Keypoints
- Wazuh collects Kubernetes audit logs (configured via an audit policy) and forwards them to a central Wazuh server for detection and analysis.
- The blog demonstrates deploying a local Minikube cluster on AlmaLinux, configuring audit logging, and exporting a flattened kubeconfig for remote emulation.
- The Wazuh agent is deployed as a Kubernetes DaemonSet to ensure audit logs from /var/log/kubernetes are monitored on every node.
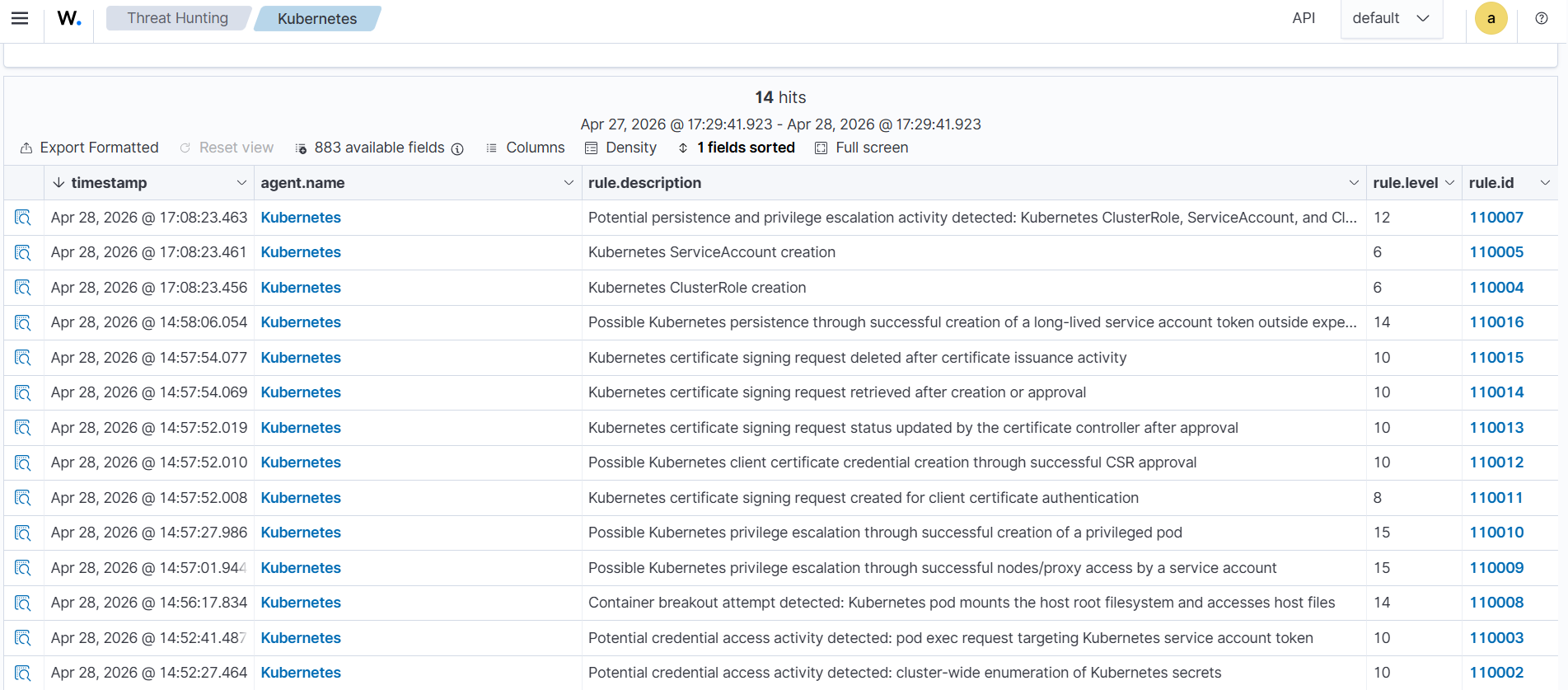
- Custom Wazuh rules (k8s_stratus_read_team_rules) map specific API audit patterns to MITRE ATT&CK techniques to detect credential access, privilege escalation, persistence, and container breakout attempts.
- Stratus Red Team is used from an Ubuntu endpoint (via an SSH tunnel to the API server) to emulate attacks such as dumping secrets, stealing service account tokens, creating privileged ClusterRoles/ServiceAccounts/Bindings, mounting hostPath, node/proxy abuse, privileged pods, CSR-based certificates, and long‑lived tokens.
- The blog includes cleanup instructions and guidance to view generated alerts on the Wazuh dashboard to validate detections and improve Kubernetes visibility and response.
MITRE Techniques
- [T1552 ] Unsecured Credentials – Detects cluster-wide enumeration and access to Kubernetes secrets ( ‘Potential credential access activity detected: cluster-wide enumeration of Kubernetes secrets.’ )
- [T1098 ] Account Manipulation – Detects creation of ClusterRoles, ServiceAccounts, and ClusterRoleBindings for persistence and privilege escalation ( ‘Kubernetes ClusterRole creation’ )
- [T1611 ] Escape to Host / Container Escape – Detects pods mounting host root filesystem and creation of privileged pods that enable container breakout ( ‘Container breakout attempt detected: Kubernetes pod mounts the host root filesystem and accesses host files’ )
- [T1068 ] Exploitation for Privilege Escalation – Detects successful nodes/proxy access by a service account indicating privilege escalation via kubelet/proxy APIs ( ‘Possible Kubernetes privilege escalation through successful nodes/proxy access by a service account’ )
- [T1649 ] Create or Abuse Client Certificates (Credential Creation) – Detects creation, approval, retrieval, status update, and deletion of CertificateSigningRequests used to create client certificates for API authentication ( ‘Kubernetes certificate signing request created for client certificate authentication’ )
Indicators of Compromise
- [Domain ] download and repository URLs referenced for tool and component installation – github.com/DataDog/stratus-red-team, download.docker.com, and 2 more domains (dl.k8s.io, pkgs.k8s.io)
- [File path ] Kubernetes and logging configuration files and audit logs – /etc/kubernetes/audit-policy.yaml, /etc/kubernetes/manifests/kube-apiserver.yaml (and /var/log/kubernetes/audit.log)
- [Container image ] Container images referenced in manifests and init containers – wazuh/wazuh-agent:4.14.5, busybox:1.36
- [Filename / Artifact ] Downloaded binaries and archives used for setup and emulation – stratus-red-team_Linux_x86_64.tar.gz, minikube-linux-amd64
- [Kubernetes API endpoints ] API request targets used in detection regexes and emulations – /api/v1/secrets, /apis/rbac.authorization.k8s.io/v1/clusterroles
- [Kubeconfig ] Configuration files used to authenticate to the cluster – /root/flat-kubeconfig, /root/.kube/config
Read more: https://wazuh.com/blog/detecting-kubernetes-attacks-with-wazuh-2/