The FBI, US DoD, and multiple cybersecurity companies, including ESET, successfully disrupted the Danabot infostealer malware infrastructure as part of Operation Endgame. Danabot operated as a malware-as-a-service platform, offering a sophisticated toolset for affiliates to steal data and distribute additional malware including ransomware. #Danabot #OperationEndgame
Keypoints
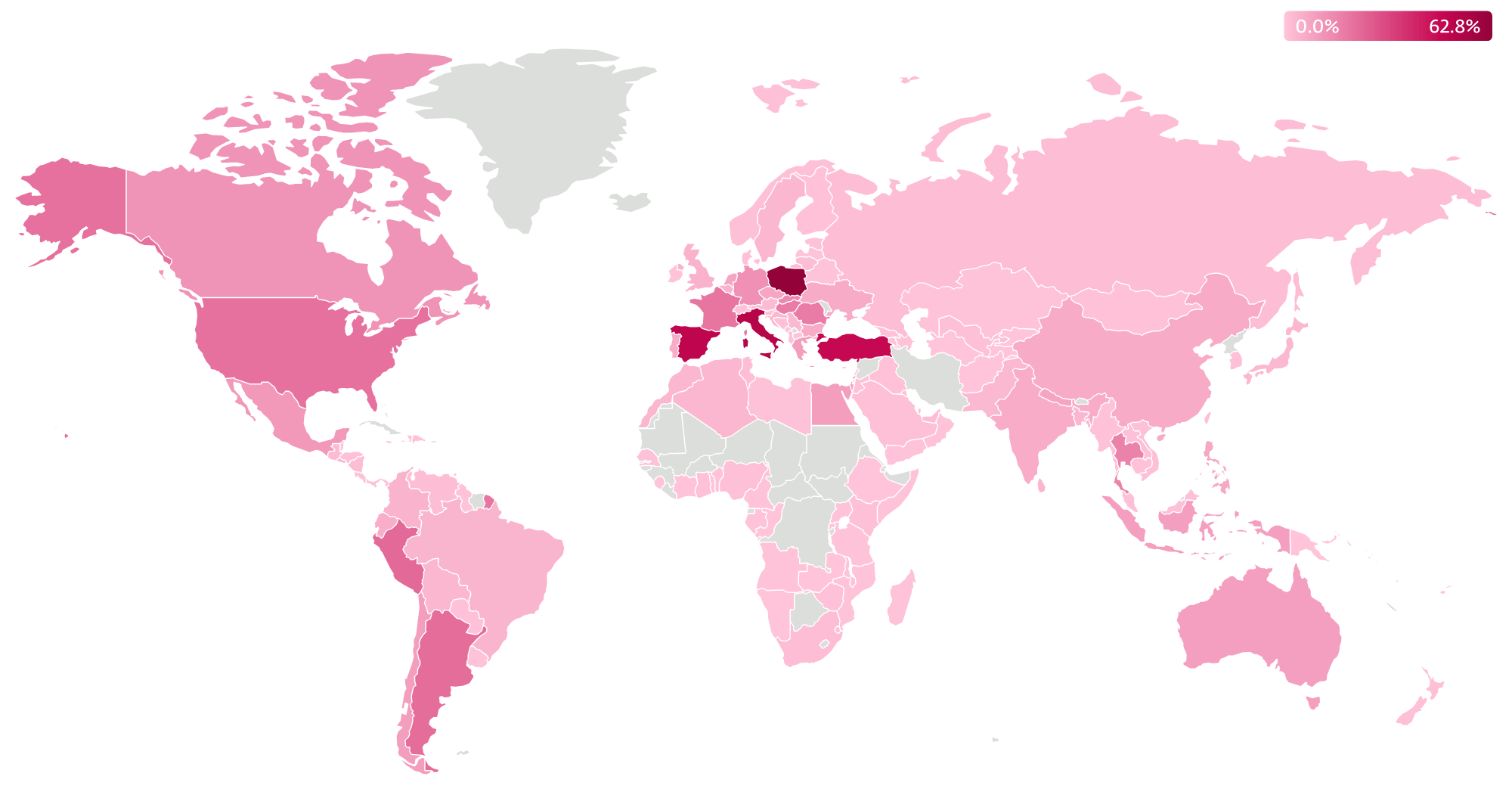
- ESET has been tracking Danabot since 2018, uncovering over 1,000 unique command-and-control (C&C) servers worldwide.
- Danabot is primarily an infostealer and banking trojan, but it also serves as a loader for additional malware such as LockBit ransomware.
- The malware is offered as MaaS (malware-as-a-service) on underground forums with various rental and customization options for affiliates.
- Typical toolset includes an administration panel, backconnect tool for real-time control, proxy server applications, and options to generate customized builds.
- Distribution techniques include spam campaigns, malvertising, malware loaders, and misuse of Google Ads to lure victims through deceptive websites and software bundles.
- Danabot uses encrypted communication protocols with AES-256 and RSA, supports Tor fallback channels, and uses multi-hop proxy servers to evade detection.
- The takedown was part of the coordinated global Operation Endgame, involving numerous law enforcement and private sector partners.
MITRE Techniques
- [T1583.003] Acquire Infrastructure: Virtual Private Server – Danabot operators use VPS in their infrastructure.
- [T1583.004] Acquire Infrastructure: Server – Multiple servers acquired for C&C communication.
- [T1587.001] Develop Capabilities: Malware – Danabot authors developed custom malware tools.
- [T1608.001] Stage Capabilities: Upload Malware – Operators upload other malware to Danabot’s infrastructure for spreading.
- [T1583.008] Acquire Infrastructure: Malvertising – Malvertising is used as a Danabot distribution method.
- [T1566.001] Phishing: Spearphishing Attachment – Spearphishing attachments are commonly used to distribute Danabot.
- [T1106] Native API – Danabot uses dynamic Windows API resolution.
- [T1204.001] User Execution: Malicious Link – Victims are lured into executing malicious links leading to Danabot deployment.
- [T1204.002] User Execution: Malicious File – Danabot distributed through malicious files.
- [T1548.002] Abuse Elevation Control Mechanism: Bypass User Account Control – Danabot bypasses UAC with multiple methods.
- [T1027.007] Obfuscated Files or Information: Dynamic API Resolution – Uses hashing for dynamic API resolution.
- [T1055.001] Process Injection: Dynamic-link Library Injection – Injects into other processes to evade detection.
- [T1218.007] System Binary Proxy Execution: Msiexec – MSI packages used for distribution.
- [T1218.010] System Binary Proxy Execution: Regsvr32 – regsvr32.exe used to execute Danabot modules.
- [T1218.011] System Binary Proxy Execution: Rundll32 – rundll32.exe used for execution of Danabot DLLs.
- [T1656] Impersonation – Used in phishing campaigns to gain initial access.
- [T1555.003] Credentials from Password Stores: Credentials from Web Browsers – Steals browser-saved credentials.
- [T1539] Steal Web Session Cookie – Can steal web session cookies.
- [T1010] Application Window Discovery – Collects data based on the active window.
- [T1217] Browser Information Discovery – Gathers browser-related information like history.
- [T1083] File and Directory Discovery – Discovers files/directories to steal data.
- [T1057] Process Discovery – Enumerates running processes on infected systems.
- [T1021.001] Remote Services: Remote Desktop Protocol – Uses RDP for remote control of bots.
- [T1021.005] Remote Services: VNC – Supports VNC for remote access.
- [T1056.001] Input Capture: Keylogging – Keylogging capability for data theft.
- [T1560.002] Archive Collected Data: Archive via Library – Compresses data with zlib and ZIP.
- [T1560.003] Archive Collected Data: Archive via Custom Method – Further encrypts collected data using AES and RSA.
- [T1119] Automated Collection – Automated collection of victim data.
- [T1185] Browser Session Hijacking – Performs webinjects to alter web functions.
- [T1115] Clipboard Data – Collects clipboard contents.
- [T1005] Data from Local System – Searches for sensitive files locally.
- [T1113] Screen Capture – Takes screenshots periodically.
- [T1125] Video Capture – Captures video on victim machines.
- [T1132.001] Data Encoding: Standard Encoding – Compresses data between bot and C&C using ZIP and zlib.
- [T1001.001] Data Obfuscation: Junk Data – Adds junk bytes to obfuscate communication.
- [T1573.001] Encrypted Channel: Symmetric Cryptography – Uses AES-256 encryption.
- [T1573.002] Encrypted Channel: Asymmetric Cryptography – Uses RSA encryption.
- [T1008] Fallback Channels – Uses Tor as a fallback for C&C communication.
- [T1095] Non-Application Layer Protocol – Utilizes a proprietary TCP protocol.
- [T1571] Non-Standard Port – Communicates on arbitrary ports.
- [T1090.003] Proxy: Multi-hop Proxy – Employs proxy chains to hide C&C server locations.
- [T1219] Remote Access Software – Supports remote access tools within the malware.
- [T1020] Automated Exfiltration – Automates victim data exfiltration.
- [T1030] Data Transfer Size Limits – Limits large file transfers to evade detection.
- [T1041] Exfiltration Over C2 Channel – Exfiltrates data over the command and control channel.
- [T1498] Network Denial of Service – Conducted DDoS attacks using Danabot modules.
Indicators of Compromise
- [File Hashes] Danabot components – 6D361CD9ADBF1630AF7B323584168E0CBD9315FB (Loader), A7475753CB865AEC8DC4A6CEA27F2AA594EE25E8 (Main component), 787EAB54714F76099EC350E029154ADFD5EDF079 (Dropper).
- [File Hashes] Lockbit ransomware payload distributed by Danabot – 17B78AD12B1AE1C037C5D39DBE7AA0E7DE4EC809.
- [IP Addresses] Danabot proxy C&C servers – 212.18.104[.]245, 212.18.104[.]246 (Global Connectivity Solutions LLP), 34.16.215[.]110, 34.65.116[.]208, 34.168.100[.]35 (Google LLC).
- [Domains] Deceptive websites used in Danabot distribution – advanced-ip-scanned.com, gfind.org, mic-tests.com.
Read more: https://www.welivesecurity.com/en/eset-research/danabot-analyzing-fallen-empire/