Gamaredon has been abusing CVE-2025-8088 in a long-running spearphishing campaign against Ukrainian state institutions, using weaponized archives to drop multi-stage VBScript payloads and establish persistence. The operation relies on GammaDrop and GammaLoad, with Cloudflare Workers, fast flux, DDNS, and compromised email infrastructure supporting selective payload delivery and host profiling. #Gamaredon #CVE-2025-8088 #GammaDrop #GammaLoad #CloudflareWorkers
Keypoints
- Gamaredon’s campaign against Ukrainian organizations has been active since at least September 2025 and remained ongoing through late April and early May 2026.
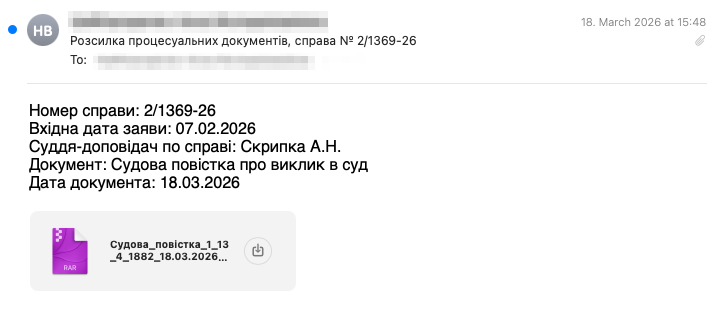
- The actor used spearphishing emails sent from compromised or spoofed government accounts to deliver weaponized RAR and later ARJ archives.
- CVE-2025-8088 in WinRAR was exploited to write a VBScript payload into the Windows Startup folder, enabling persistence.
- GammaDrop is the first-stage VBScript downloader that fetches a remote HTA file and executes it from a Cloudflare Workers infrastructure.
- GammaLoad is a second-stage HTA/VBScript implant that establishes persistence, profiles the host, and beacons to C2 servers for a tailored next-stage payload.
- The infrastructure used rotating Cloudflare Workers domains, quick tunnels, fast flux DNS, dynamic DNS providers, and a fallback domain pattern across multiple waves.
- The primary targets were Ukrainian state institutions, especially the SSU, along with courts, prosecutors, military, law enforcement, and regional administrative bodies.
MITRE Techniques
- [T1566.001 ] Spearphishing Attachment – The actor delivered malicious archives through email attachments to infect targets (‘weaponized RAR archives’ and ‘spearphishing emails against Ukrainian state institutions’).
- [T1204.002 ] User Execution: Malicious File – The victim had to extract/open the attached archive for the payload chain to begin (‘Upon extraction, the PDF is written normally’).
- [T1055 ] Process Injection – Not mentioned in the article.
- [T1036 ] Masquerading – The archive used a PDF decoy and later files masqueraded as documents or image types to hide the payload (‘a decoy file with a .pdf extension’ and ‘VBScript masquerading as encoded VBScript’).
- [T1027 ] Obfuscated Files or Information – Both GammaDrop and GammaLoad were heavily obfuscated to resist analysis (‘randomized variable names, junk functions and string building techniques’ and ‘roughly 4,000-5,000 lines’).
- [T1053.005 ] Scheduled Task/Job: Startup Items – Persistence was achieved by writing the VBS payload into the Windows Startup folder (‘writing the VBS payload to the Windows Startup folder, achieving persistence’).
- [T1105 ] Ingress Tool Transfer – GammaDrop downloaded GammaLoad and GammaLoad later fetched a next-stage payload from C2 (‘fetch a remote HTA’ and ‘downloads a next-stage payload’).
- [T1112 ] Modify Registry – GammaLoad established persistence with a RunOnce registry key (‘Establishes persistence via a RunOnce registry key’).
- [T1041 ] Exfiltration Over C2 Channel – GammaLoad beaconed host information to C2 servers (‘collects host information and beacons it to a set of C2 servers’).
- [T1016 ] System Network Configuration Discovery – The implant collected computer and system drive details for profiling (‘Computer name’ and ‘System drive’).
- [T1124 ] System Time Discovery – The beacon included a timestamp in the User-Agent and used date-derived values for URL generation (‘Date-derived value’ and ‘Timestamp of this beacon check-in’).
- [T1082 ] System Information Discovery – The malware gathered host identity and volume serial number (‘collects host information’ and ‘Volume serial number’).
- [T1583.006 ] Acquire Infrastructure: Web Services – The operators used Cloudflare Workers and trycloudflare tunnels to host delivery infrastructure (‘Cloudflare Workers domains’ and ‘Cloudflare quick tunnel URL’).
- [T1583.001 ] Acquire Infrastructure: Domains – The campaign used newly registered and attacker-controlled domains for C2 and relays (‘registered on 2026-03-25’ and ‘attacker-controlled email relays’).
- [T1090.002 ] Proxy: External Proxy – Cloudflare proxying was used to hide infrastructure (‘Cloudflare-proxied host’).
- [T1095 ] Non-Application Layer Protocol – The implants communicated over HTTP(S) using MSXML2.XMLHTTP (‘GET /k8f2ma.mov HTTP/1.1’).
Indicators of Compromise
- [SHA-256 ] Malicious archives, dropped payloads, and loader samples – 1e57e3c3225afcd4eece2f2dec9ac7f4a181a2681c3b8a56b831046aa8277007, 62818ae5e305b89b9461536dac1b9daf4cebd99d24e417357e27e2ae4582a704, and 69cdde1ec82099a471283de89dd5e17266b1d8dda57d3c1589b7754b009fa2ed
- [File names ] Weaponized archive and payload filenames – Судова_повістка_1_13_4_1882_18.03.2026.rar, brushedGpI.hta, and 1_13_4_1882_18.03.2026.vbs
- [Domains/hostnames ] C2, relay, and delivery infrastructure – throbsuns2.h4puonhajw.workers[.]dev, a.cnbyvilkghx2a6p.workers[.]dev, and kosoyed[.]ru
- [Domains/hostnames ] Additional infrastructure examples – bed-office-original-bytes.trycloudflare[.]com, relay.astrocaf[.]com, and heart7766.vmkyieebw2.workers[.]dev
- [Domains/hostnames ] Related DDNS and fallback infrastructure – uarefire[.]ru, yourrain[.]ru, myvnc[.]com, and 3utilities[.]com
- [IP addresses ] Malicious relay or operator IPs – 194.58.66[.]53, 194.58.66[.]82, and 194.58.66[.]106
- [File paths ] Persistence locations and temporary drop paths – %APPDATA%MicrosoftWindowsStart MenuProgramsStartup1_13_4_1882_18.03.2026.vbs, %TEMP%brushedGpI.hta, and %TEMP%casto0O.icl
- [Email artifacts ] Spoofing and mail delivery clues – X-Ukrnet-Yellow: 0, X-Ukrnet-Yellow: 64, and frv72.fwdcdn.com
Read more: https://harfanglab.io/insidethelab/gamaredon-gammadrop-gammaload/