CVE-2026-31431, nicknamed “Copy Fail,” is a Linux kernel vulnerability in the algif_aead userspace crypto interface that allows an unprivileged local user to corrupt page cache backing setuid binaries and gain root within seconds. A public ~700-byte PoC leverages AF_ALG + splice() to stage shellcode into /usr/bin/su across major distributions; patches are available in Linux 7.0, 6.19.12 and 6.18.22 and runtime detection via AF_ALG socket monitoring (Sysdig/Falco rules) is recommended. #CVE-2026-31431 #CopyFail
Keypoints
- Copy Fail (CVE-2026-31431) is a local privilege escalation in the kernel’s algif_aead interface that corrupts page-cache pages of setuid binaries via AF_ALG + splice().
- The bug was introduced in 2017 by commit 72548b093ee3 when AEAD ops were switched to in-place processing and was reverted by a fix ending with commit fafe0fa2995a in early April 2026.
- A public PoC (~700 bytes of Python) chains three primitives (AF_ALG bind, splice of /usr/bin/su page cache, recvmsg AAD write) to deposit a four-byte scratch write and stage shellcode, yielding a root shell when su is executed.
- Affected kernels include 4.14 through 7.0-rc and 6.18.x prior to 6.18.22 and 6.19.x prior to 6.19.12; downstream LTS backports (e.g., 6.12.x, 6.6.x, 5.15.x, 5.10.x) may also be vulnerable; fixed in 7.0, 6.19.12 and 6.18.22.
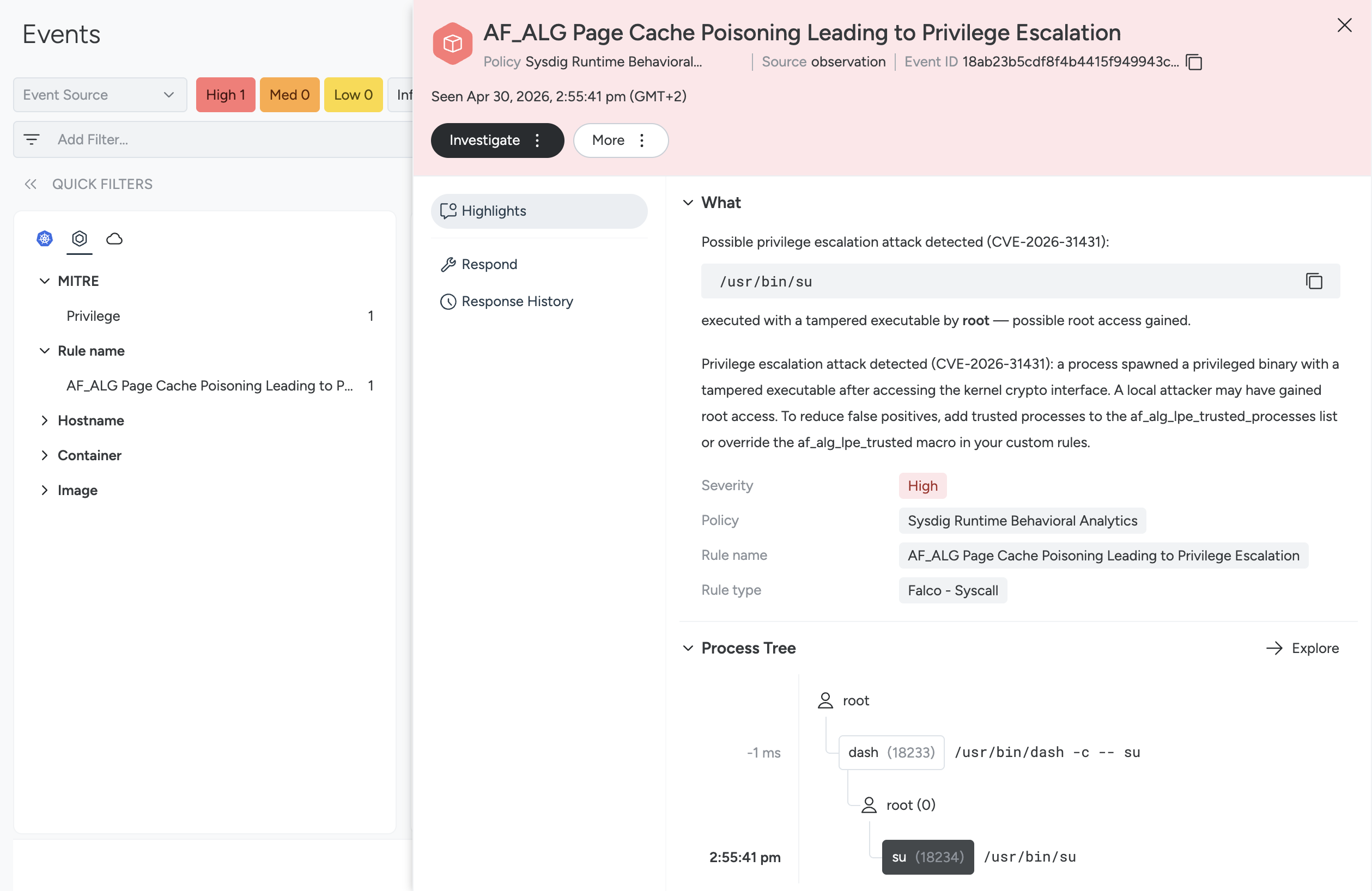
- Detection and mitigation options: apply kernel updates, restrict AF_ALG via seccomp/runtime defaults or disable CONFIG_CRYPTO_USER_API_AEAD, deploy Sysdig/Falco rules to flag unexpected AF_ALG SEQPACKET sockets and monitor setuid binary modifications.
- Exploit is reliable and trivial compared with Dirty Pipe; any local unprivileged user (or attacker with initial code execution) can escalate to root without race conditions or distribution-specific timing tricks.
MITRE Techniques
- [T1068 ] Exploitation for Privilege Escalation – Kernel AEAD API (AF_ALG) + splice() is used to corrupt page-cache of setuid binaries and escalate privileges (‘Any local unprivileged user on a vulnerable kernel can gain root access.’)
Indicators of Compromise
- [CVE ] vulnerability identifier – CVE-2026-31431
- [Repository ] public PoC – theori-io/copy-fail-CVE-2026-31431 (public Python PoC)
- [Commit hashes ] regression and fix context – 72548b093ee3 (regression commit, 2017), fafe0fa2995a (fix revert commit)
- [Kernel versions ] affected/fixed kernel ranges – vulnerable: 4.14 through 7.0-rc and 6.18.x prior to 6.18.22, 6.19.x prior to 6.19.12; fixed: 7.0, 6.19.12, 6.18.22
- [File names ] targeted setuid binary context – /usr/bin/su (page-cache corruption target) and other setuid binaries
- [Distributions ] examples of impacted downstream systems – Ubuntu 24.04, Amazon Linux 2023, RHEL 10.1, SUSE 16
- [Binaries list ] Falco known AF_ALG users (detection allowlist) – cryptsetup, systemd-cryptsetup, and other disk-encryption toolchain binaries