Grinex suffered a large-scale wallet breach that forced the Kyrgyzstan-based exchange to suspend trading after attackers stole roughly $13–15 million in USDT. Hackers rapidly moved and chain-hopped the funds across Ethereum, Tron and other wallets—consolidating about 45.9 million TRX—while investigators probe possible links to sanctioned ecosystems and unproven foreign-intelligence involvement. #Grinex…
Category: Cyber Security News
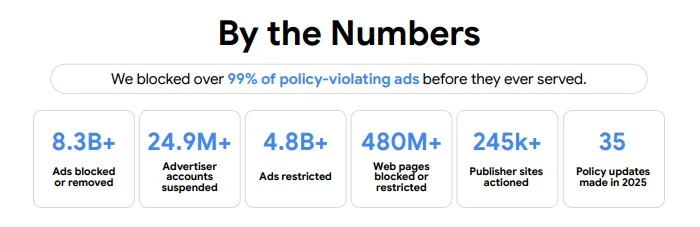
Google says its Gemini ad safety systems blocked more than 8.3 billion ads in 2025 and suspended nearly 25 million advertiser accounts, many linked to scam campaigns. The platform emphasizes early detection—analyzing intent, account behavior, and campaign patterns—to stop harmful and increasingly AI-generated scam ads before they go live. #Google #GeminiAdSafety…

A researcher known as “Chaotic Eclipse” published a proof-of-concept exploit called RedSun that abuses Microsoft Defender’s cloud file behavior to achieve local privilege escalation and obtain SYSTEM on fully patched Windows 10, Windows 11, and Windows Server. The release, following a prior BlueHammer PoC, was made in protest of the researcher’s treatment by Microsoft’s vulnerability response process. #RedSun #ChaoticEclipse

Threat actors are actively exploiting three recently disclosed Windows vulnerabilities—BlueHammer, RedSun, and UnDefend—to gain SYSTEM or elevated administrator permissions. Proof-of-concept exploit code was leaked by researcher “Chaotic Eclipse” (aka “Nightmare-Eclipse”) and Huntress Labs has observed all three zero-days in the wild, with BlueHammer patched as CVE-2026-33825 while RedSun and UnDefend remain unpatched. #BlueHammer #RedSun
![Cybersecurity News | Daily Recap [16 Apr 2026] Cybersecurity News | Daily Recap [16 Apr 2026]](https://www.hendryadrian.com/tweet/image/DailyRecap.png)
Daily Recap, Ukraine-linked UAC-0247 is intensifying attacks on hospitals and local governments using AgingFly, multi-stage loaders, and credential theft tooling to maintain persistence and deploy cryptominers, while a backdoored EssentialPlugin WordPress suite pushes malware via a hidden updater and Ethereum-based C2, and Dragon Boss Solutions’ digitally signed adware disables antivirus and runs payloads with SYSTEM privileges across thousands of hosts. Muddy Water is expanding its intrusion toolkit with CastleRAT and ChainShell, including HVNC hijacking and Ethereum-based C2 resolution, nginx-ui CVE-2026-33032 exploitation affecting 2,600+ exposed servers amid Patch Tuesday fixes for SAP, Adobe, Microsoft, and Fortinet, and related identity, data breach, and privacy developments. #AgingFly #EssentialPlugin #DragonBossSolutions #MuddyWater #CastleRAT #ChainShell #HVNC #NginxUI #CVE-2026-33032 #SAP #Adobe #Microsoft #Fortinet #ATHR #DPRK #PowerSchool #McGrawHill #EUAgeApp

Two New Jersey men were sentenced to nine years and nearly eight years for running a laptop-farm scheme that helped North Korean IT workers gain employment at over 100 U.S. companies and funneled more than $5 million to the DPRK. The operation used stolen U.S. identities and KVM-controlled laptops to enable…
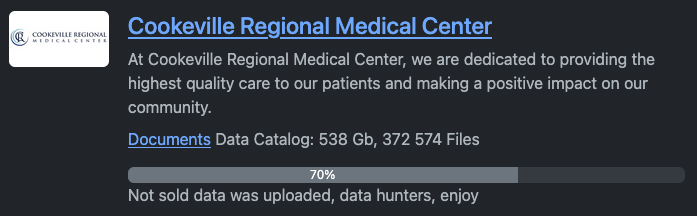
The Cookeville Regional Medical Center disclosed a July 14, 2025 network intrusion that led to a ransomware-related data breach affecting more than 337,000 individuals and reportedly resulting in roughly 370,000 stolen files totaling about 500 GB. The Rhysida group listed the data for sale for 10 bitcoin, later making it freely…
OpenAI launched GPT-5.4-Cyber, a fine-tuned GPT-5.4 variant that relaxes guardrails and adds capabilities like binary reverse engineering to help defenders analyze vulnerabilities and malicious behavior. The model will be distributed iteratively through an expanded Trusted Access for Cyber program for thousands of verified defenders and vetted security teams, contrasting with Anthropic’s…

The scale, speed, and sophistication of modern cyberattacks have outstripped what governments can defend alone, driven by expanded attack surfaces, third-party dependencies, industrialized cybercrime, and nation-state activity. A resilient national defense requires rapid public–private collaboration on threat intelligence, secure-by-design AI governance, and coordinated offensive actions to disrupt criminal infrastructure across borders….

The Education Authority investigation confirmed a targeted attack on a small number of schools that led to the compromise of some personal data. Authorities say the breach—identified on April 10, 2026—has been contained, forensic analysis and law enforcement involvement continue, and affected individuals and schools will be notified. #EducationAuthority #C2k…

ZionSiphon is a newly discovered OT-focused malware engineered to sabotage water treatment and desalination systems by manipulating hydraulic pressures and raising chlorine levels. Researchers at Darktrace found a flawed country-verification XOR logic that renders the current sample non-functional but warn that a minor fix could enable destructive actions and USB propagation targeting Israeli infrastructure. #ZionSiphon #Darktrace #Israel #Desalination

Operation PowerOFF, an international law enforcement campaign supported by Europol, targeted DDoS-for-hire platforms and warned over 75,000 users while resulting in arrests and domain takedowns. The operation dismantled booter-service infrastructure across 21 countries, seized criminal account databases, and is entering a prevention phase with awareness campaigns and search‑engine and on‑chain disruption measures. #OperationPowerOFF #Europol
Two U.S. nationals were sentenced for facilitating a North Korea IT worker scheme that used “laptop farms” and stolen American identities to place overseas operatives in remote IT roles at more than 100 U.S. companies, generating over $5 million for the DPRK. The investigation uncovered shell companies, covert remote-access setups, and…

Cisco released security updates addressing four critical vulnerabilities, including a Webex SSO certificate-validation flaw (CVE-2026-20184) that could let unauthenticated attackers impersonate users. Customers using SSO must upload a new SAML certificate to Control Hub, and Cisco also patched critical ISE flaws while noting no evidence of active exploitation. #Webex #CVE-2026-20184 #ControlHub #IdentityServicesEngine #Interlock #SecureFirewallManagementCenter

Attackers are exploiting a critical remote code execution flaw in the Marimo reactive Python notebook (CVE-2026-39987) to deploy a new variant of NKAbuse hosted on Hugging Face Spaces. Sysdig observed rapid post-disclosure exploitation that delivered a dropper and a kagent binary for persistence and remote access, and recommends upgrading to Marimo 0.23.0 or blocking the /terminal/ws endpoint if upgrading is not possible. #NKAbuse #Marimo
