CVE-2025-24054 is a vulnerability that allows NTLM hash disclosure through spoofing methods, primarily via a malicious .library-ms file. Active exploits have targeted institutions in Poland and Romania, posing significant risk for password leakage and system compromise. Microsoft issued a patch on March 11, 2025, but attackers exploited the flaw just days later. Affected: NTLM authentication systems, Government institutions, Private sectors in Poland and Romania
Keypoints :
- CVE-2025-24054 enables NTLM hash disclosure via spoofing using a .library-ms file.
- Active exploitation commenced shortly after the patch release on March 11, 2025.
- Vulnerabilities were exploited in campaigns targeting Polish and Romanian institutions.
- Malspam campaigns utilized Dropbox links to distribute malicious archives.
- NTLMv2-SSP hashes can be leaked with minimal user interaction.
- The vulnerability is similar to CVE-2024-43451, also previously patched.
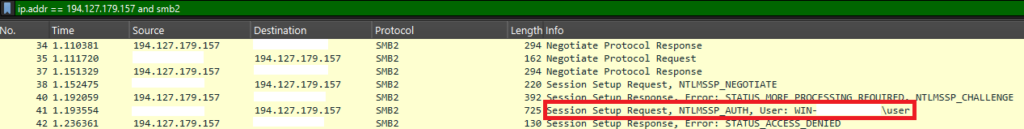
- Threat actors used malicious SMB servers for data harvesting.
- Microsoft’s patch documentation indicates exploitation can occur without unzipping files.
- New campaigns continued to emerge, expanding the scope of the vulnerability’s exploitation.
MITRE Techniques :
- T1071.001: Application Layer Protocol – SMB used to leak NTLM hashes.
- T1071: Application Layer Protocol – Exploited using .library-ms and other files to initiate SMB connections.
- T1203: Exploitation for Client Execution – Users exploited through the extraction of malicious files.
- T1074: Data Staged – Data exfiltration via SMB for NTLM hash harvesting.
- T1046: Network Service Scanning – Attackers scanned for vulnerable systems to exploit the flaw.
Indicator of Compromise :
- [IP Address] 159.196.128[.]120
- [IP Address] 194.127.179[.]157
- [Hash] 9ca72d969d7c5494a30e996324c6c0fcb72ae1aexd.website
- [Hash] 84132ae00239e15b50c1a20126000eed29388100xd.url
- [Hash] 7dd0131dd4660be562bc869675772e58a1e3ac8exd.library-ms
Full Story: https://research.checkpoint.com/2025/cve-2025-24054-ntlm-exploit-in-the-wild/