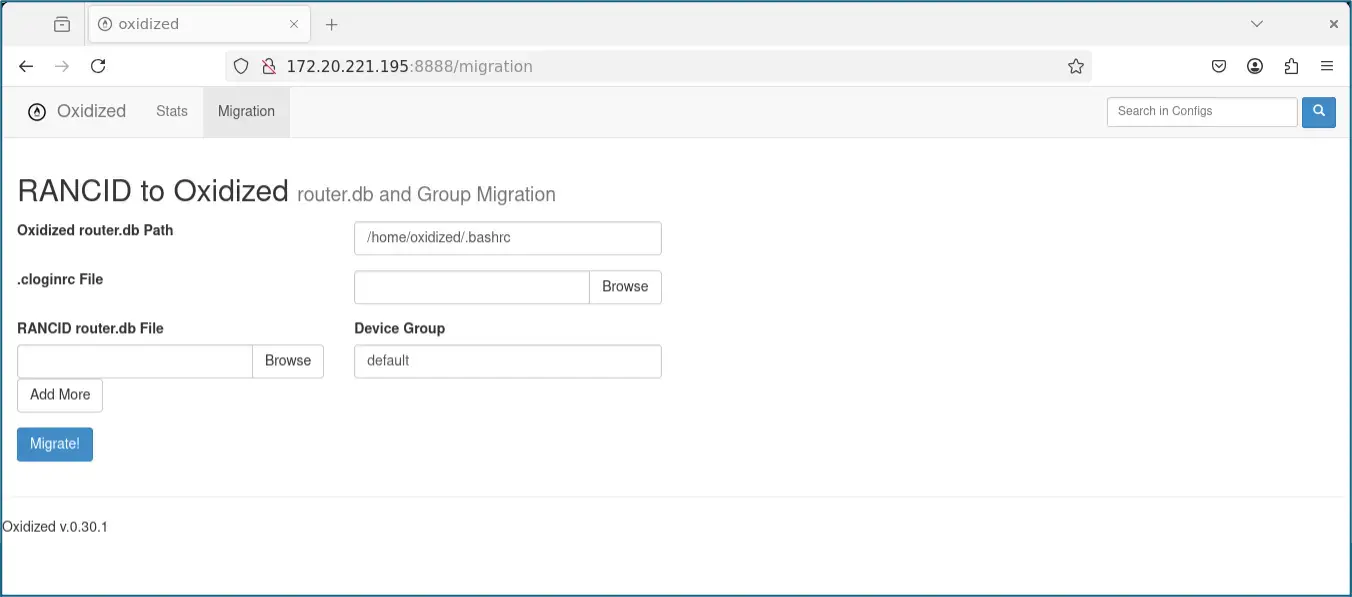
The NetSPI red team identified a vulnerability in Oxidized Web v0.14, where an attacker could exploit a data validation issue in the /migration page to overwrite arbitrary files, gaining remote code execution. This vulnerability has been fixed in version 0.15. Affected: Oxidized Web, routers, switches, server security
Keypoints :
- NetSPI found a vulnerability in the Oxidized Web application during a security engagement.
- Oxidized Web is a tool for managing router and switch configurations.
- A data validation issue allowed for arbitrary file overwrite via the /migration page.
- The vulnerability enabled code execution on the server through the overwritten ~/.bashrc file.
- The vulnerability was tracked as CVE-2025-27590.
- The development team quickly remediated the issue by removing the deprecated migration script in version 0.15.
- Restricting access to the Oxidized Web interface is recommended.
MITRE Techniques :
- T1070.001 – Indicator Removal on Host: Clear logs or evidence of unauthorized access
- T1036.004 – Masquerading: Rename files or directories to appear as system files
- T1203 – Exploitation for Client Execution: Use of browser to execute malicious requests
Indicator of Compromise :
- [URL] http://172.20.221.195:8888/migration
- [Domain] 172.20.221.195
- [File] ~/.bashrc
- [File] ~/.ssh/authorized_keys
- [MD5] – Not applicable, no MD5 hashes provided
Full Story: https://www.netspi.com/blog/technical-blog/web-application-pentesting/cve-2025-27590-oxidized-web-rce/