More than 30 WordPress plugins in the EssentialPlugin package were found to contain a backdoor that allows unauthorized access to sites using them. The dormant backdoor, introduced after the project’s August 2025 acquisition, was recently activated to fetch wp-comments-posts.php which injects invisible malware into wp-config.php and delivers spam pages and redirects via an Ethereum-based C2. #EssentialPlugin #AnchorHosting
Category: Cyber Security News

Ukrainian cyber defenders warned of an intensified campaign by threat cluster UAC-0247 targeting hospitals, emergency services, municipal bodies, and defense-linked users with phishing lures disguised as humanitarian aid. Attackers deploy multi-stage loaders, custom executable formats and backdoors like AGINGFLY—alongside tools such as SILENTLOOP and RAVENSHELL—to gain persistent remote control, steal credentials,…

Microsoft awarded $2.3 million to security researchers after nearly 700 submissions to this year’s Zero Day Quest, where over 80 high-impact cloud and AI vulnerabilities were identified during a live event at its Redmond campus. The contest, part of Microsoft’s Secure Future Initiative, increased its prize pool to $5 million and will share findings via the CVE program to strengthen cloud and AI security. #ZeroDayQuest #Microsoft

A digitally signed adware tool distributed by Dragon Boss Solutions LLC uses an Advanced Installer update mechanism to silently deploy MSI and PowerShell payloads that run with SYSTEM privileges and disable antivirus protections on thousands of endpoints across education, utilities, government, and healthcare sectors. Huntress researchers sinkholed the unregistered update domain after observing over 23,500 infected hosts in 124 countries and warn the existing infrastructure and AV-killing mechanism could be leveraged to push far more dangerous payloads. #DragonBossSolutions #ClockRemoval

Several major ad companies allegedly ignored Global Privacy Control opt-out signals on California websites, with webXray finding 194 advertising services failing to honor user opt-outs. The report claims Google, Microsoft, and Meta frequently set advertising cookies despite GPC signals, raising potential CCPA violations and echoing past fines against companies like Sephora…

Researchers reveal a new alliance between Iranian threat actor Muddy Water and Russian-speaking cybercriminals operating the CastleRAT (TAG-150) MaaS, marking a capability upgrade from simple scripts to professional-grade intrusion tools. The group now deploys a JavaScript-based ChainShell via a reset.ps1 loader, uses HVNC for invisible browser session hijacking, and resolves C2…

Capsule Security, an Israeli startup founded in 2025 by Naor Paz and Lidan Hazout, emerged from stealth with $7 million in seed funding to add a runtime security layer for agentic AI. The Tel Aviv-based platform continuously monitors agents’ reasoning, interactions, and execution across frameworks to intervene on anomalous behavior, prevent…

A critical vulnerability in the Nginx UI web management interface (CVE-2026-33032) tied to its MCP AI integration has been exploited in the wild and can allow unauthenticated attackers to take full control of exposed servers. Pluto Security found over 2,600 internet-exposed instances, technical details and a public PoC exist, and the…

Sweden says a pro‑Russian group with links to Russia’s security and intelligence services carried out a cyberattack last year against a heating plant in western Sweden, but the attack failed. Officials in Poland, Norway, Denmark and Latvia have reported similar incidents targeting critical infrastructure — including combined heat and power plants,…

Trucks are rolling networks full of connected sensors, telematics, ELDs, and cloud services, creating extensive attack surfaces that cybercriminals exploit for ransomware, extortion, and cyber-enabled cargo theft. Industry groups like NMFTA are promoting tailored cybersecurity guidance, best practices, and collaboration through conferences to help carriers reduce risk with measures such as MFA, network segmentation, and patching. #NMFTA #VeriskCargoNet

CISA warned U.S. federal agencies to secure systems against a Windows Task Host privilege escalation vulnerability that could allow local attackers to obtain SYSTEM privileges. Tracked as CVE-2025-60710 and patched by Microsoft in November 2025, the link-following flaw affects Windows 11 and Windows Server 2025 and prompted a two-week remediation order for FCEB agencies. #CVE-2025-60710 #TaskHost

Ross McKerchar describes his 18-year journey from Sophos’s first internal security engineer to CISO, explaining how leadership, recruitment, and team management differ from technical training. He outlines key challenges including senior-level skills gaps, AI-driven attack evolution, burnout, legal limits around retaliation, and a growing trust problem in security products. #Sophos #PacificRim…

More than 20,000 users installed 108 malicious Chrome extensions published from five developer accounts (GameGen, InterAlt, SideGames, Rodeo Games, Yana Project) that appear to be a single coordinated campaign sharing command-and-control infrastructure. The extensions steal Google accounts via OAuth2, hijack Telegram Web sessions, open arbitrary C&C URLs at browser startup, inject…
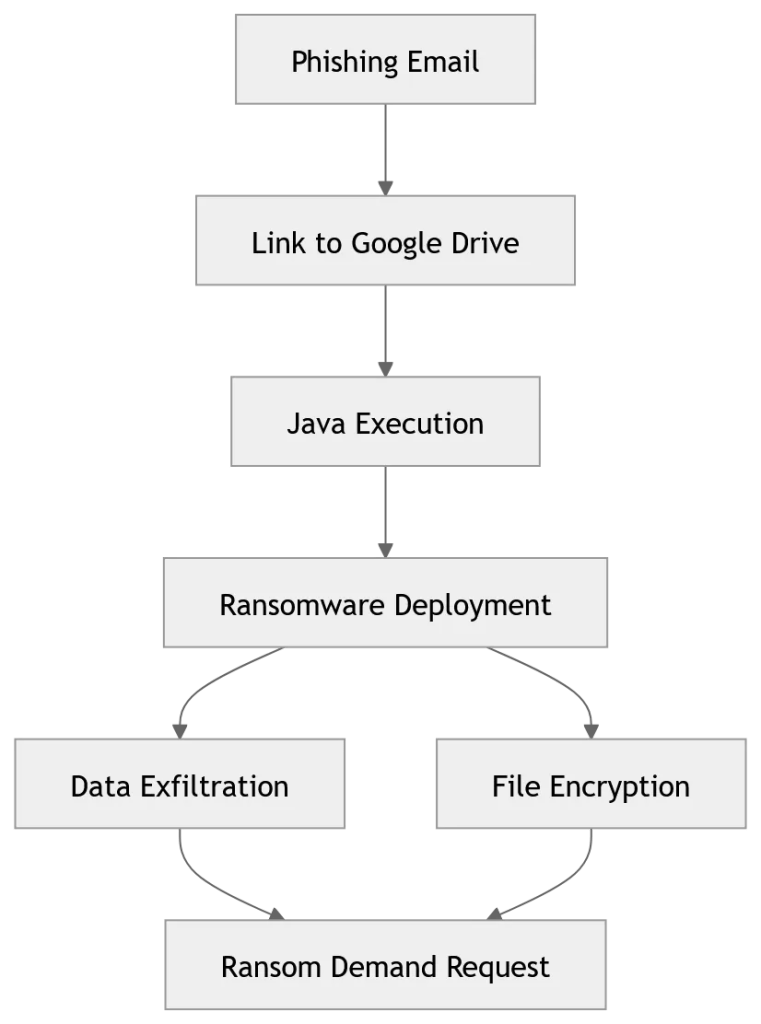
Researchers at Acronis TRU identified a long-running JanaWare campaign active since at least 2020 that targets users in Turkey using a customized, polymorphic Adwind RAT and extensive obfuscation to evade detection. The operation spreads via phishing-delivered Java archives, employs geofencing and Turkish-language ransom notes, disables security controls before delivering an AES…

OpenAI is expanding its Trusted Access for Cyber (TAC) program and launching GPT 5.4 Cyber to provide vetted defenders with advanced AI tools for defensive cybersecurity workflows. The move uses identity-verified access tiers and phased rollouts to scale defensive capabilities while managing dual-use risks. #OpenAI #GPT5.4Cyber…
