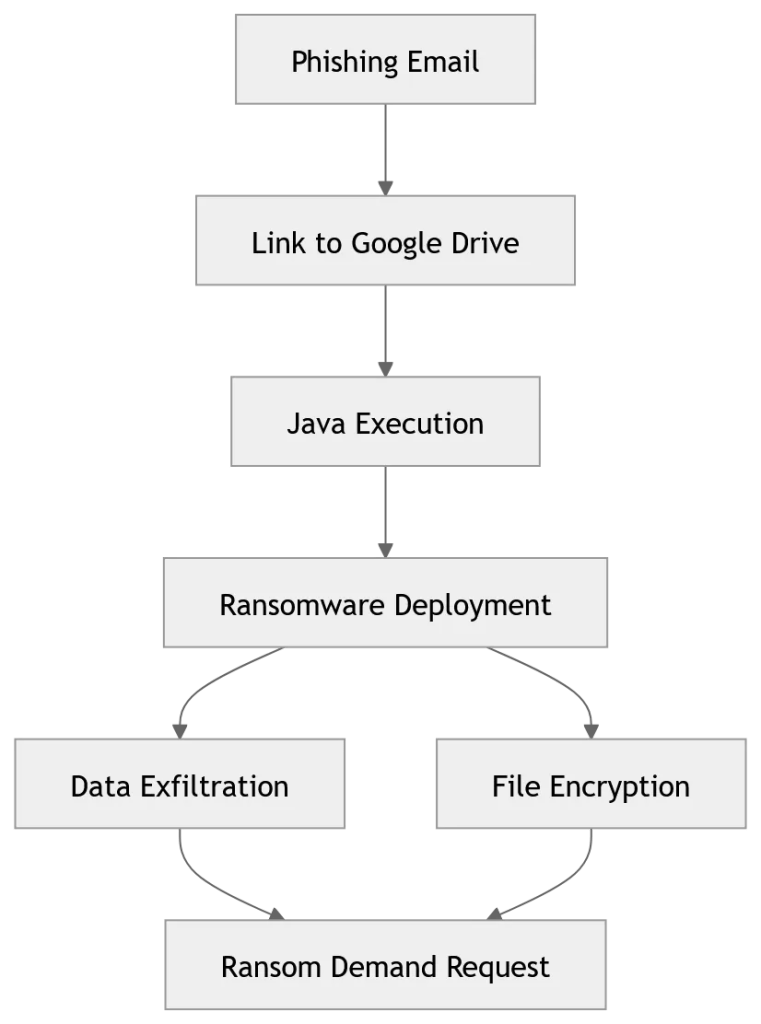
Researchers at Acronis TRU identified a long-running JanaWare campaign active since at least 2020 that targets users in Turkey using a customized, polymorphic Adwind RAT and extensive obfuscation to evade detection. The operation spreads via phishing-delivered Java archives, employs geofencing and Turkish-language ransom notes, disables security controls before delivering an AES encryption module, and communicates over Tor. #JanaWare #Adwind
Keypoints
- Acronis TRU linked the JanaWare campaign to a customized Adwind RAT active from 2020 into late 2025.
- The malware uses polymorphism and obfuscation tools like Stringer and Allatori to hinder detection.
- Phishing emails delivering Java archive files hosted on cloud storage are the primary infection vector.
- Geofencing and Turkish-language ransom notes restrict operations to systems matching Turkish locale and IPs.
- The threat disables Microsoft Defender and recovery mechanisms, then deploys an AES encryption module that communicates over Tor while demanding modest ransoms.
Read More: https://thecyberexpress.com/janaware-ransomware-hits-turkish-users/