Two new variants of the KimJongRAT stealer have been analyzed, one using a Portable Executable (PE) file and the other implemented in PowerShell, both leveraging Windows shortcut (LNK) files to initiate infection via a legitimate CDN. These variants steal comprehensive victim information, including browser and crypto-wallet data, employing multi-stage loaders and backdoors communicating with attacker-controlled C2 servers. #KimJongRAT #PowerShellVariant #PEVariant #CryptoWalletStealer
Keypoints
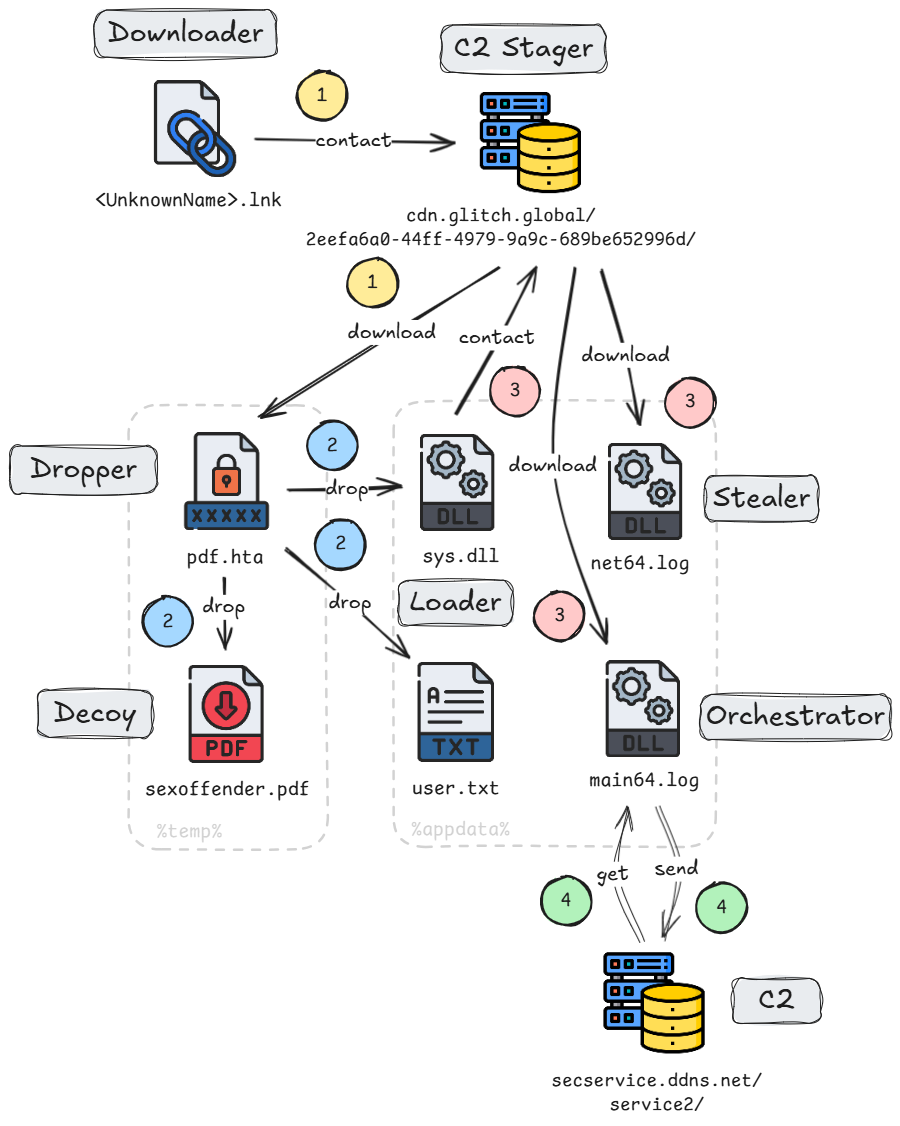
- Two KimJongRAT variants were identified: a PE-based variant and a PowerShell-based variant, both distributed via LNK files downloading malicious HTA droppers from legitimate CDN services.
- The PE variant deploys a multi-stage loader chain involving sys.dll, main64.log, and net64.log, where net64.log acts as the stealer and main64.log as the orchestrator and backdoor.
- The PowerShell variant drops a decoy PDF and a ZIP archive containing a PowerShell stealer and keylogger, focusing heavily on stealing cryptocurrency wallet-related browser extensions.
- Both variants gather extensive victim information including system info, browser data, email, FTP credentials, keystrokes, clipboard, and crypto-wallet extensions, then exfiltrate it to attacker-controlled C2 servers.
- The malware uses obfuscation techniques including Base64 encoding and simple substitution ciphers for hiding API strings and encryption methods such as RC4 and XOR for payloads and data exfiltration.
- Persistence is achieved in the PowerShell variant via registry entries launching obfuscated VBScript code; anti-VM and sandbox detection mechanisms are included to evade analysis.
- Palo Alto Networks solutions, including Advanced WildFire, Advanced URL Filtering, Advanced DNS Security, Cortex XDR, and XSIAM, provide detection and prevention capabilities against these threats.
MITRE Techniques
- [T1204] User Execution – Infection initiated by victim double-clicking malicious Windows shortcut (LNK) files that download subsequent payloads. (‘Initial LNK file downloads an HTA file and runs it.’)
- [T1105] Ingress Tool Transfer – Downloading of files like HTA, DLLs, and ZIP archives from attacker-controlled legitimate CDN service. (‘The initial LNK file downloads an HTA file from an attacker-controlled CDN account.’)
- [T1027] Obfuscated Files or Information – Use of obfuscated VBScript in HTA files and Base64 encoding to conceal payloads. (‘The HTA file contains obfuscated VBS code with embedded Base64 payloads.’)
- [T1053] Scheduled Task/Job – Persistence via registry Run key launching obfuscated VBScript in PowerShell variant. (‘Registry entry WindowsSecurityCheck created for persistence.’)
- [T1056] Input Capture – Keylogging and clipboard capture functionality in both variants. (‘Keylogger modules capture keystrokes, window titles and clipboard content.’)
- [T1005] Data from Local System – Stealing browser data, cookies, saved passwords, email and FTP client information, and cryptocurrency wallet extensions. (‘The stealer attempts to retrieve information from popular browsers and email or FTP clients.’)
- [T1071] Application Layer Protocol – C2 communication via HTTP GET and POST requests to upload stolen data and receive commands. (‘Network communication using HTTP POST multi and HTTP GET requests with the C2 server.’)
- [T1560] Archive Collected Data – Stolen data and browser files are compressed into ZIP archives before exfiltration. (‘Collected files compressed using PowerShell Compress-Archive command to micro.log.zip.’)
- [T1497] Virtualization/Sandbox Evasion – Anti-VM checks performed in loaders to avoid execution in virtual environments. (‘If malware is running on a virtual machine or sandbox, the loader deletes itself and quits.’)
Indicators of Compromise
- [SHA256 Hashes] Initial LNK files – a66c25b1f0dea6e06a4c9f8c5f6ebba0f6c21bd3b9cc326a56702db30418f189, 28f2fcece68822c38e72310c911ef007f8bd8fd711f2080844f666b7f371e9e1, and more.
- [SHA256 Hashes] First Stage HTA files – 02783530bbd8416ebc82ab1eb5bbe81d5d87731d24c6ff6a8e12139a5fe33cee, 3c2ea04090ad8c28116c42a9a2be5b240f135ac184e5a2c121b4eb311a7bf075, and others.
- [SHA256 Hashes] Second Stage Loader (baby.dll) files – f4d9547269e0cd7a0df97e394f688e0eb00b31965abd5e6ad67d373a7dc58f3b, 7a9f4ca13aed4d6d8ba430bc2b2f5ac2e4f9c7b5de2f5d2ba5aada211059da73, and others.
- [SHA256 Hashes] KimJongRAT Orchestrator (NetworkService.dll) – 85be5cc01f0e0127a26dceba76571a94335d00d490e5391ccef72e115c3301b3, bdb272189a7cdcf166fce130d58b794b242c582032f19369166b3d4cfdc0902c, and others.
- [SHA256 Hashes] KimJongRAT Stealer (dwm.dll, UPX packed) – 96df4f9cb5d9cacd6e3b947c61af9b8317194b1285936ce103f155e082290381, c356cd9fea07353a0ee4dfd4652bf79111b70790e7ed63df6b31d7ec2f5953d5, and others.
- [SHA256 Hash] PowerShell loader file – 97d1bd607b4dc00c356dd873cd4ac309e98f2bb17ae9a6791fc0a88bc056195a.
- [SHA256 Hashes] PowerShell stealer files – b103190c647ddd7d16766ee5af19e265f0e15d57e91a07b2a866f5b18178581c, eb68ed54e543c18070e5cc93a27db4a508d79016c09e28a47260ca080110328f.
- [SHA256 Hashes] PowerShell keylogger files – 3c6476411d214d40d0cc43241f63e933f5a77991939de158df40d84d04b7aa78, 4e45009f5b582ca404b197d28805e363a537856b55e39c5c806fcf05acd928ff.
- [SHA256 Hash] Persistence VBS file – f73164bd4d2a475f79fb7d0806cfc3ddb510015f9161e7dce537d90956c11393.
- [Domains] CDN stager URLs – cdn.glitch[.]global/2eefa6a0-44ff-4979-9a9c-689be652996d/, cdn.glitch[.]global/17443dac-272c-421c-80ac-53a3695ede0e/, and others.
- [IP Addresses / Domains] C2 servers – 131.153.13[.]235/sp/, 131.153.13[.]235/service/, secservice.ddns[.]net/service2/, srvdown.ddns[.]net/service3/.
Read more: https://unit42.paloaltonetworks.com/kimjongrat-stealer-variant-powershell/