NightSpire is a financially motivated ransomware group that emerged in early 2025, utilizing a double extortion strategy targeting small to medium-sized enterprises globally. They exploit vulnerabilities such as CVE-2024-55591 and use living-off-the-land techniques for lateral movement, exfiltrating data prior to encryption and demanding ransom payments under threat of data leak. #NightSpire #CVE202455591
Keypoints
- NightSpire ransomware surfaced in early 2025 and targets small and medium-sized enterprises across multiple industries and countries.
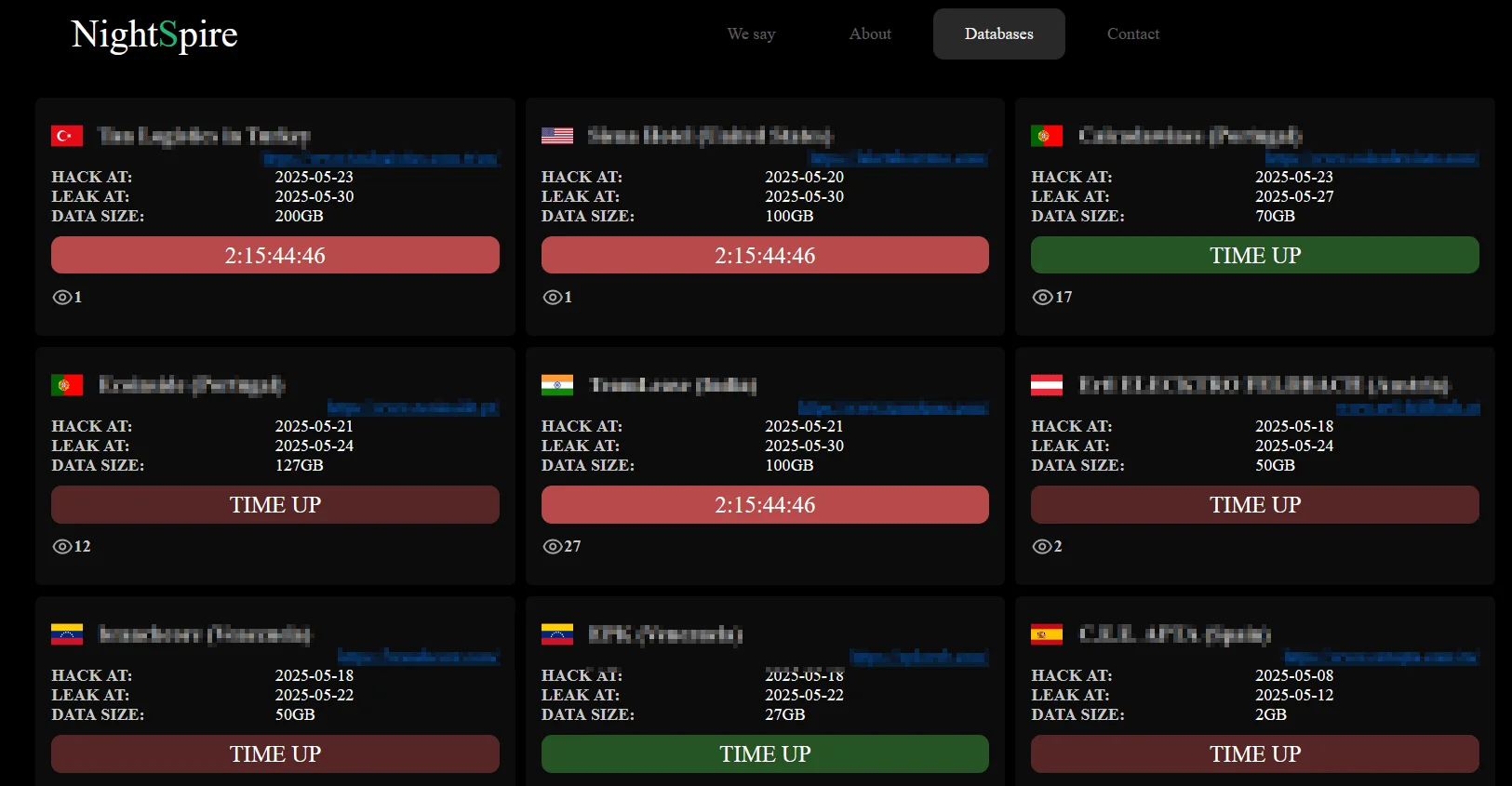
- The group uses a double extortion tactic by stealing data and encrypting victim systems, threatening to publish stolen data on their Dark Web Data Leak Site.
- The United States is the most frequently targeted country, followed by Taiwan, Hong Kong, Egypt, and various European nations.
- They exploit public-facing vulnerabilities such as FortiOS zero-day CVE-2024-55591 to gain initial access and use common tools like PowerShell, PsExec, and WMI for lateral movement.
- Credential dumping via Mimikatz and data exfiltration using Rclone or MEGA are integral parts of their operations.
- Mitigation strategies include prompt patching, restricting remote access, network segmentation, monitoring for exfiltration tools, and maintaining offline backups.
- SOCRadar provides real-time threat intelligence and attack surface management to help defend against NightSpire’s evolving tactics.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Initial access via vulnerable systems like FortiOS (e.g., CVE-2024-55591) (‘exploiting public-facing vulnerabilities in systems such as VPN appliances, firewalls, or unpatched web servers, notably CVE-2024-55591’).
- [T1078] Valid Accounts – Use of stolen or brute-forced credentials including RDP (‘Use of stolen or brute-forced credentials (including RDP)’).
- [T1059.001] PowerShell – Used for lateral movement and remote execution (‘NightSpire moves laterally using legitimate tools such as PowerShell’).
- [T1021.002] SMB/Windows Admin Shares – Lateral movement via administrative shares (‘navigate laterally through internal systems’).
- [T1003.001] LSASS Memory – Credential dumping using tools like Mimikatz (‘dumps credentials using tools like Mimikatz’).
- [T1482] Domain Trust Discovery – Mapping domain and trust relationships (‘maps out the Active Directory environment to gain control over key systems’).
- [T1041] Exfiltration Over C2 Channel – Stolen data sent to attacker-controlled storage such as Rclone and MEGA (‘packages sensitive files into encrypted archives and transfers them using utilities such as Rclone or MEGA’).
- [T1486] Data Encrypted for Impact – Employs strong AES-256 + RSA encryption to lock systems (‘encrypting data after exfiltration’).
- [T1485] Data Manipulation: Data Destruction – Threatens data release and possible destruction during extortion phase (‘threatening to publish stolen data on their Dark Web Data Leak Site’).
- [T1573] Encrypted Channel – Use of encryption to conceal C2 traffic (‘Communication with victims takes place over relatively secure platforms such as ProtonMail, Telegram, or custom Dark Web chat portals’).
- [T1583.006] Acquire Infrastructure: Web Services – Uses cloud platforms for data exfiltration (‘transfers them to attacker-controlled infrastructure using utilities such as Rclone or MEGA’).
Indicators of Compromise
- [File Hashes] NightSpire ransomware samples identified – 0170601e27117e9639851a969240b959, 7a4aee1910b84c6715c465277229740dfc73fa39, and 2 more hashes.
- [Domain] Dark Web Data Leak Site used for extortion – a2lyiiaq4n74tlgz4fk3ft4akolapfrzk772dk24iq32cznjsmzpanqd[.]onion
Read more: https://socradar.io/dark-web-profile-nightspire-ransomware/