Chinese nation-state APT groups exploited an unauthenticated file upload vulnerability (CVE-2025-31324) in SAP NetWeaver Visual Composer to gain persistent remote access to critical infrastructure networks globally. This wide-ranging campaign targeted essential services and government entities across multiple countries, using sophisticated webshells and multi-stage malware to maintain stealthy control and enable espionage. #APT, #SAPNetWeaver, #CVE202531324, #China, #CriticalInfrastructure, #Webshell, #Malware
Keypoints
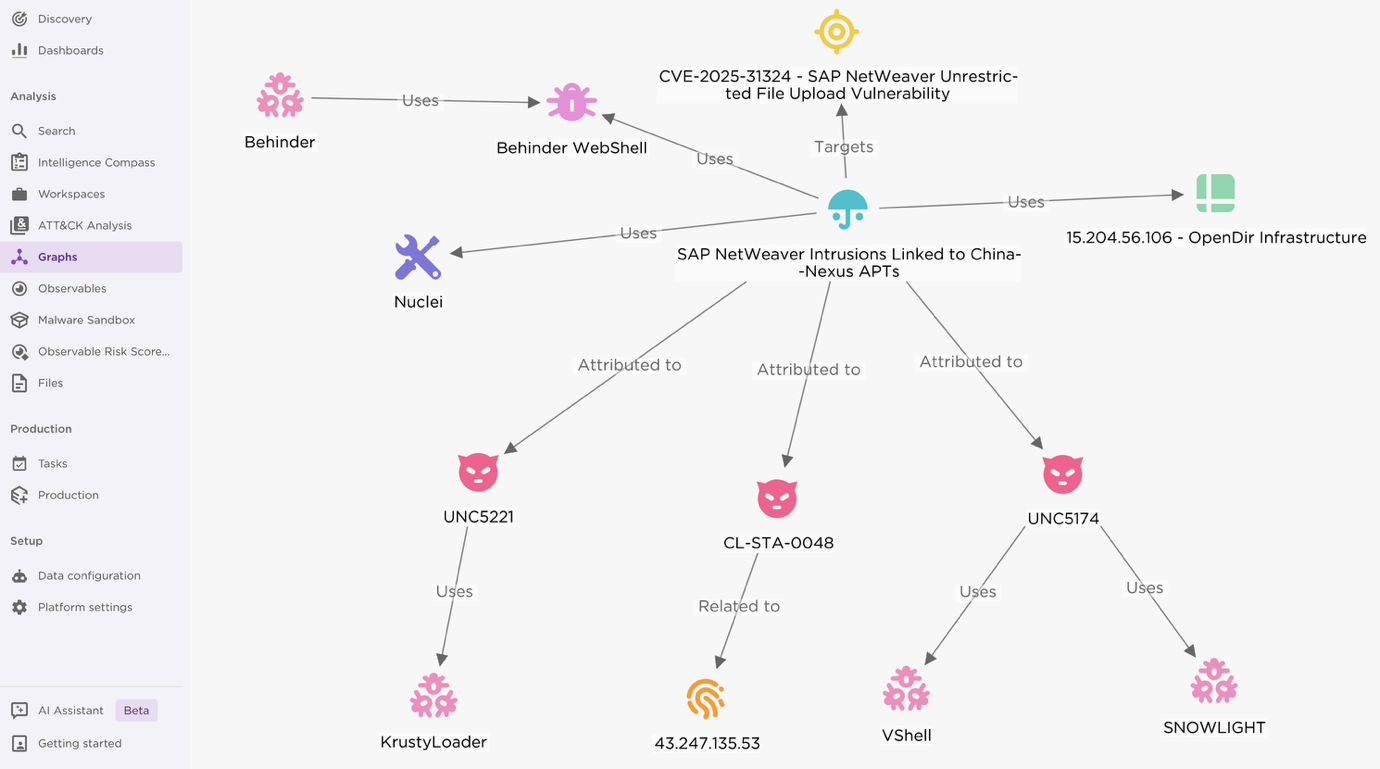
- Multiple China-linked APT groups including UNC5221, UNC5174, and CL-STA-0048 exploited CVE-2025-31324 in SAP NetWeaver Visual Composer for remote code execution and persistent access.
- Attackers hosted open directories revealing detailed logs of 581 compromised SAP NetWeaver instances and 1,800 additional targets across critical sectors worldwide.
- Two main webshells, coreasp.js (AES encrypted, fileless execution) and forwardsap.jsp (unauthenticated command execution), were deployed for stealthy post-exploitation access.
- The campaign primarily targeted essential services such as UK energy and water utilities, US medical device manufacturers, and Saudi Arabian government ministries.
- Threat actors used multi-stage malware loaders including KrustyLoader (Rust-based) and SNOWLIGHT downloader, combined with VShell and GOREVERSE RATs, for in-memory execution and evasion.
- Command-and-control infrastructure involved multiple IPs and domains, including the CL-STA-0048-linked sentinelones.com and Amazon S3-hosted payload distribution.
- Recommended mitigations include applying SAP Security Note #3594142, restricting access to vulnerable endpoints, and monitoring for specific webshell indicators and network anomalies.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Exploitation of SAP NetWeaver Visual Composer CVE-2025-31324 enabling unauthenticated file upload and remote code execution (“…unauthenticated file upload vulnerability…”).
- [T1105] Ingress Tool Transfer – Use of curl and wget to download malware from attacker-controlled Amazon S3 buckets (“…Linux Bash one-liners to retrieve and decode base64-encoded KrustyLoader payload hosted on Amazon S3…”).
- [T1059] Command and Scripting Interpreter – Execution of Bash and other shell commands via webshells coreasp.js and forwardsap.jsp, enabling remote command execution (“…accepts system commands via a query parameter named cmdhghgghhdd…”).
- [T1027] Obfuscated Files or Information – KrustyLoader performs multi-step decryption including hex decoding, XOR and AES-128-CFB to decrypt payloads (“…decrypts a hardcoded staging URL using a three-step obfuscation chain…”).
- [T1566] Phishing (implied) – Use of DNS beaconing with ping commands for covert communication (“…sent a ping command to a subdomain of *.oastify.com…”).
- [T1210] Exploitation of Remote Services – Deployment of multiple webshells to maintain persistence and enable lateral movement within victim networks (“…uploaded to SAP NetWeaver systems after a POST request to the API endpoint: /developmentserver/metadatauploader”).
- [T1090] Proxy – Use of proxy domains and trusted cloud services like AWS S3 to mask malicious traffic and payload delivery (“…threat actors abused the legitimate AWS cloud service to mask its malicious activity…”).
Indicators of Compromise
- [IP Addresses] C2 and infrastructure IPs involved in exploitation and persistence – 15.204.56[.]106 (opendir server), 43.247.135[.]53 (sentinelones.com C2), 103.30.76[.]206 (SNOWLIGHT C2), 54.77.139[.]23, and 3.248.33[.]252 (related to DNS beaconing and Fortinet reports).
- [Domains] Attacker hosting and payload delivery – applr-malbbal.s3.ap-northeast-2.amazonaws[.]com, abode-dashboard-media.s3.ap-south-1.amazonaws[.]com, brandnav-cms-storage.s3.amazonaws[.]com (AWS S3 buckets for KrustyLoader), sentinelones[.]com (C2 domain).
- [File Names] Deployed webshell files – coreasp.js, forwardsap.jsp, helper.jsp, cache.jsp, usage.jsp, .webhelper.jsp, 404_error.jsp, .h.jsp.
- [File Hashes] Malware and payload hashes linked to KrustyLoader, SNOWLIGHT, and GOREVERSE campaigns – multiple SHA256 hashes provided for these samples (e.g., f92d0cf4d577c68aa615797d1704f40b14810d98b48834b241dd5c9963e113ec).