The report identifies three cryptocurrency companies—BlockNovas LLC, Angeloper Agency, and SoftGlide LLC—as fronts for the North Korean APT group known as Contagious Interview. Through fake job offers, they deploy various strains of malware, including BeaverTail, InvisibleFerret, and OtterCookie, targeting unsuspecting cryptocurrency job seekers. The threat actors utilize AI-generated employee profiles and exploit job listing platforms to execute their scheme. Affected: BlockNovas LLC, Angeloper Agency, SoftGlide LLC, Job Seekers, Cryptocurrency Sector
Keypoints :
- Three cryptocurrency companies are identified as fronts for the North Korean APT group Contagious Interview.
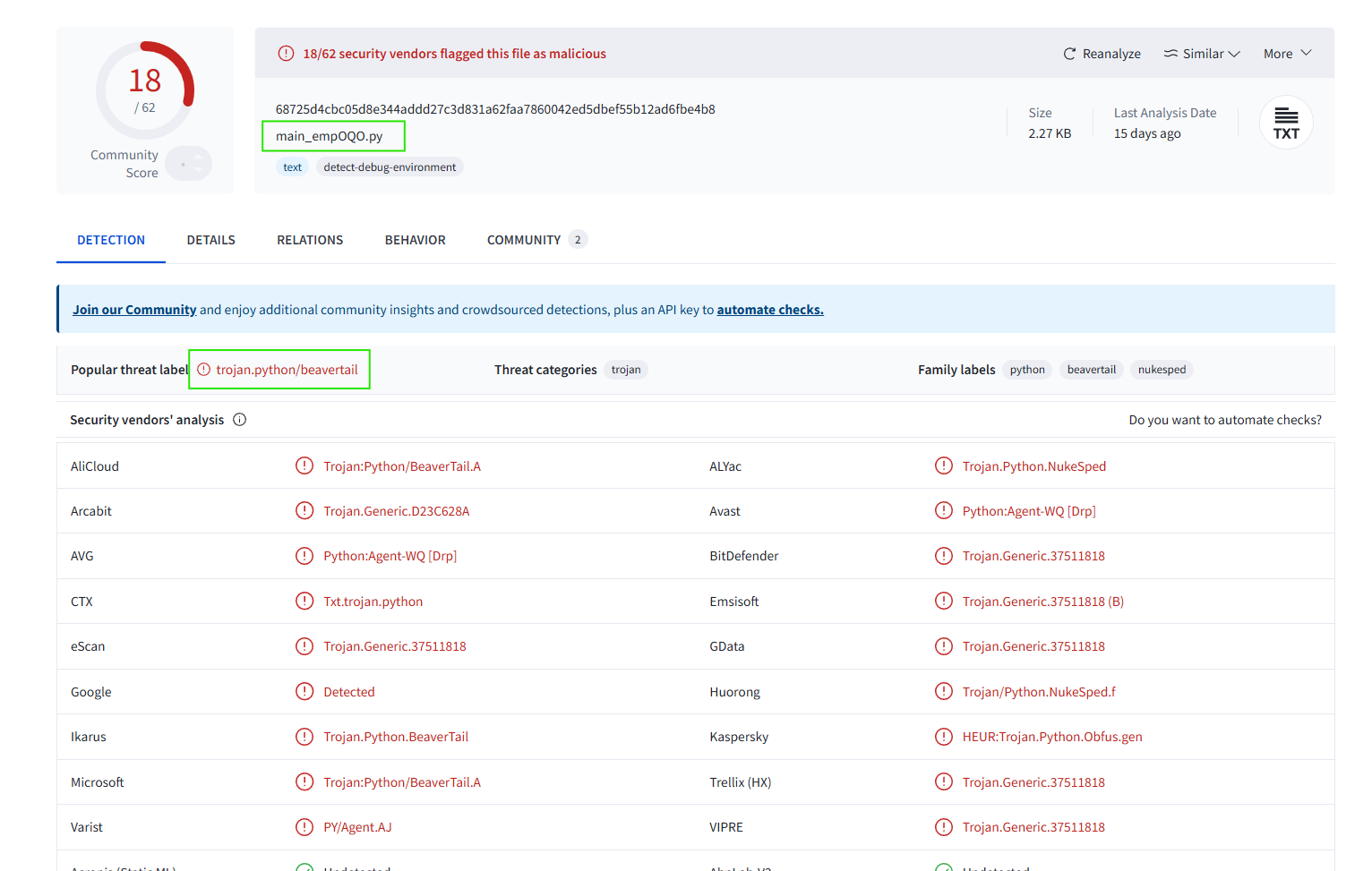
- Malware strains being used include BeaverTail, InvisibleFerret, and OtterCookie.
- AI-generated images are employed to create fake employee profiles.
- The threat actors use job interview lures to distribute malware.
- Several job listing and freelancer websites are exploited in these attacks.
- Technical infrastructure, including command and control domains, supports the malware distribution.
- Persistent fake identities are created by the threat actors to enhance credibility.
MITRE Techniques :
- T1071.001 – Application Layer Protocol: The actors use HTTP protocols to communicate with malware C2 servers.
- T0872.001 – Malware Delivery: Delivery methods exploited include fake job offers and links to malicious GitHub projects.
- T1203 – Exploitation for Client Execution: Executable code is triggered upon unsuspecting user action.
- T1105 – Ingress Tool Transfer: Malicious payloads are transferred from external domains to victim systems.
- T1086 – PowerShell: PowerShell is utilized to execute the malware payload on victim devices.
Indicator of Compromise :
- [Domain] blocknovas[.]com
- [Domain] angeloper[.]com
- [Domain] softglide[.]co
- [Domain] lianxinxiao[.]com
- [IP Address] 37.211.126[.]117
Full Story: https://www.silentpush.com/blog/contagious-interview-front-companies/