security identified vulnerabilities related to the default Service Account (SA) in Cloud Build.
- Threat actors can exploit Cloud Build permissions to execute malicious commands.
- Defensive measures include enforcing the principle of least privilege.
- Manual approval should be required for builds triggered by Pull Requests (PRs).
- Talos provided research on possible attacks leveraging the artifact registry and Cloud Storage.
- Data destruction can occur through malicious Cloud Build configurations.
- Logging of Cloud Build events is crucial for Digital Forensics & Incident Response (DFIR).
MITRE Techniques :
- Credential Dumping (T1078.004): A threat actor can obtain GCP user or service account credentials.
- Supply Chain Compromise (T1195.002): The addition of malicious code to a victim application via Cloud Build pipelines.
- Data Destruction (T1485): Deleting a Cloud Storage bucket using Cloud Build triggers.
- Data Encrypted for Impact (T1486): Encrypting objects in a Cloud Storage bucket via Cloud Build using customer-managed encryption keys.
Indicator of Compromise :
- [Domain] github.com
- [Command] gcloud storage rm –recursive gs://BUCKET_NAME
- [Command] gsutil cp “$FILE” “gs://$BUCKET_NAME/”
- [Command] gcloud builds triggers create github
- [Command] gcloud builds connections create github
Full Story: https://blog.talosintelligence.com/gcp-data-destruction-via-cloud-build/