A threat actor exploited a misconfigured Open WebUI system to upload and execute an AI-assisted malicious Python script, deploying cryptominers and infostealers on Linux and Windows environments. The attack used sophisticated evasion techniques, including processhider and argvhider, and a Discord webhook for command and control. #OpenWebUI #DiscordWebhook #processhider #argvhider #application-ref.jar
Keypoints
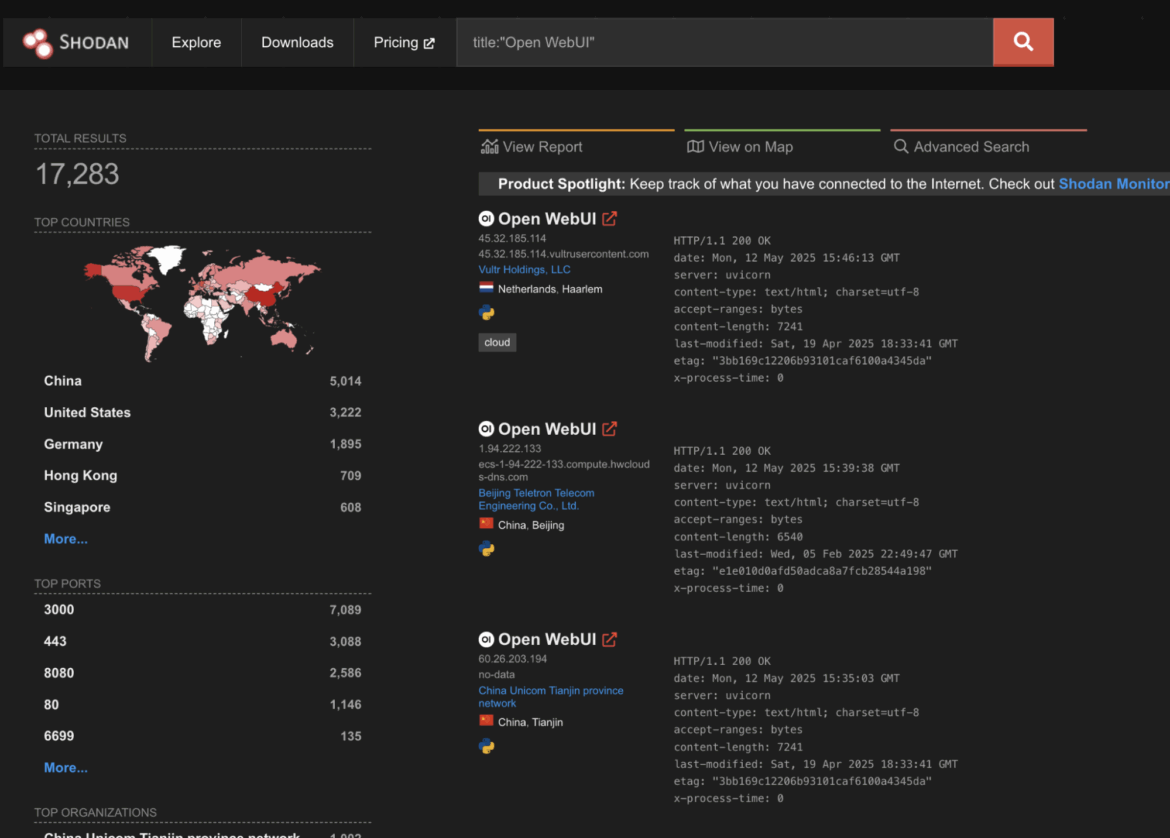
- Open WebUI was exposed to the internet with administrator access and no authentication, allowing attackers to execute malicious Python scripts.
- The attackers used an AI-generated Python script to download and execute cryptominers (T-Rex and XMRig) targeting Monero and Kawpow cryptocurrencies.
- Defense evasion techniques included compiling and loading inline C programs: processhider to hide the miner process and argvhider to hide process arguments.
- Persistence was achieved by installing a disguised systemd service named “ptorch_updater” to run the malicious script continuously.
- On Windows, the payload downloaded and executed a Java-based loader (application-ref.jar) with advanced evasion and infostealer capabilities involving DLLs and credential theft targeting Chrome extensions and Discord.
- The attacker utilized a Discord webhook for C2 communication to send victim system information.
- Sysdig Secure detected and blocked the attack via Yara rules for malicious shared objects and runtime threat intelligence on domain lookups and behavior.
MITRE Techniques
- [T1105] Ingress Tool Transfer – Attackers downloaded cryptominers and malicious JAR files from external URLs to the victim system. (“The script then downloads two cryptominers, T-Rex and XMRig” / “downloaded a Java-based loader from 185.208.159[.]155”)
- [T1547.001] Boot or Logon Autostart Execution: Systemd Service – Persistence was established by creating a systemd service ‘ptorchupdater’ to run the malicious Python script. (“uses a systemd service… ‘ptorchupdater’ to try to masquerade as a legitimate service”)
- [T1055] Process Injection – The payload used LDPRELOAD to load shared objects (processhider, argvhider) to hide miner processes and arguments from detection. (“compiled into shared objects and were loaded using LDPRELOAD”)
- [T1071.001] Application Layer Protocol: Web Protocols – Discord webhook was used for command and control communication. (“A Discord webhook was leveraged for command and control (C2)”)
- [T1027] Obfuscated Files or Information – The payload used multi-layer Base64 encoded and compressed Python code obfuscated with PyObfuscator (pyklump). (“The code is obfuscated using PyObfuscator… 64 layers deep”)
- [T1539] Steal Web Session Cookie – The infostealer component stole Discord authentication tokens by hijacking desktop_core.js. (“Malicious code… attempts to hijack Discord and steal the victim’s authentication token”)
- [T1555] Credentials from Password Stores – Attackers targeted Chrome extension credentials for theft. (“This malware contains packages that can be used for credential theft from Chrome extensions”)
Indicators of Compromise
- [SHA256 Hash] Malicious files – application-ref.jar (1e6349278b4dce2d371db2fc32003b56f17496397d314a89dc9295a68ae56e53), appbounddecryptor.dll (41774276e569321880aed02b5a322704b14f638b0d0e3a9ed1a5791a1de905db), background.properties (eb00cf315c0cc2aa881e1324f990cc21f822ee4b4a22a74b128aad6bae5bb971), and Initial Python Script (ec99847769c374416b17e003804202f4e13175eb4631294b00d3c5ad0e592a29)
- [URL] Malicious downloader URLs – http://185[.]208[.]159[.]155:8000/application-ref.jar, https://gh-proxy.com/https://github.com/xmrig/xmrig/releases/download/v6.22.2/xmrig-6.22.2-linux-static-x64.tar.gz, https://gh-proxy.com/https://github.com/trexminer/T-Rex/releases/download/0.26.8/t-rex-0.26.8-linux.tar.gz
- [Discord Webhook] C2 communication – https://canary.discord.com/api/webhooks/1357293459207356527/GRsqv7AQyemZRuPB1ysrPUstczqL4OIi-I7RibSQtGS849zY64H7W_-c5UYYtrDBzXiq
- [Wallet Address] Cryptocurrency wallets used – RavenCoin wallet: RHXQyAmYhj9sp69UX1bJvP1mDWQTCmt1id, Monero XMR wallet: 45YMpxLUTrFQXiqgCTpbFB5mYkkLBiFwaY4SkV55QeH2VS15GHzfKdaTynf2StMkq2HnrLqhuVP6tbhFCr83SwbWExxNciB
- [IP Address] Malicious host IP – 185.208.159[.]155 (used as payload hosting and JAR downloader)
Read more: https://sysdig.com/blog/attacker-exploits-misconfigured-ai-tool-to-run-ai-generated-payload/