The threat actor exploited the CVE-2023-22527 vulnerability in an internet-facing Atlassian Confluence server to gain initial access, followed by privilege escalation, credential harvesting, lateral movement, and deployment of the ELPACO-team Mimic ransomware after approximately 62 hours. Despite ransomware deployment and log deletion, no significant data exfiltration was observed during the intrusion targeting enterprise networks. #AtlassianConfluence #ELPACOransomware
Keypoints
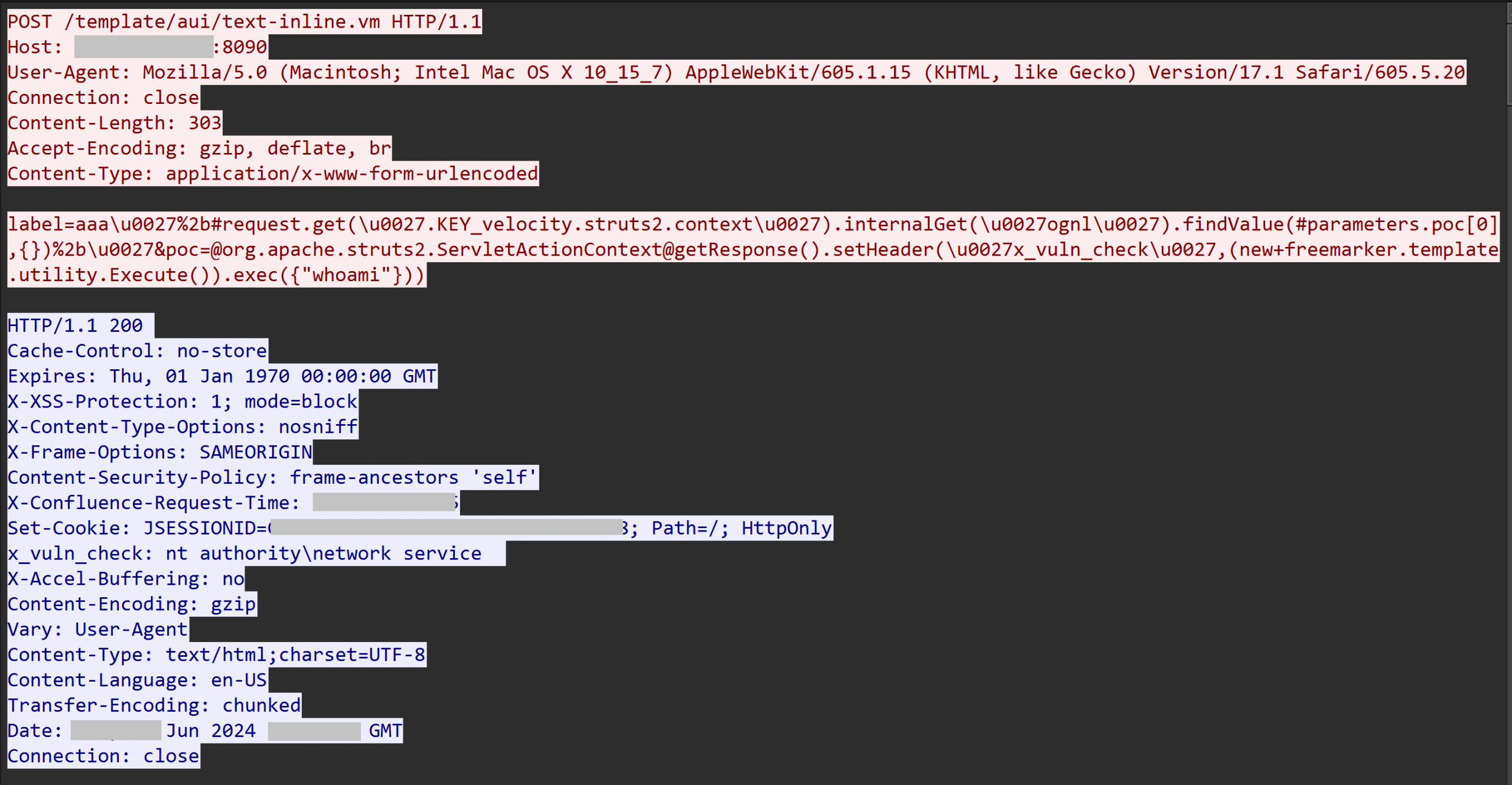
- The attacker gained initial access by exploiting the template injection vulnerability CVE-2023-22527 on an unpatched Atlassian Confluence server.
- Multiple Metasploit loaders and a Meterpreter payload were deployed via remote code execution, followed by AnyDesk installation for persistent remote access.
- Privilege escalation was achieved using the Named Pipe Impersonation (RPCSS variant) technique, enabling SYSTEM-level access and creation of local admin accounts.
- Credential harvesting tools such as Mimikatz, ProcessHacker, and Impacket Secretsdump were used to compromise domain administrator credentials.
- Network discovery and lateral movement were conducted through SMB share enumeration, Netscan, wmiexec, and RDP connections targeting domain controllers, backup, and file servers.
- The threat actor deployed ELPACO-team.exe, a Mimic ransomware variant, approximately 62 hours after initial exploitation to encrypt multiple servers with minimal prior data exfiltration.
- Defensive measures like disabling Windows Defender and modifying firewall settings were executed to maintain persistence and evade detection.
MITRE Techniques
- [T1190] Exploit Public-Facing Application – Exploited CVE-2023-22527 in Confluence to execute arbitrary commands (“The threat actor first gained entry by exploiting a known vulnerability (CVE-2023-22527) on an internet-facing Confluence server…”).
- [T1543.003] Windows Service – Installed and ran AnyDesk as a Windows service for persistence (“This initial AnyDesk binary was then executed via the command line… to install AnyDesk on the system as a service…”).
- [T1136] Create Account – Created local and domain accounts (“created a new user account named ‘noname’ with the password ‘Slepoy_123’…”).
- [T1068] Exploitation for Privilege Escalation – Used Named Pipe Impersonation (RPCSS variant) to escalate privileges to SYSTEM (“The final method observed, which worked, was the Named Pipe Impersonation (RPCSS Variant)…”).
- [T1003.001] LSASS Memory – Harvested credentials by dumping LSASS memory with Mimikatz (“The mimikatz.exe process accessed the Local Security Authority Subsystem Service (lsass.exe) to access credentials…”).
- [T1047] Windows Management Instrumentation – Used wmiexec.exe for lateral movement and executing commands remotely (“Leveraging the compromised domain administrator credentials… utilizing Impacket wmiexec…”).
- [T1021.001] Remote Desktop Protocol – Established RDP connections to remote servers for lateral movement (“…using RDP to move laterally to a file server as well as a backup server…”).
- [T1105] Ingress Tool Transfer – Transferred tools such as Mimikatz, ProcessHacker, and Netscan onto compromised hosts (“The threat actor dropped tools focused on credential access, including Mimikatz, ProcessHacker…”).
- [T1562.001] Disable or Modify Tools – Used Defender Control to disable Windows Defender (“…executed Defender Control, an executable… to stop Windows Defender Antivirus Service…”).
- [T1562.004] Disable or Modify System Firewall – Modified firewall rules to allow RDP connections (“…adjusted Windows Firewall settings using netsh advfirewall commands…”).
- [T1486] Data Encrypted for Impact – Deployed ELPACO-team ransomware variant to encrypt files (“…deployed ELPACO-team.exe, identified as a variant of Mimic ransomware…”).
- [T1071] Application Layer Protocol – Used raw TCP sockets for Metasploit C2 communication (“The Command and Control traffic to the Metasploit server used raw TCP sockets…”).
- [T1112] Modify Registry – Modified registry keys to persist and enable features like RDP and disable Defender (“…setting the value of the registry Windows Run key… as well as disabling Defender…”).
- [T1012] Query Registry – Queried registry to discover configured RDP port and settings (“…querying the registry to identify the configured RDP port…”).
- [T1057] Process Discovery – Used enumeration commands to identify running processes and environment details (“Many of the discovery commands were issued as a direct result of the initial Confluence exploit…”).
- [T1059.003] Windows Command Shell – Executed batch files and shell commands such as u1.bat to add users and enable services (“…batch file u1.bat… to create a new user account and make it a local admin…”).
- [T1219] Remote Access Software – Used AnyDesk for interactive remote access sessions (“The threat actor used AnyDesk’s Direct Connection feature…”).
Indicators of Compromise
- [IP Address] Initial exploit and C2 servers – 45.227.254.124, 91.191.209.46 used for Confluence exploitation and Metasploit C2.
- [File Hash] Ransomware and tools – elpaco-team.exe (various hashes including 0b83f2667abff814bb724808c404396e6ad417591165f1762a8e99ec108d4996), secretsdump.exe (96ec8798bba011d5be952e0e6398795d), mimikatz.exe and other related credential dumping binaries.
- [File Name] Scripts and utilities – u1.bat (user creation script), checkvuln.bat (PrintNightmare discovery), wmiexec.exe (remote code execution), netscan.exe (network discovery), and defendercontrol.exe (disables Defender).
- [Domain/File Path] Suspicious DLLs and files – spider.dll and spider_32.dll used to create hidden admin accounts; nbjlop.dll and other randomly named DLLs dropped by Metasploit loader in temp folders.
- [Network] AnyDesk server and direct connection on port 443 at 45.227.254.124; Metasploit C2 communication on TCP port 12385 to 91.191.209.46.