This article discusses the cyber espionage campaign CL-STA-0048, attributed to a Chinese threat actor targeting high-value organizations in South Asia, particularly in the telecommunications sector. The attackers utilized advanced techniques such as Hex Staging and DNS exfiltration, aiming to steal sensitive data and personal information from government employees. Affected: telecommunications organizations, government entities
Keypoints :
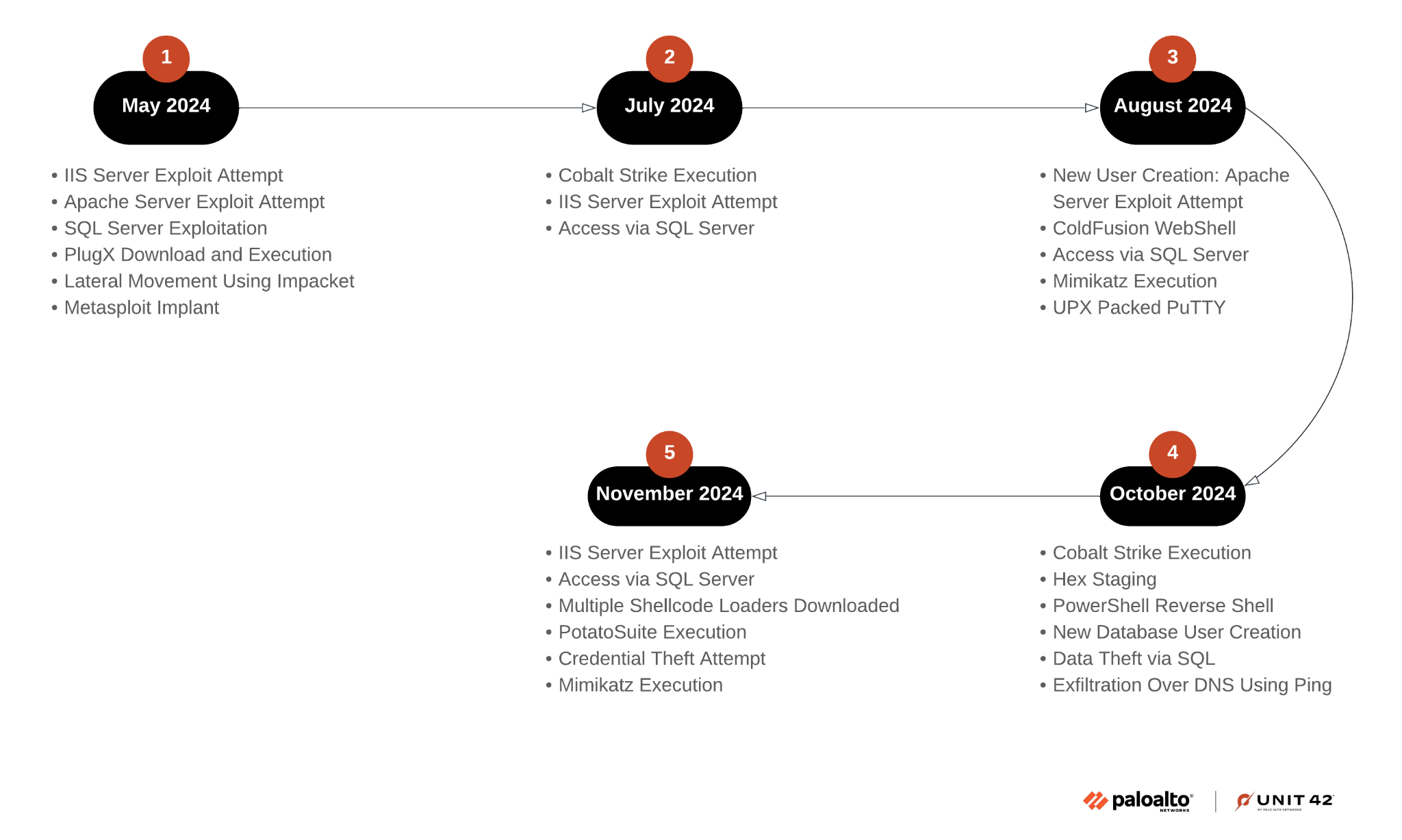
- Identification of the CL-STA-0048 activity cluster targeting South Asian high-value organizations.
- Use of rare tools and techniques, including Hex Staging and DNS exfiltration.
- Moderate-high confidence assessment of the campaign’s origin in China.
- Targeting of IIS, Apache Tomcat, and MSSQL services to exploit known vulnerabilities.
- Focus on obtaining personal information of government employees and sensitive data theft.
- Recommendations for organizations to patch vulnerabilities and improve IT hygiene.
- Utilization of advanced threat protection tools like Cortex XDR by Palo Alto Networks.
MITRE Techniques :
- T1027: Obfuscated Files or Information – The attackers used Hex Staging to deliver payloads in chunks, avoiding detection.
- T1041: Exfiltration Over Command and Control Channel – Data was exfiltrated using DNS requests triggered by ping commands.
- T1071: Application Layer Protocol – The threat actor used SoftEther VPN for stealthy communications.
- T1059: Command and Scripting Interpreter – PowerShell scripts were leveraged for executing commands and exfiltrating data.
- T1210: Exploitation of Remote Services – Exploited vulnerabilities in IIS, Apache Tomcat, and MSSQL services.
Indicator of Compromise :
- [domain] mail.tttseo[.]com
- [domain] h5.nasa6[.]com
- [ip address] 154.201.68[.]57
- [ip address] 43.247.135[.]106
- [file hash] 525540eac2d90c94dd3352c7dd624720ff2119082807e2670785aed77746301d
- Check the article for all found IoCs.
Full Research: https://unit42.paloaltonetworks.com/espionage-campaign-targets-south-asian-entities/