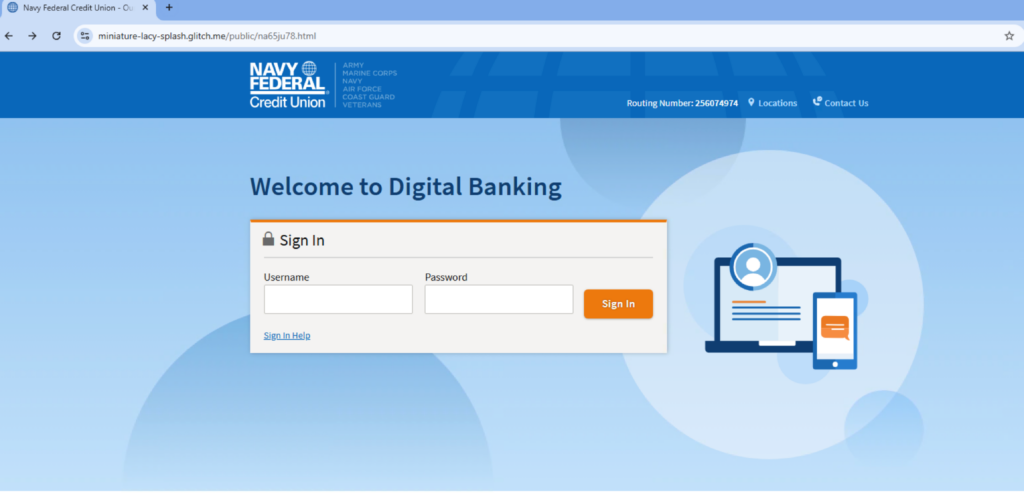
From January to April 2025, phishing traffic on the Glitch platform surged over threefold, targeting primarily Navy Federal Credit Union members and stealing sensitive data. Attackers bypass multi-factor authentication by exfiltrating credentials and one-time passwords via Telegram and use fake CAPTCHA tests to evade detection. #Glitch #NavyFederalCreditUnion #Telegram
Keypoints
- Traffic to phishing pages hosted on Glitch increased 3.32 times from January to April 2025.
- Phishing campaigns primarily target Navy Federal Credit Union members, aiming to steal login credentials and sensitive banking information.
- Half of the campaigns abuse Telegram to exfiltrate stolen credentials and one-time passwords, effectively bypassing multi-factor authentication.
- Attackers leverage Glitch’s free web hosting features and the “Remix” function to rapidly create multiple phishing subdomains.
- Some phishing pages incorporate fake CAPTCHA tests to deceive users and evade static web scanners.
- Attackers collect additional victim data such as IP address, location, and email credentials to facilitate fraud and account takeover.
- Phishing sites follow a URL pattern of three hyphenated English words followed by “.glitch.me”.
MITRE Techniques
- [T1110] Brute Force – Attackers request victims’ username and password inputs on phishing pages to gain unauthorized access. (“…victims to log in using the victim’s username and password…”)
- [T1566.001] Phishing: Spearphishing Link – Phishing pages on Glitch target specific groups like Navy Federal Credit Union members through crafted URLs. (“…phishing campaigns that are hosted on the Glitch platform targeting Navy Federal Credit Union members…”)
- [T1114] Email Collection – Attackers prompt victims to provide email addresses and passwords for further credential reset processes. (“…attackers request more sensitive information, including the user’s email address and password…”)
- [T1446] Exfiltration Over Alternative Protocol – Use of Telegram’s BotAPI sendMessage method to exfiltrate credentials and OTPs. (“…information is sent to the attacker using Telegram’s sendMessage method from BotAPI…”)
- [T1113] Screen Capture – Use of JavaScript to silently collect victim IP address, city, and country through services like ipify and ipinfo. (“…collect the victim’s public IP address and the victim’s country and city silently using JavaScript…”)
- [T1204.002] User Execution: Malicious File – Fake CAPTCHA tests prompt users to interact, allowing access to phishing page payloads while evading scanners. (“…fake CAPTCHA that trick victims into downloading the malicious payload or enter their credentials…”)
Indicators of Compromise
- [Domain] Glitch phishing subdomains – URL pattern example: projectname-projectname-projectname.glitch.me
- [Service] Telegram BotAPI – Used to exfiltrate stolen credentials and OTPs via sendMessage method
- [IP/Geo] Victim IP addresses and location data collected via ipify, ipinfo, and I2.io services
- [Credential Data] Usernames, passwords, one-time passwords (e.g., placeholder “0000”), email addresses collected through phishing pages