The article explains how to build an AWS incident response playbook using open source tools, including the MCP server AWS-IReveal-MCP, within the Shared Responsibility Model to plan, detect, contain, eradicate, and recover from cloud incidents. It covers organizing AWS accounts with security and forensics OUs, leveraging services like CloudTrail, Athena, CloudWatch, GuardDuty, Config, Security Hub, and IAM, and provides practical steps for containment and post-incident analysis, including real-world mentions of affected buckets such as customers-keys and private-customers. #customers-keys #private-customers #AWS-IReveal-MCP
Keypoints
- Adopt an assume-breach mindset to improve cloud security readiness.
- Define and practice a comprehensive AWS incident response plan using multiple AWS services.
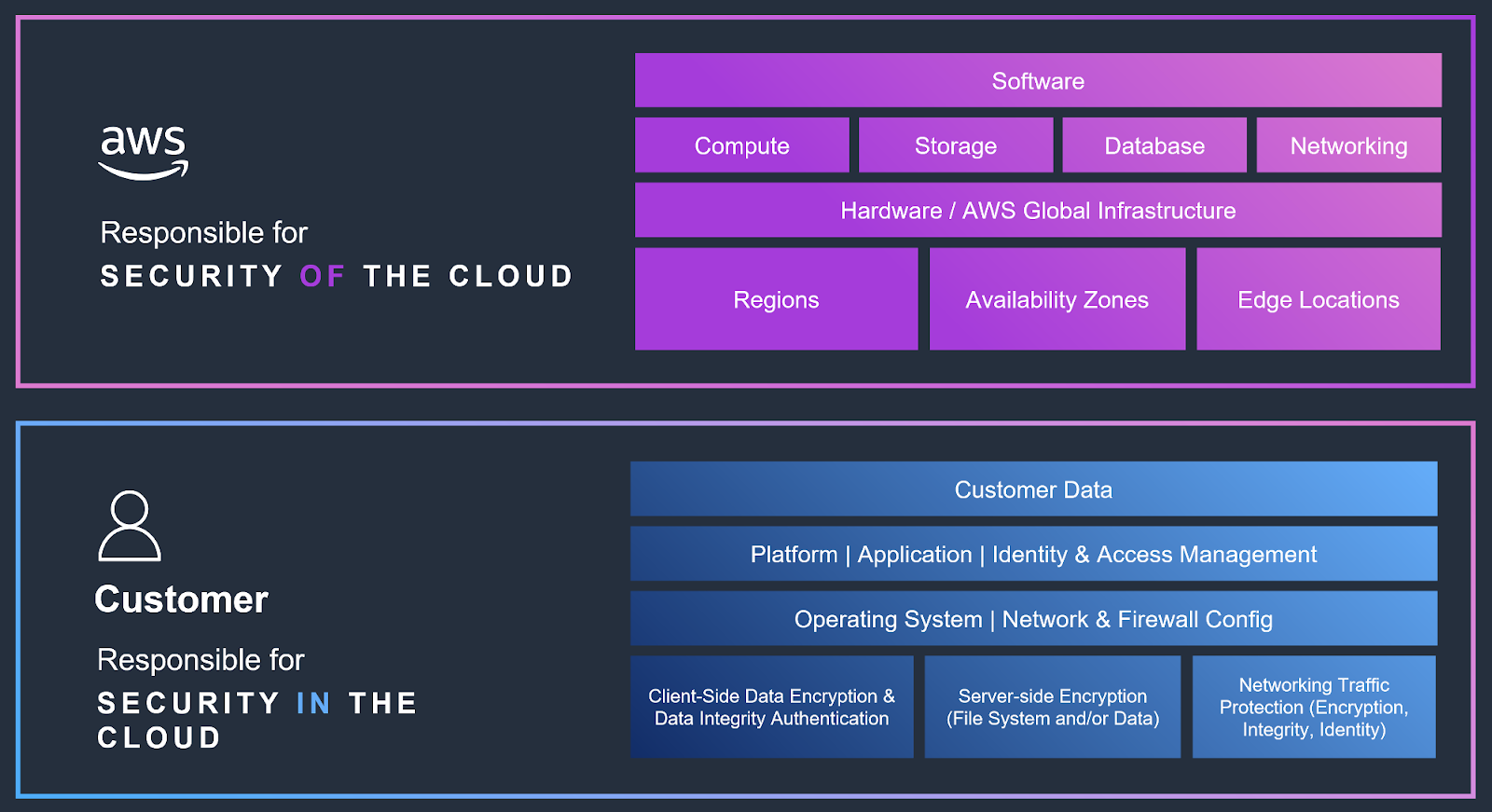
- Split responsibilities between AWS and customers under the Shared Responsibility Model.
- Use open source MCP server tools like AWS-IReveal-MCP to assist investigation and remediation.
- Organize AWS accounts with security and forensics OUs to enhance containment, evidence integrity, and auditability.
Read More: https://www.sysdig.com/blog/build-your-aws-incident-response-playbook-with-open-source-tools