The article discusses the discovery of how the io_uring system in Linux can be exploited to evade detection by various security tools. ARMO released a proof-of-concept tool, “curing”, demonstrating this vulnerability. Sysdig and Falco have implemented detection strategies to counteract this evasion technique, emphasizing the importance of layered security. Affected: Crowdstrike, Microsoft Defender, Falco, Tetragon, Linux security tools.
Keypoints :
- ARMO published a report on using io_uring to bypass Linux security tools.
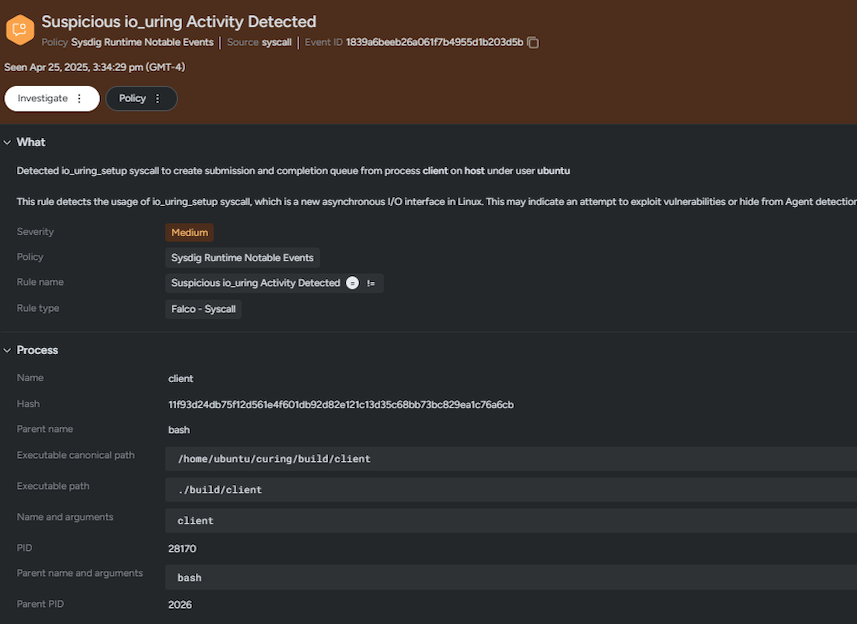
- A proof-of-concept tool called “curing” was shared by ARMO to exploit the io_uring flaw.
- Sysdig introduced a rule to detect suspicious io_uring activity.
- Falco is enhancing its functionality to detect io_uring initiated operations.
- Io_uring allows certain actions to be executed without detection by system call-based tools.
- Initial Access and Execution of malicious code are prerequisites for leveraging io_uring for evasion.
- Io_uring does not hide files or processes and does not apply to process execution.
- Containerized workloads typically do not experience this evasion technique due to default security profiles.
- Sysdig and Falco are implementing layered security strategies to mitigate risks from this technique.
- Improvement updates from Falco are expected regarding its ability to detect io_uring activities.
MITRE Techniques :
- Initial Access (T1078) – Attackers need to gain access to a system to use io_uring for evasion.
- Execution (T1203) – Malicious code must be executed to then utilize io_uring calls for undetected activity.
Indicator of Compromise :
- None explicitly mentioned in the article.
Full Story: https://sysdig.com/blog/detecting-and-mitigating-io-uring-abuse-for-malware-evasion/