A sophisticated phishing campaign targets payroll and payment platforms by impersonating Deel through malicious Google ads, stealing credentials and bypassing two-factor authentication to facilitate wire fraud using advanced web technologies. (Affected: Payroll platforms, Payment platforms, HR services, Online commerce)
Keypoints :
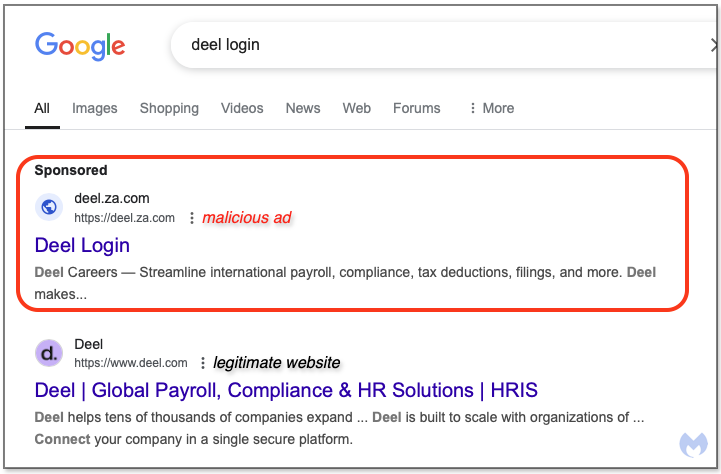
- A new phishing kit impersonates Deel via fraudulent Google search ads targeting payroll and HR users.
- The phishing site steals usernames, passwords, and circumvents two-factor authentication through social engineering.
- Malicious JavaScript code uses Pusher WebSockets and web workers to manipulate bank and payment data in real-time.
- Anti-debugging and code obfuscation techniques complicate malware analysis and detection.
- The phishing URLs rotate and use cloaking to evade detection and redirect users to decoy or phishing domains.
- Multiple related targets include payroll, payment solutions, and commerce platforms like Shopify and Marqeta.
- FBI issued a public service announcement warning about impersonation via search ads and wire fraud risks.
- Indicators include specific phishing domains, obfuscated JavaScript files, and use of legitimate services to mask malicious activity.
- Users should verify URLs carefully, apply phishing awareness, and use browser protections against malicious ads and sites.
- The campaign demonstrates increasing cybercriminal sophistication requiring shared security responsibility between users and platforms.
MITRE Techniques :
- Phishing (T1566) – Use of fraudulent search ads and phishing websites to steal user credentials and bypass Two-Factor Authentication.
- User Execution (T1204) – Victims are socially engineered to enter credentials and OTP codes into fake login pages.
- Credential Access (T1110) – Password harvesting through phishing forms impersonating legitimate login portals.
- Web Service (T1102) – Abuse of legitimate hosted service Pusher to facilitate real-time communication and data exfiltration.
- Command and Control over WebSockets (T1071.004) – Use of persistent WebSocket connections to communicate between victim’s browser and attacker infrastructure.
- Obfuscated Files or Information (T1027) – Use of JavaScript obfuscation to conceal malicious code and prevent detection.
- Process Injection (T1055) – Use of web workers and script injection to authenticate victims while hiding malicious operations.
- Input Capture (T1056) – Capturing credentials and two-factor codes via manipulated login forms and session hijacking.
Indicator of Compromise :
- The article includes domain names of phishing sites such as login-deel[.]app and accuont-app-deel[.]cc used to impersonate Deel’s login portal.
- It mentions the use of URL redirects like deel[.]za[.]com designed to redirect victims to phishing domains through cloaking techniques.
- Hashes of key JavaScript files involved in the phishing kit, including Worker.js (SHA256: 56755aaba6…) and obfuscated kel.js/auth.js libraries (SHA256: 72864bd09c…), are provided for detection.
- The mention of legitimate service Pusher’s real-time communication traffic patterns can act as behavioral IOCs to identify malicious WebSocket connections.