A malspam campaign targeting Italy uses emails claiming to be from “Arabian Construction Co” to distribute AsyncRAT malware via a TAR archive containing obfuscated JavaScript and PowerShell scripts. The final payload is hidden inside a GIF file with Base64-encoded DLL code, which downloads and executes AsyncRAT after environment checks. #AsyncRAT #Remcos #Formbook #MassLogger #CERTAGID
Keypoints
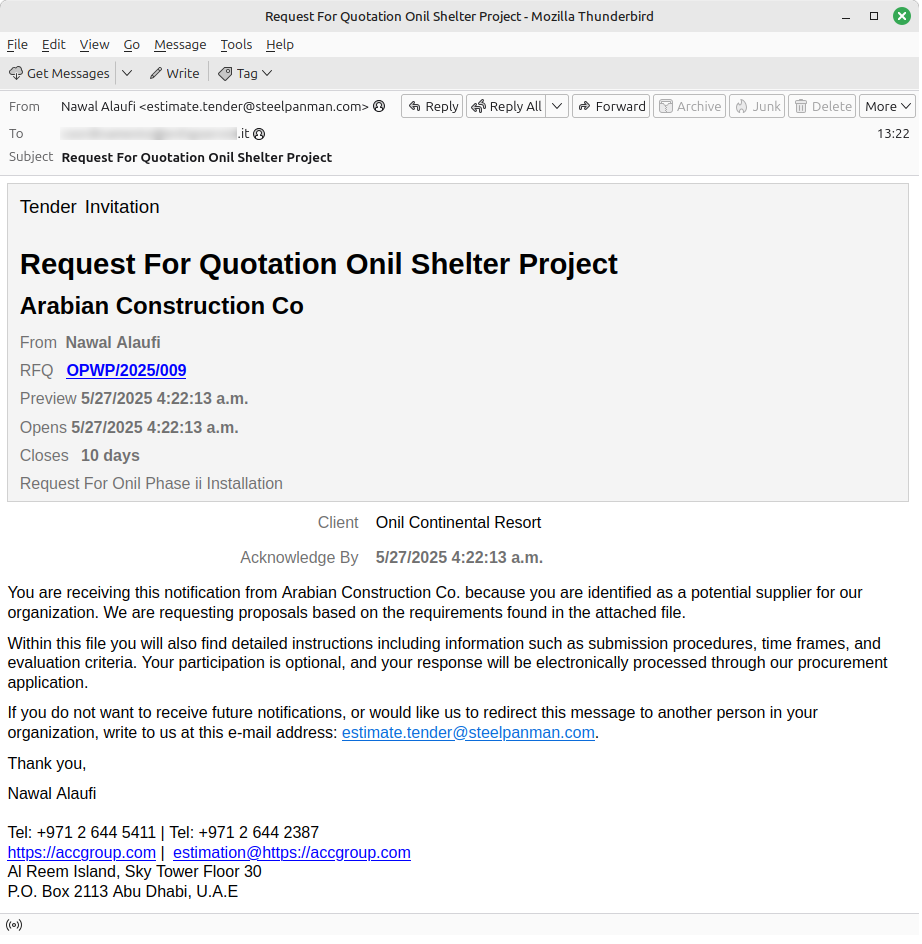
- The campaign uses emails in English pretending to be from Arabian Construction Co, inviting victims to access a TAR archive via a Box.com link.
- The TAR archive contains obfuscated JavaScript that executes PowerShell code to download additional components from Aruba Drive storage.
- A GIF file with embedded Base64-encoded code is used to deliver a DLL that performs environment checks before downloading the final AsyncRAT payload.
- AsyncRAT enables remote unauthorized access, data theft, and remote command execution on infected systems.
- The same GIF-based delivery method has been previously used to distribute other malware like Remcos, Formbook, Avemaria, and MassLogger.
- Collaboration with Aruba led to the takedown of the malicious resource, and IoCs were shared via CERT-AGID’s Feed IoC.
- Users are advised to exercise caution with suspicious emails and report them to [email protected] for analysis.
MITRE Techniques
- [T1566] Phishing – The campaign uses phishing emails pretending to be from Arabian Construction Co with links to malicious TAR archives (“email pretending to be from Arabian Construction Co inviting the victim… to consult information in the attached file”).
- [T1204] User Execution – The victim must click the link to download and execute the malicious TAR archive containing obfuscated JavaScript (“TAR archive includes obfuscated JavaScript that executes PowerShell code”).
- [T1059] Command and Scripting Interpreter – PowerShell scripts are used to download the DLL and final AsyncRAT payload (“PowerShell designed to download a resource from Aruba Drive”).
- [T1036] Masquerading – The use of a GIF file with embedded Base64-encoded code to hide the DLL payload (“The file obtained is a GIF containing Base64-encoded code inside specific tags”).
- [T1083] File and Directory Discovery – The DLL checks the environment including virtual machine presence before executing (“After checks on the machine including verification of Virtual Machine presence, the DLL downloads and executes the final payload”).
- [T1105] Ingress Tool Transfer – The final AsyncRAT malware is downloaded from a remote URL after initial payload execution (“The DLL downloads and executes the final sample, AsyncRAT”).
Indicators of Compromise
- [URL] Malicious download links – Box.com TAR archive link, Aruba Drive storage URL used to deliver payloads.
- [File Name] Malicious files – obfuscated JavaScript in TAR archive, Base64 encoded GIF file containing DLL payload.
- [Email] Phishing sender impersonation – emails claiming to be from “Arabian Construction Co”.
Read more: https://cert-agid.gov.it/news/asyncrat-distribuito-in-italia-tramite-componenti-steganografici/