TeamPCP ran a coordinated supply chain campaign that abused trusted CI/CD and release workflows in the Checkmarx KICS, Bitwarden CLI, and elementary-data incidents to steal credentials at scale. The campaign used poisoned Docker Hub, VS Code/OpenVSX, GitHub Actions, PyPI, and GHCR artifacts, plus live AWS secret enumeration and GitHub commit-search dead drops to exfiltrate data. #TeamPCP #Checkmarx #KICS #Bitwarden #elementary-data #PyPI #GHCR
Keypoints
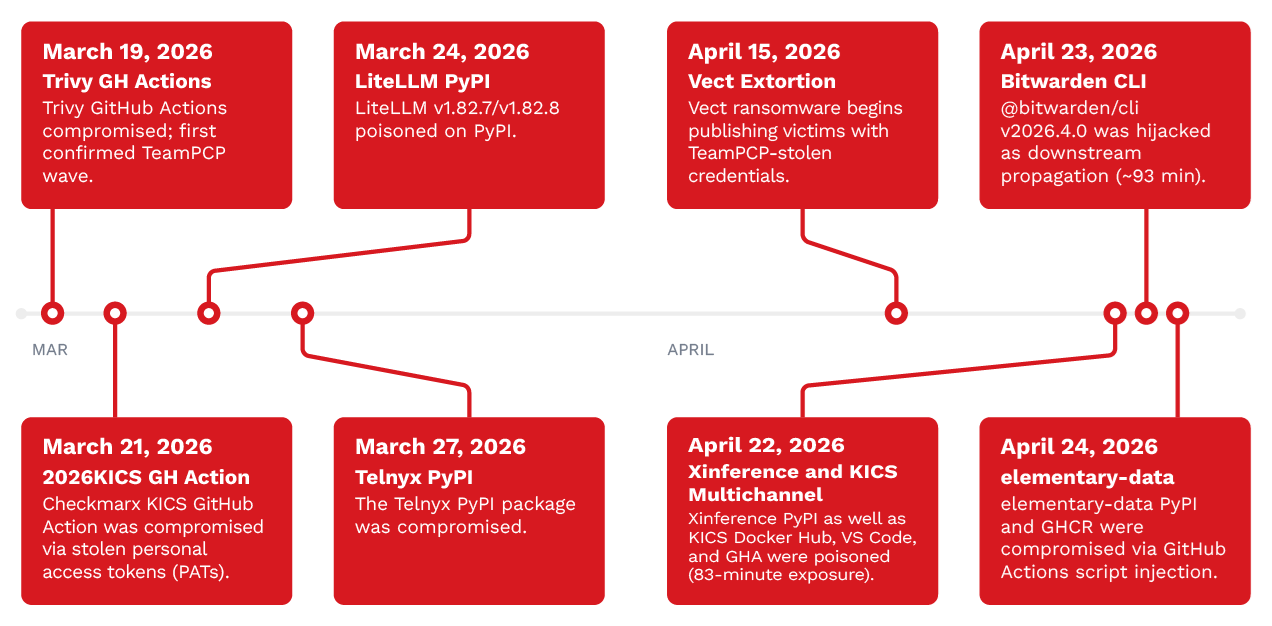
- TeamPCP conducted at least seven supply chain attack waves from March 19 to April 24, 2026.
- The April 22 KICS incident poisoned Docker Hub, VS Code/OpenVSX, and GitHub Actions, then hijacked @bitwarden/cli using stolen npm tokens.
- The April 24 elementary-data incident used a single GitHub PR comment to trigger GitHub Actions script injection and a malicious signed release.
- The campaign’s main goal was credential theft, targeting GitHub PATs, npm tokens, cloud credentials, SSH keys, Kubernetes secrets, database secrets, and wallet keystores.
- The elementary-data payload also performed live AWS API calls to enumerate and retrieve secrets from Secrets Manager and SSM Parameter Store.
- Actor branding was embedded across payloads through Session messenger IDs, Dune-themed repository names, and custom exfiltration headers.
- Recommended defenses include digest pinning, least privilege, egress restrictions on CI runners, and auditing GitHub Actions for unsanitized user-controlled input.
MITRE Techniques
- [T1195.002] Supply Chain Compromise: Compromise Software Supply Chain – The actor poisoned trusted distribution channels and release workflows across Docker Hub, VS Code/OpenVSX, PyPI, GHCR, and GitHub Actions (‘Poisoned Docker Hub images, VS Code extensions, PyPI packages, and GitHub Actions across both incidents’).
- [T1078] Valid Accounts – Stolen publisher credentials were used to republish compromised artifacts in the KICS case (‘stolen publisher credentials used for Docker Hub, VS Code, and GitHub Action republish’).
- [T1199] Trusted Relationship – GitHub Actions runner trust was abused through pull request comment injection in elementary-data (‘GitHub Actions runner token abused through PR comment script injection’).
- [T1059.007] Command and Scripting Interpreter: JavaScript – The KICS payload executed JavaScript via the Bun runtime on the victim system (‘mcpAddon.js executed via Bun runtime on the victim system’).
- [T1059.006] Command and Scripting Interpreter: Python – The elementary-data .pth payload executed when Python started (‘elementary-data .pth payload executed at Python interpreter startup’).
- [T1059.004] Command and Scripting Interpreter: Unix Shell – The injected command in GitHub Actions launched a shell stager (‘GitHub Actions runner executes shell stager after comment injection’).
- [T1547] Boot or Logon Autostart Execution – The .pth file caused code to run on every Python interpreter startup (‘elementary-data .pth fires on every Python interpreter startup on the host’).
- [T1027] Obfuscated Files or Information – Both payloads used encryption or XOR-based hiding to hinder analysis (‘KICS payload uses AES-256-GCM + RSA OAEP-SHA256; elementary-data uses MD5-keystream XOR’).
- [T1070.004] Indicator Removal: File Deletion – Temporary-directory cleanup removed artifacts after execution (‘temporary-directory context manager to delete trin.tar.gz on exit’).
- [T1552.001] Unsecured Credentials: Credentials In Files – Both payloads harvested secrets from files on disk (‘Both payloads harvest SSH keys, cloud credential files, and developer tokens from disk’).
- [T1552.005] Unsecured Credentials: Cloud Instance Metadata API – The stealer queried cloud metadata services for credentials (‘queries EC2 IMDS v2 and ECS task credential endpoints’).
- [T1528] Steal Application Access Token – The attacker abused the GitHub Actions GITHUB_TOKEN to forge a release commit (‘GITHUB_TOKEN abused to forge release commit’).
- [T1526] Cloud Service Discovery – The payload enumerated AWS Secrets Manager and SSM entries (‘secretsmanager:ListSecrets and ssm:DescribeParameters live enumeration’).
- [T1613] Container and Resource Discovery – Kubernetes secrets were enumerated from the runner environment (‘kubectl get secrets –all-namespaces enumeration’).
- [T1005] Data from Local System – The malware collected local credential files, shell history, and config files (‘Credential files, shell history, AI and MCP configuration files harvested’).
- [T1530] Data from Cloud Storage – The payload retrieved plaintext secrets from cloud secret stores (‘secretsmanager:GetSecretValue retrieves plaintext secrets’).
- [T1071.001] Application Layer Protocol: Web Protocols – Exfiltration used HTTPS to actor-controlled infrastructure (‘HTTPS exfiltration to actor-controlled C&C endpoints in both incidents’).
- [T1102.001] Dead Drop Resolver – GitHub commit-search was used to recover fallback C&C domains (‘use GitHub commit-search API to recover fallback C&C domains’).
- [T1041] Exfiltration Over C2 Channel – Encrypted archives were posted to C2 over HTTPS (‘POST encrypted credential archives over HTTPS to the primary C&C endpoint’).
- [T1567] Exfiltration Over Web Service – Stolen data was also dead-dropped into public GitHub repositories (‘auto-created public GitHub repositories under Dune-themed names’).
- [T1657] Financial Theft – Cryptocurrency wallet keystores were targeted as part of the credential theft (‘Cryptocurrency wallet harvesting observed in the elementary-data payload’).
Indicators of Compromise
- [Docker image tags ] KICS compromise and downstream exposure – checkmarx/kics:alpine, checkmarx/kics:latest, and other poisoned tags such as v2.1.20
- [VS Code/OpenVSX extension versions ] poisoned extension distribution – cx-dev-assist v1.17.0, ast-results v2.66.0, and other affected extension versions
- [GitHub Actions workflow/repo names ] compromised CI workflow and release paths – checkmarx/ast-github-action, format-check.yml, update_pylon_issue.yml, and workflow_dispatch tag=v0.23.3
- [Python package versions ] malicious package release – elementary-data==0.23.3, elementary-data==0.23.4 (safe follow-up), and the malicious .pth payload
- [Container registry references ] malicious container distribution – ghcr[.]io/elementary-data/elementary:0[.]23[.]3 and :latest
- [File names ] payload and cleanup artifacts – mcpAddon.js, elementary.pth, trin.tar.gz, and .trinny-security-update
- [Custom HTTP headers ] actor-branded exfiltration markers – X-Rise-To-The-Trinny: agree, X-Filename: tpcp.tar.gz, and X-QT-SR: 14
- [Repository naming pattern ] dead-drop staging repositories – Dune-themed names following the — pattern such as sardaukar-fremen-###, with description Shai-Hulud: The Third Coming
- [Session identifier marker ] cross-campaign decryption/contact key – reused Session messenger identifier embedded in multiple payloads
- [C2 infrastructure ] actor-controlled exfil and fallback endpoints – Checkmarx-impersonating C&C domains, Cloudflare-fronted IPs, and GitHub commit-search dead-drop infrastructure
Read more: https://www.trendmicro.com/en_us/research/26/e/analyzing-teampcp-supply-chain-attacks.html