Check Point Research revealed a sophisticated campaign by the APT group Stealth Falcon exploiting a zero-day vulnerability (CVE-2025-33053) through malicious .url files to deliver custom malware implants such as the Horus Agent. The group targets government and defense sectors in the Middle East and Africa using spear-phishing, WebDAV exploitation, and customized post-exploitation tools including keyloggers and credential dumpers. #StealthFalcon #CVE2025-33053 #HorusAgent
Keypoints
- Stealth Falcon exploited CVE-2025-33053, a zero-day vulnerability allowing remote code execution via manipulation of the working directory in .url files linked to actor-controlled WebDAV servers.
- The infection chain involves multi-stage loaders like the Horus Loader and custom implants based on the Mythic C2 framework, including the advanced Horus Agent and a customized Apollo agent.
- The Horus Loader employs code virtualization, anti-analysis, and anti-detection techniques, decrypting payloads disguised as IPv6 addresses (“IPfuscation”) and executing decoy documents to evade detection.
- Stealth Falcon leverages LOLBins and WebDAV, combining multiple legitimate Windows tools for stealthy malware deployment through spear-phishing campaigns targeting governmental and defense organizations.
- The group’s post-compromise toolset includes a DC Credential Dumper operating on virtual disk copies to steal locked system credential files, a passive AES-encrypted backdoor, and a DLL-based keylogger without C2 functionality.
- The Horus Agent communicates with C2 servers using encrypted JSON packets and supports commands focused on system fingerprinting, shellcode injection, file management, and task control, with sophisticated anti-analysis methods.
- Stealth Falcon consistently uses older legitimate domains to host infrastructure, enhancing stealth and complicating attribution, while their advanced obfuscation and customization hinder reverse engineering and detection.
MITRE Techniques
- [T1192] Spearphishing Link – Delivery via spear-phishing emails containing .url files and phishing attachments directing victims to actor-controlled WebDAV servers.
- [T1105] Ingress Tool Transfer – Use of WebDAV servers to host and deliver malicious payloads including route.exe loader and subsequent implants.
- [T1055] Process Injection – Horus Agent and loaders inject shellcode into legitimate processes using multiple injection methods, including stealth injection and remote thread creation (‘…the loader creates a suspended process and injects the payload…’).
- [T1036] Masquerading – Use of legitimate system utilities such as iediagcmd.exe and CustomShellHost.exe with manipulated working directories to execute attacker-controlled files.
- [T1140] Deobfuscate/Decode Files or Information – Payloads are obfuscated using code virtualization, RC4, XOR, and custom encryption for strings and configuration data (‘…Horus Agent uses string encryption and control flow flattening…’).
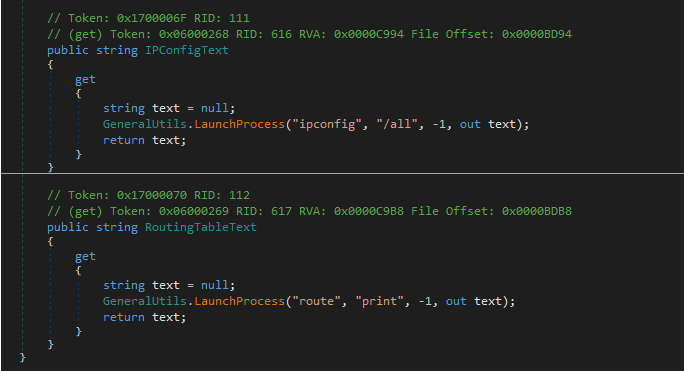
- [T1083] File and Directory Discovery – Custom survey commands enumerate system services, processes, battery status, user, and network configuration via WMI queries and API calls.
- [T1119] Automated Collection – DC Credential Dumper extracts locked credential files by reading virtual disk copies of the system drive.
- [T1059] Command and Scripting Interpreter – Abuse of LOLBins like cmd.exe, DeviceCredentialDeployment.exe, and forfiles.exe to execute attacker commands stealthily.
- [T1574] Hijack Execution Flow – Use of .url files manipulating working directories to hijack execution of system tools.
- [T1573] Encrypted Channel – Use of AES with HMAC-SHA256 for encrypted C2 communications (‘…the sent data is encrypted with AES with HMAC for integrity…’).
Indicators of Compromise
- [File Hash] Samples and components – Horus Loader (ddce79afe9f67b78e83f6e530c3e03265533eb3f4530e7c89fdc357f7093a80b), Horus Agent (1d95a44f341435da50878eea1ec0a1aab6ae0ee91644c497378266290a6ef1d8), custom Apollo (700b422556f070325b327325e31ddf597f98cc319f29ef8638c7b0508c632cee), keylogger components, passive backdoor, and credential dumper loaders.
- [Domain] Malicious infrastructure – summerartcamp[.]net, roundedbullets[.]com, downloadessays[.]net, joinushealth[.]com, healthherofit[.]com, worryfreetransport[.]com, radiotimesignal[.]com, and others primarily using .net and .com TLDs.
- [File Name] Malicious lure and loader files – TLM.005TELESKOPIKMASTHASARBILDIRIM_RAPORU.pdf.url, Supplier.lnk, and CPL loader files named after Star Trek characters such as JeanLucPicardbrownie.cpl.
Read more: https://research.checkpoint.com/2025/stealth-falcon-zero-day/