CallPhantom is a cluster of 28 fraudulent Android apps on Google Play that falsely claimed to provide call logs, SMS records, and WhatsApp call history for any phone number after payment. The apps amassed more than 7.3 million downloads, used fabricated data and deceptive payment flows, and were removed after ESET reported them to Google. #CallPhantom #GooglePlay #Firebase #UPI
Keypoints
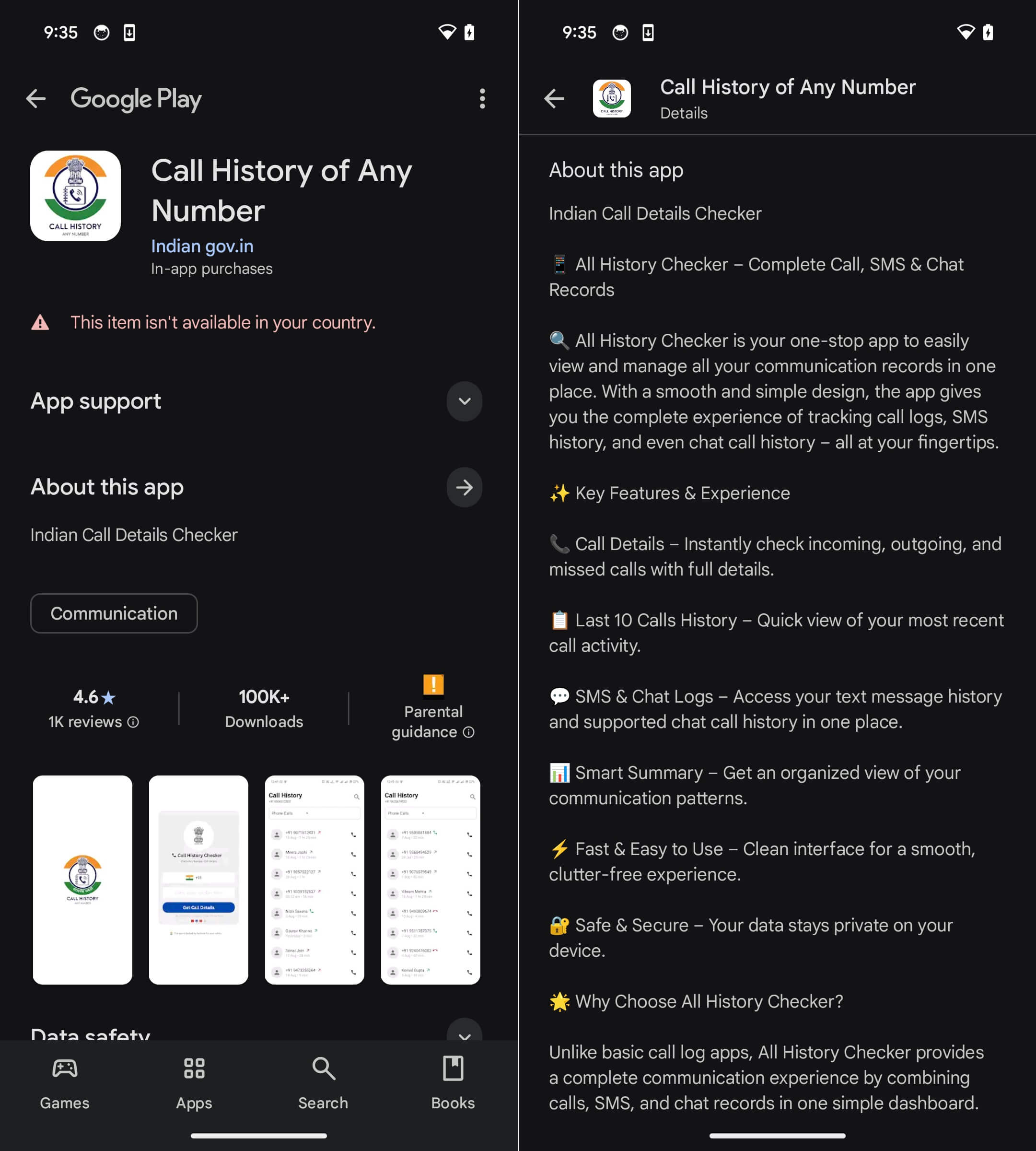
- CallPhantom refers to 28 fraudulent Android apps found on Google Play that promised access to call histories, SMS records, and WhatsApp call logs for any number.
- The apps generated fake results using hardcoded names, country codes, timestamps, and randomly generated phone numbers embedded in the code.
- Collectively, the apps were downloaded more than 7.3 million times before being removed from Google Play.
- The campaign mainly targeted Android users in India and the broader Asia-Pacific region, with some apps preselecting India’s +91 country code.
- Several apps used payment methods outside Google Play’s official billing system, including UPI-based third-party apps and direct card checkout forms, making refunds harder.
- One tactic used to pressure victims was a deceptive email-style notification claiming the results had arrived and linking to a subscription screen.
- ESET reported the full set of apps to Google, and existing subscriptions were canceled after removal from the store.
MITRE Techniques
- [T1437.001 ] Application Layer Protocol: Web Protocols – The apps used Firebase-based web infrastructure for command-and-control communication and payment URL delivery (‘CallPhantom uses Firebase Cloud Messaging for C&C communication’ and URLs were ‘fetched dynamically from a Firebase realtime database’).
- [T1643 ] Generate Traffic from Victim – The campaign attempted to create fraudulent billing by convincing users to pay for fake call history access (‘CallPhantom tries to achieve fraudulent billing’).
Indicators of Compromise
- [SHA-1 ] Android app samples – 799BB5127CA54239D3D4A14367DB3B712012CF14, 56A4FD71D1E4BBA2C5C240BE0D794DCFF709D9EB, and 26 more hashes
- [Package names ] Fraudulent app identifiers on Google Play – com.pixelxinnovation.manager, com.app.call.detail.history, and 26 more package names
- [Domains ] Firebase Realtime Database infrastructure used for payment/C2 – call-history-7cda4-default-rtdb.firebaseio.com, ch-ap-4-default-rtdb.firebaseio.com, and 2 more domains
- [IP addresses ] Google-hosted backend endpoints tied to the campaign – 34.120.160.131, 34.120.206.254
- [File names ] Android app samples and installers – all.callhistory.detail.apk, com.basehistory.historydownloading.xapk, and other APK/XAPK files