This blog entry discusses the emerging ransomware group CrazyHunter, which is threatening Taiwan’s essential services by targeting crucial sectors like healthcare, education, and industry. Utilizing sophisticated attack techniques, including BYOVD, and a variety of open-source tools, CrazyHunter poses a significant risk to the operational integrity of its victims. Affected: Taiwan, healthcare sector, education sector, industrial sector
Keypoints :
- CrazyHunter is a significant ransomware threat targeting organizations in Taiwan.
- Critical sectors being targeted include healthcare, education, and industrial organizations.
- Utilizes sophisticated techniques like the Bring Your Own Vulnerable Driver (BYOVD) method to bypass security measures.
- Approximately 80% of CrazyHunter’s toolkit comprises open-source tools, enhancing their operational capabilities.
- Trend Vision One™ actively detects and counters malicious components from CrazyHunter’s campaigns.
- The group has specialized their attacks to focus exclusively on Taiwan, impacting small and medium-sized businesses.
- They have incorporated customized ransomware variants and scripts for efficient execution and deployment.
- Security recommendations emphasize the need for proactive measures against ransomware threats.
MITRE Techniques :
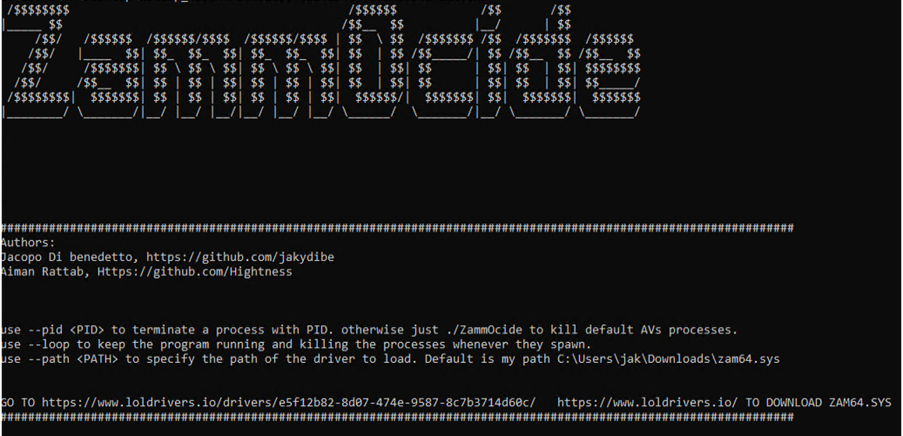
- Defense Evasion (T1562.001): Uses a tailored variant of ZammoCide to terminate processes associated with security solutions.
- Privilege Escalation (T1068): Exploits Group Policy Objects (GPO) through the SharpGPOAbuse tool to gain higher privileges.
- Impact (Ransomware) (T1486): Deploys a variant of Prince ransomware, which uses encryption to secure files and modify victim’s desktop settings.
- Exfiltration (T1041): Utilizes “file.exe” as a monitoring tool for potential exfiltration and to track changes in web-related files.
- Execution (T1203): Uses batch scripts to execute multiple binaries, effectively deploying the ransomware payload while evading detection.
Indicator of Compromise :
- [Email Address] payment[.]attack-tw1337@proton[.]me
- [Domain] zam64.sys
- [Executable] go2.exe
- [Executable] go.exe
- [Executable] file.exe
Full Story: https://www.trendmicro.com/en_us/research/25/d/crazyhunter-campaign.html