This video discusses how cybercriminals exploit fake AI websites to distribute malware, including payloads like info stealers and backdoors. It also demonstrates a PowerShell script to create malicious files with Unicode padding, effectively hiding executable extensions in Windows. #AIWebsites #UnicodePadding
Keypoints :
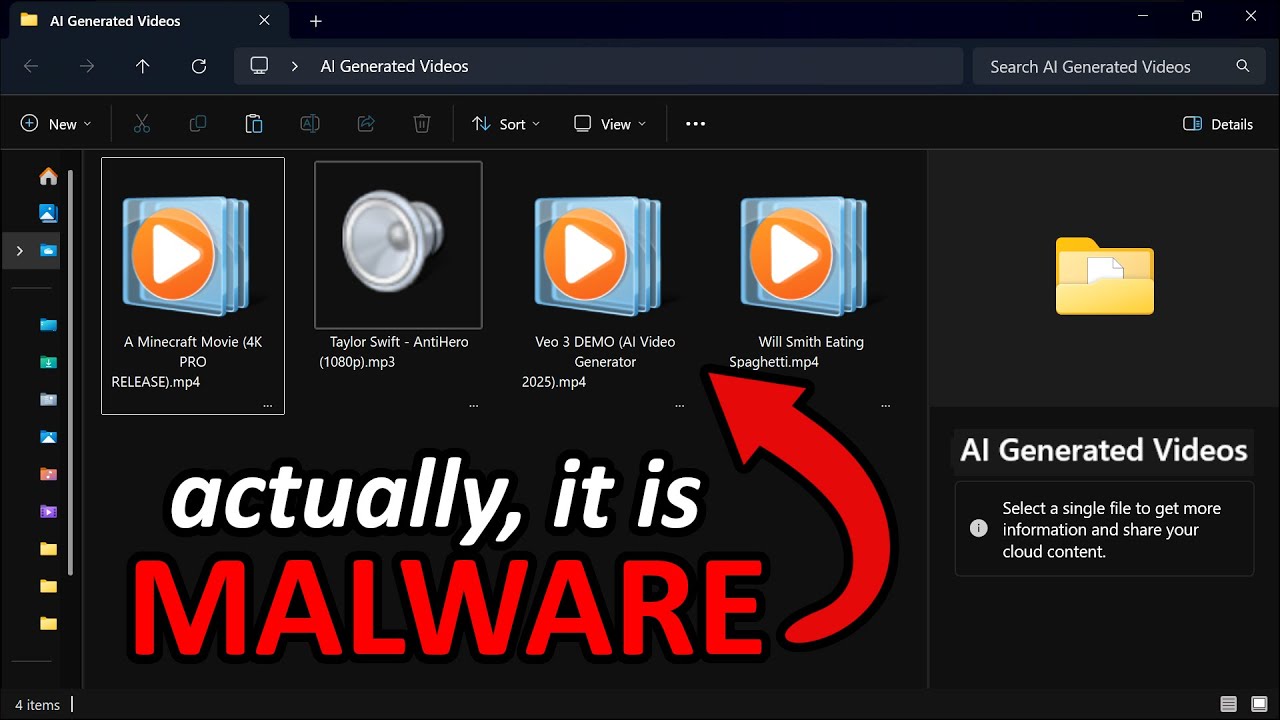
- Threat actors use fake AI video generator websites to spread malware via social media ads targeting millions of users.
- Malware payloads include Python-based info stealers, backdoors, and traffic through the Tor network for command and control.
- Files are disguised with Unicode braille characters and multiple spaces to hide executable extensions like .exe in Windows Explorer.
- A PowerShell script automates bulk renaming of files, inserting Unicode characters, and padding filenames to conceal malicious payloads.
- Malicious files often contain double extensions and icons to mimic legitimate media files, tricking users into execution.
- Detection strategies include monitoring filenames with Unicode characters using Sigma rules or endpoint detection tools like Aurora.
- The video emphasizes the importance of blue team tactics to recognize and mitigate such obfuscation techniques.
- Youtube Video: https://www.youtube.com/watch?v=aj3uBl9hFxY
- Youtube Channel: John Hammond
- Youtube Published: Thu, 29 May 2025 13:00:06 +0000