Government institutions worldwide are increasingly targeted by sophisticated cyberattacks, leveraging phishing emails, fraudulent domains, and malicious PDFs. ANY.RUN’s solutions provide critical tools for detecting, analyzing, and mitigating these threats, enhancing organizational cybersecurity resilience. #FormBook #ScreenConnect #SocialSecurityAdministration
Keypoints
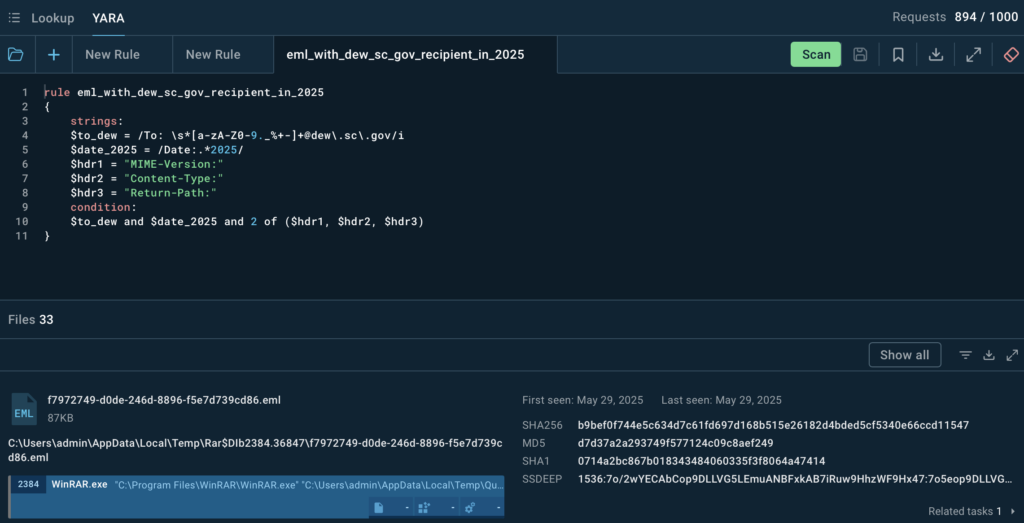
- Phishing emails targeting the South Carolina Department of Employment and Workforce were detected using YARA rules and sandbox analysis, revealing the use of FormBook stealer malware.
- A fraudulent domain mimicking the U.S. Social Security Administration was identified distributing malware that deploys ScreenConnect for remote access.
- ANY.RUN’s Threat Intelligence Lookup discovered multiple malicious domains spoofing government ministries, including ministries of foreign affairs.
- A malicious PDF disguised as a South African Judiciary notice was analyzed, revealing its use for credential-harvesting through a fake Microsoft Office 365 login page.
- Sandbox analysis combined with Suricata network detection highlighted malware behaviors and attack patterns in all studied cases.
- ANY.RUN’s YARA Search and TI Lookup facilitate scalable tracking of phishing campaigns and threat actor tactics across government sectors.
- Recommendations emphasize proactive threat hunting, real-time analysis, staff phishing awareness, and integrating automated threat intelligence feeds for government cybersecurity teams.
MITRE Techniques
- [T1552.001] Credentials in Files – FormBook malware used in phishing emails to steal credentials by accessing files. (“FormBook activity detected with credential theft behaviors.”)
- [T1518] Software Discovery – FormBook also performed software discovery to gather environment information. (“Execution chain showing software reconnaissance techniques.”)
- [T1219] Remote Access Software – ScreenConnect remote administration tool deployed via malicious executable from fraudulent SSA domain. (“ScreenConnect remote administration tool deployed after execution.”)
- [T1071.001] Application Layer Protocol: Web Protocols – Network traffic from FormBook and ScreenConnect detected through characteristic HTTP headers and unusual port connections. (“Suricata detected HTTP headers and network connections indicative of malware.”)
Indicators of Compromise
- [IP Address] Email sender IP used in FormBook phishing email failing SPF, DKIM, and DMARC checks – example: unauthorized 163.com sending IP address.
- [File Hash] PDF embedded image hash associated with South African Judiciary fake notice – dfbbc198e7cb36ca31a5cb9dfd859955c4366b94f4a87c2a03102d60168eb74d and 17 more hashes.
- [Domain] Malicious domains impersonating government agencies – documentssagov.com, multiple .mofa domains flagged as malicious.
- [File Name] Malicious executable and attachment names – “Quotation.exe” (FormBook), “SSA_Document.exe” (ScreenConnect), “SUMMON COURT DEMAND DOCUMENT.html” (phishing credential page).
Read more: https://any.run/cybersecurity-blog/cybersecurity-blog/how-to-investigate-government-cyber-attacks/