Impacket is a Python-based toolkit used by both red teamers and threat actors for executing stealthy lateral movement, credential dumping, and remote command execution on Windows systems. This article details how to simulate Impacket attacks and configure Wazuh for effective detection of such malicious activities. #Impacket #Wazuh #WindowsSecurity
Keypoints
- Impacket contains modules like WMIexec, Secretsdump, and SMBexec that facilitate stealthy lateral movement, credential theft, and remote execution on Windows endpoints.
- The toolkit’s ability to mimic legitimate network activity makes it challenging to detect during cyber attacks.
- The article demonstrates configuring a Windows 11 endpoint to forward Sysmon logs to a Wazuh server to enhance monitoring capabilities.
- Enabling Windows remote administration services and configuring firewall rules is necessary to simulate realistic Impacket attack scenarios.
- Custom Wazuh detection rules were created to identify Impacket-related activities, including remote WMI commands and suspicious credential dumping behavior.
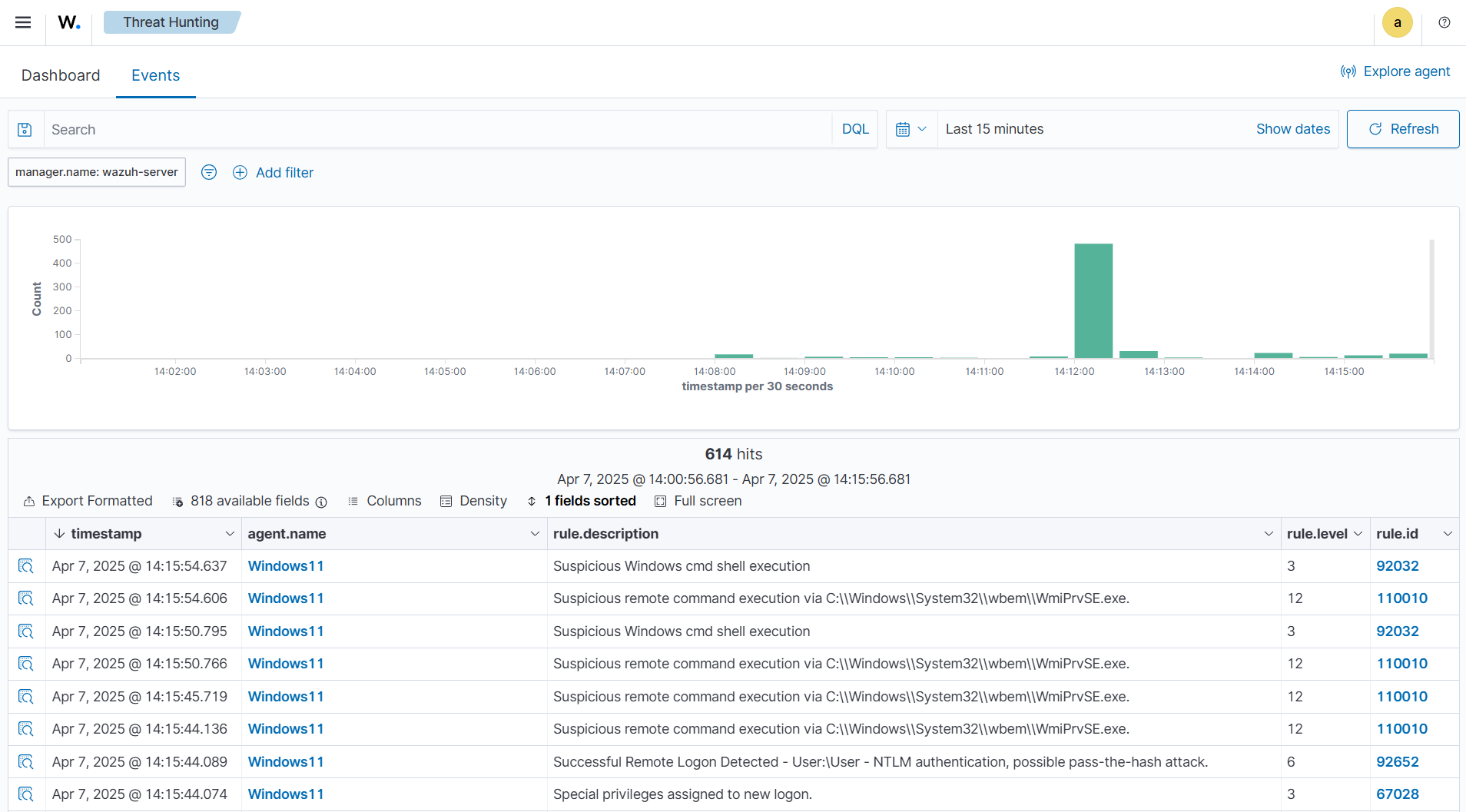
- Attack simulations using wmiexec.py, secretsdump.py, and smbexec.py successfully triggered alerts in Wazuh, validating the detection setup.
- Wazuh’s combination of built-in and custom rules improves detection confidence against stealthy attacks performed using Impacket tools.
MITRE Techniques
- [T1047] Windows Management Instrumentation – Used for remote command execution via WMI as evidenced by rules detecting wmiprvse.exe command execution (“Suspicious remote command execution via $(win.eventdata.parentimage)”).
- [T1021.003] Remote Services: Windows Management Instrumentation – Impacket modules utilize WMI for lateral movement and spawning remote shells.
- [T1003] Credential Dumping – Detection of svchost.exe creating temporary files related to Secretsdump module execution (“Possible attempt to dump credentials. svchost.exe created a temporary file $(win.eventdata.targetfilename)”).
Indicators of Compromise
- [File Names] Temporary files with eight-character names created in C:WindowsSystem32 or C:WindowsTemp directories associated with Secretsdump activity.
- [Processes] Execution of parent processes such as wmiprvse.exe, mmc.exe, explorer.exe, or services.exe launching cmd.exe with specific command-line flags indicating remote execution.
- [Configuration Files] Sysmon configuration file located at C:Sysmonsysmonconfig.xml used for advanced event logging and forwarding to Wazuh.
Read more: https://wazuh.com/blog/detecting-impacket-with-wazuh/