Threat actors have evolved the delivery of Lumma Stealer by leveraging trusted cloud storage platforms like Tigris, OCI, and Scaleway to host fake reCAPTCHA pages, tricking privileged users into executing malicious commands. Additionally, earlier campaigns targeted gamers through Steam-like domains distributing malicious payloads via cracked software downloads. #LummaStealer #TigrisObjectStorage #OracleCloudInfrastructure #ScalewayObjectStorage #my-steamunlocked.online
Keypoints
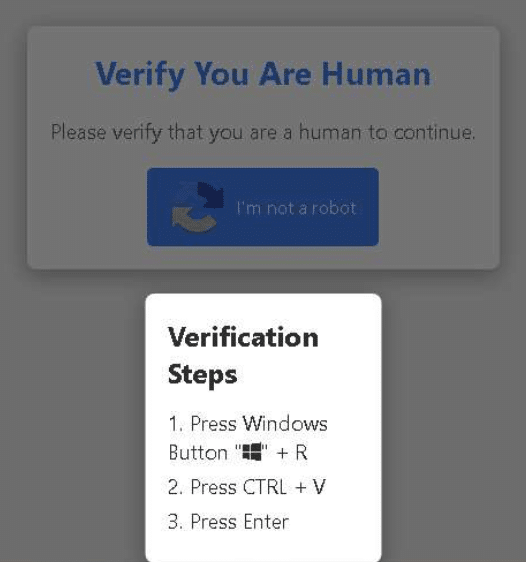
- Threat actors host fake reCAPTCHA pages on cloud storage platforms (Tigris, OCI, Scaleway) to target privileged users within organizations, leading to execution of Lumma Stealer malware.
- Delivery involves instructing users to press Windows + R and run malicious clipboard-injected PowerShell commands that launch mshta.exe to fetch disguised trojan files.
- Code samples contain Russian-language comments, suggesting possible involvement of Russian-speaking threat actors.
- Earlier Lumma Stealer campaigns targeted gamers via malvertising and Steam-impersonating domains distributing cracked software laced with DLL search order hijacking techniques.
- Malware uses advanced obfuscation, security software detection, and AutoIt-based loaders to evade antivirus and detection mechanisms.
- Cato MDR service proactively blocked fake reCAPTCHA redirection attempts using high-confidence IPS rules, protecting customers from the threat.
- Cloud providers Tigris and Scaleway have removed malicious content following disclosure; Oracle has not yet responded.
MITRE Techniques
- [T1583.006] Acquire Infrastructure – Web Services – Fake reCAPTCHA pages hosted on cloud platforms (Tigris, OCI, Scaleway) used as attack infrastructure (“Tigris Object Storage has been leveraged by threat actors to host fake reCAPTCHA pages”).
- [T1204.004] User Execution – Malicious Copy and Paste – Victims coerced to open Windows Run dialog and paste PowerShell commands from clipboard to execute malware (“Users tricked into running clipboard-injected PowerShell via Windows + R”).
- [T1059.001] Command and Scripting Interpreter: PowerShell – PowerShell commands used to silently invoke mshta.exe to fetch trojan payloads (“PowerShell launches mshta.exe to fetch disguised trojan”).
- [T1218.005] Signed Binary Proxy Execution (mshta.exe) – mshta.exe, a legitimate signed Windows binary, exploited to execute remote HTA trojan files (“PowerShell command invoking mshta.exe, a legitimate Windows binary commonly leveraged by threat actors”).
- [T1036.008] Masquerading: Masquerade File Type – Malicious payloads disguised as seemingly benign media files with deceptive extensions (.mp4, .mp3) (“Malicious HTA masqueraded as other file type”).
- [T1059.003] Command and Scripting Interpreter – Windows Command Shell – Batch scripts used in malware execution and obfuscation (“Obfuscated batch script located in the %temp% folder”).
- [T1059.010] Command and Scripting Interpreter – AutoHotKey & AutoIT – AutoIt scripts constructed and executed to load Lumma Stealer payloads in memory (“the script constructs a .com file… an AutoIt3-based executable”).
- [T1574.001] Hijack Execution Flow – DLL Search Order Hijacking – Modified DLL (MpGear.dll) used alongside renamed Setup.exe to hijack execution flow (“DLL hijacking via Microsoft-signed setup.exe using LOLBins”).
- [T1036] Masquerading – Use of Steam-like domain to impersonate legitimate brand and lure victims (“domain crafted to mimic the Steam platform”).
- [T1036.001] Masquerading – Invalid Code Signature – Malicious DLLs and executables with invalid or obfuscated signatures (“modified DLL crafted for DLL hijacking”).
- [T1027.013] Obfuscated Files or Information – Encrypted/Encoded File – Script and malware components heavily obfuscated and encoded to hamper analysis (“script’s ultimate goal is to execute a heavily obfuscated n.a3x AutoIT script”).
- [T1518.001] Software Discovery – Security Software Discovery – Batch script checks for presence of antivirus software before proceeding (“script performs security scan using tasklist.exe and findstr.exe to detect known antivirus tools”).
Indicators of Compromise
- [Malicious Domains/URLs] Fake reCAPTCHA hosting – fly.storage.tigris.dev/jinglebellringing/hidjanam-showing-next-go.html, objectstorage.ap-seoul-1.oraclecloud.com/n/id0cu93izlqm/b/need-to-complete-this/o/dest.html, datastream-dist.s3.pl-waw.scw.cloud/pass-this-for-access-prism.html
- [Malicious Domains/URLs] Masqueraded media payloads – amacys.shop/sports.mp4, beckhamin.shop/deflowev1.mp4, numbros.site/mishticplayrz.mp4
- [Malicious Domains] Malicious redirectors – my-steamunlocked.online (Steam impersonation), wq24-1.g-site.store, wq24-1.g-site.site
- [DLL File] MpGear.dll – Used for DLL search order hijacking (hash: fa2ebe7df2fcf7e0b9991d411792e0cb78d149833b2d06102ab34d74ffc4a682)
- [ZIP File] D0wnl0@d C0mp!3t3 L@t3st PC Setup.zip – Archive containing malicious files (hash: 1544ee1ab897a791b4c2eeb9a8936e5aae331de1308b08f74aadbc24856c73a2)
- [Executable File] setup.exe – Signed binary used as legitimate loader (hash: 66b8074eb73353ad0a966e4a41016e0e6aa9a9fed697a0f98a1fb65db765a195)
- [Script File] n.a3x – AutoIt script executing Lumma Stealer payload in memory (hash: 91747f5254ccddee9de4a01f959236c1d1fda06f6ba2d2664f16dfb9e2db4175)
Read more: https://www.catonetworks.com/blog/cato-ctrl-suspected-russian-threat-actors/