This webcast explores the potential security implications of using Microsoft Co-Pilot, including its role as an insider threat, licensing options, and security measures. The discussion highlights how AI tools like Co-Pilot can both assist employees and pose risks if not properly secured. #MicrosoftCoPilot #AIInsiderThreats
Category: Youtube
The video discusses the vulnerability of authenticated command injection in the ping command on IoT devices’ web management interfaces. Many IoT systems allow users to run ping commands remotely, which can be exploited due to insecure implementation. #IoTSecurity #CommandInjection

The video discusses the superficial nature of age verification systems that rely solely on image recognition, which can easily be bypassed. It critiques the effectiveness of such non-functional safeguards, emphasizing they are more about compliance than security. #ImageVerification #AgeVerification
This video highlights the widespread issue of data breaches, with over 15 billion accounts leaked on the dark web, including major companies like Facebook and Samsung. It emphasizes the importance of using unique, strong passwords for every account and recommends tools like password managers. #HaveIBeenPwned #TroyHunt
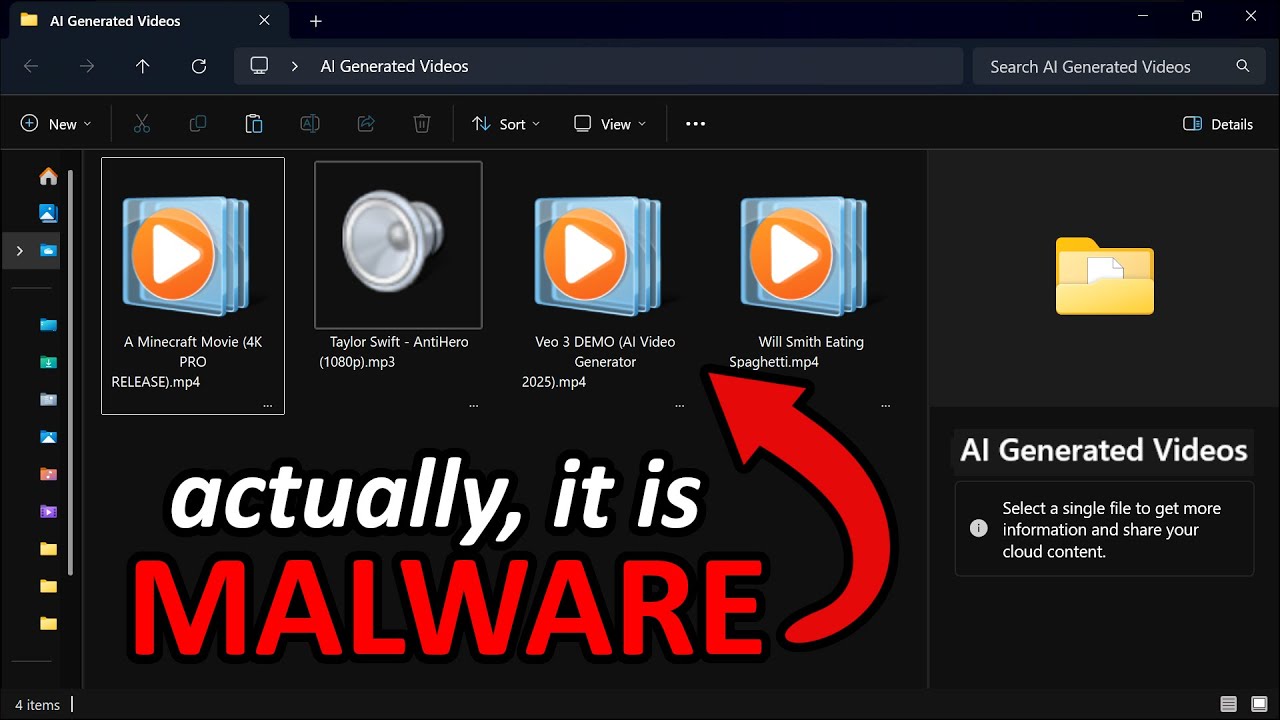
This video discusses how cybercriminals exploit fake AI websites to distribute malware, including payloads like info stealers and backdoors. It also demonstrates a PowerShell script to create malicious files with Unicode padding, effectively hiding executable extensions in Windows. #AIWebsites #UnicodePadding

The speaker reflects on advice they would give their 18-year-old self, emphasizing the importance of work-life balance and not taking life too seriously. They acknowledge that learning this balance has taken time to achieve. #WorkLifeBalance #LifeAdvice

The video explains that antivirus (AV) and Endpoint Detection and Response (EDR) are distinct technologies, despite often being mistaken for each other. It highlights the differences in their architecture and usage, emphasizing that they are separate solutions that serve different purposes. #EDR #Antivirus
This video explains how triage processes, traditionally done by humans like nurses and emergency responders, can be automated using Triage AI Agents. These AI systems imitate human decision-making to prioritize and route cases efficiently across various sectors such as healthcare, auto repair, and cybersecurity. #TriageAI #AutomatedPrioritization

This article introduces a new taxonomy for strategic questions, categorizing them into investigative, speculative, productive, interpretive, and subjective types. These categories help improve decision-making by focusing on different scopes and depths of inquiry, from root cause analysis to broad prevention strategies. #StrategicQuestions #DecisionMaking

This video introduces Graph Retrieval Augmented Generation (GraphRAG), a method that utilizes knowledge graphs and large language models (LLMs) for advanced data retrieval and query answering. Unlike vector search, GraphRAG leverages structured graph data and Cypher queries for more contextual and comprehensive insights. #Neo4j #GraphRAG

A new vulnerability prediction metric called LEV is being tested by NIST and CISA to improve the identification of exploited vulnerabilities. Meanwhile, Signal reacts to Microsoft’s Recall feature by disabling screenshots on Windows 11, and AI-assisted discovery finds a Linux kernel flaw CVE-202537899. #LEVMetrics #LinuxCVE202537899

This video provides an inside look into the realities of working as a software engineer and cybersecurity analyst, highlighting differences in deployment times, vulnerability management, and project types. It emphasizes the importance of continuous learning and adaptability in the fast-changing tech industry. #Docker #CI/CD

This episode concludes season one of Simply ICS Cyber, featuring discussions on the role of Idaho National Laboratory in cybersecurity and industrial control systems. The conversation highlights the importance of Cyberinformed Engineering (CIE) in enhancing infrastructure resilience and safety. #IdahoNationalLab #CyberinformedEngineering
![BHIS – Talkin’ Bout [infosec] News 2025-05-27 #livestream #infosec #infosecnews BHIS – Talkin’ Bout [infosec] News 2025-05-27 #livestream #infosec #infosecnews](https://img.youtube.com/vi/sziLqlBbBQ0/maxresdefault.jpg)
This transcript covers a wide range of topics including experimental AI behaviors like blackmailing engineers, advancements in drone technology for law enforcement, and recent cybersecurity incidents such as data breaches and info stealer takedowns. It also discusses the impact of geopolitical factors on hacker conferences and the evolving use of AI in various applications. #Anthropic #FlockSafety
This video explains how Windows shortcut files can be exploited to deliver malware and extract sensitive data like NLM hashes without user interaction. Attacks leverage techniques such as self-referencing icons and cloud proxying to evade detection, highlighting advanced social engineering and bypass strategies. #NLMHashLeak #PowerShellExploit
