This article discusses the ClickFix technique used by adversaries to deliver malware, particularly highlighting its association with the Lumma Stealer. The ClickFix method involves social engineering, tricking users into executing malicious commands through seemingly legitimate interfaces. Suggestions for detection and prevention using Logpoint SIEM are also provided. Affected: malware delivery, social engineering, infostealer malware
Keypoints :
- ClickFix has become a popular method for delivering malware among nation-state actors.
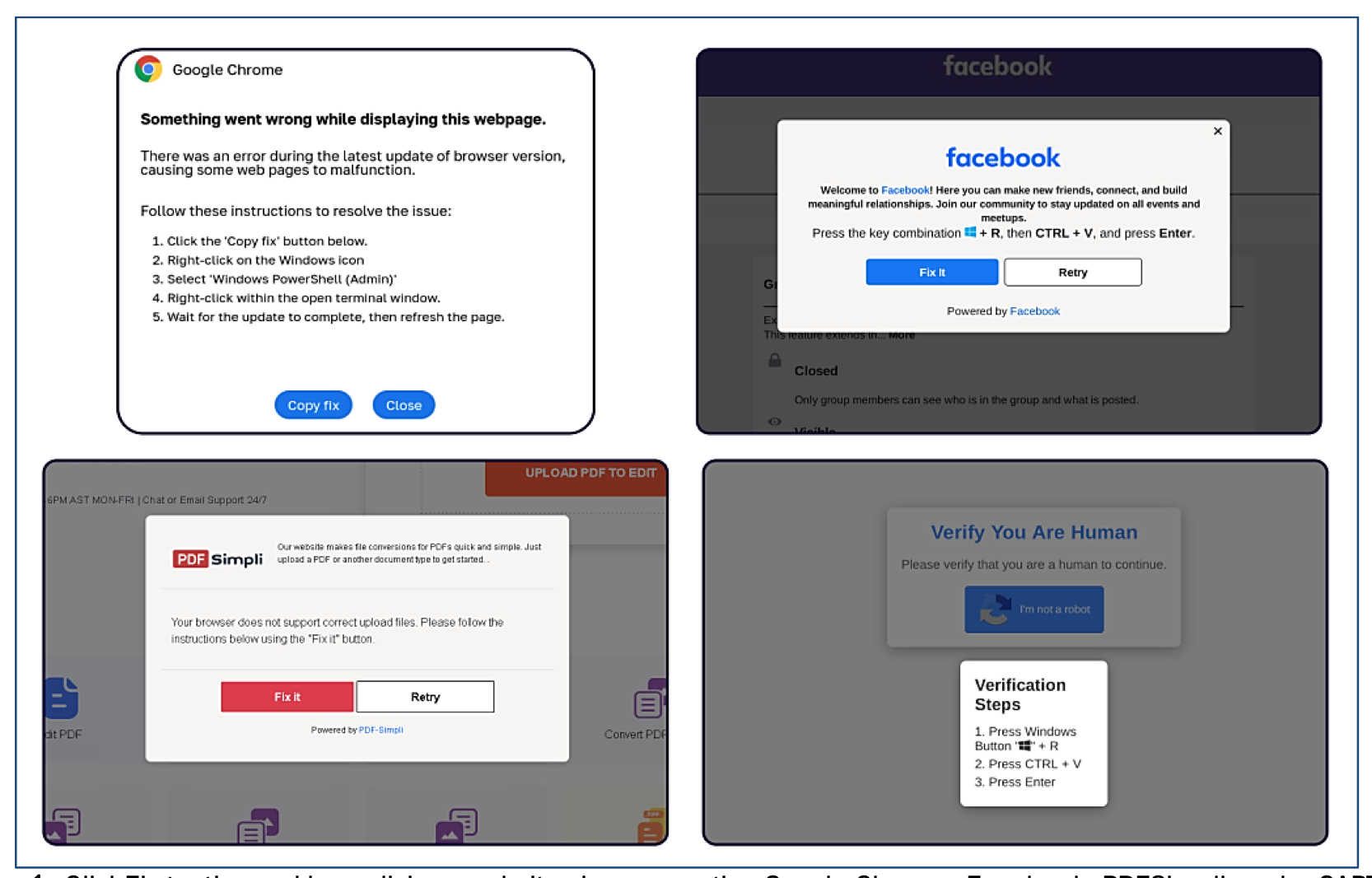
- The technique deceives users into executing malicious code by using fake prompts on compromised websites.
- Common targets for ClickFix include Google Chrome, Facebook, and reCAPTCHA impersonations.
- Adversaries often use multiple techniques like spear phishing and malvertising to direct users to ClickFix sites.
- Lumma Stealer is frequently associated with ClickFix campaigns.
- The exploitation of legitimate Windows binaries (LOLBINS) like mshta.exe is a dominant technique in these attacks.
- Detection strategies involve monitoring process creations, suspicious PowerShell commands, and log data to identify malicious activities.
- Organizations are encouraged to adopt defense-in-depth strategies and conduct regular employee training to mitigate risks.
MITRE Techniques :
- Tactic: Initial Access, Technique: Spear Phishing Link (T1566.001) – Use of social engineering techniques to trick users into visiting compromised websites.
- Tactic: Execution, Technique: User Execution (T1204.002) – Users are deceived into executing malicious commands.
- Tactic: Execution, Technique: Windows Management Instrumentation (T1047) – Abuse of mshta.exe to execute malicious scripts directly.
- Tactic: Credential Access, Technique: Input Capture (T1056) – Adversaries use ClickFix to capture user input under the guise of benign actions.
- Tactic: Persistence, Technique: Windows Service (T1050) – Malicious code is implemented via legitimate binaries that run persistently in the background.
Indicator of Compromise :
- [URL] hxxps://sokolia[.]shop/ladderupfun[.]mp3
- [URL] hxxp://aatox[.]com/verify/45.ps1
- [Domains] googIedrivers[.]com
- [Hash] MD5: 92a8cc4e385f170db300de8d423686eeeec72a32475a9356d967bee9e3453138
- [Hash] MD5: 2853a61188b4446be57543858adcc704e8534326d4d84ac44a60743b1a44cbfe
Full Story: https://www.logpoint.com/en/blog/emerging-threats/clickfix-another-deceptive-social-engineering-technique/